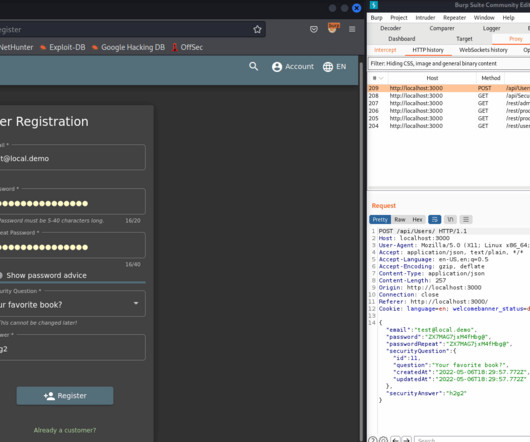
Free Unsolicited Smartwatch in the Mail and I’m in the Military? What Could Possibly Go Wrong???
KnowBe4
JULY 7, 2023
From the “shaking our heads” files comes the story of how threat actors compromised military personnel mobile devices, credentials, accounts and more.


























Let's personalize your content