OnDemand | 2021 Pharmaceutical Threat Outlook
Data Breach Today
JANUARY 5, 2021
Thwarting Mobile Phishing
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Data Breach Today
JANUARY 5, 2021
Thwarting Mobile Phishing
Security Affairs
MAY 3, 2024
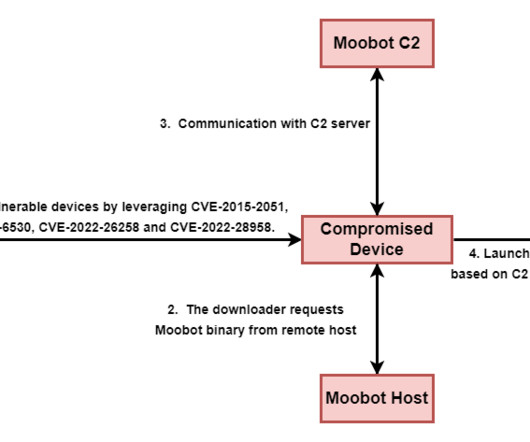
The threat actors used the botnet harvest credentials, collect NTLMv2 digests, proxy network traffic, and host spear-phishing landing pages and custom tools. The Moobot botnet has been active since at least 2016, it also includes other routers and virtual private servers (VPS). ” reported Trend Micro. ” reported Trend Micro.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
OCTOBER 17, 2020
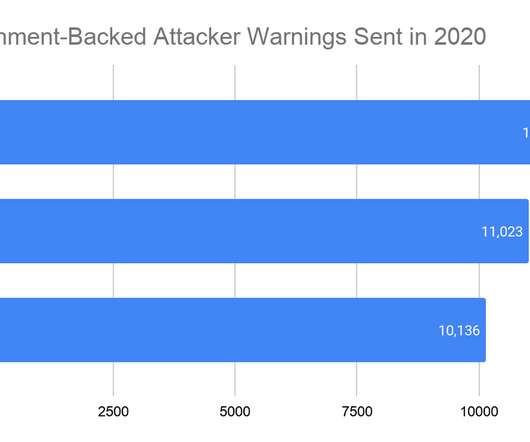
Google delivered 33,015 alerts to its users during the first three quarters of 2020 to warn them of phishing attacks, launched by nation-state actors, targeting their accounts. Google sent 11,856 government-backed phishing warnings during Q1 2020, 11,023 in Q2 2020, and 10,136 in Q3 2020. Tbps, the largest DDoS attack of ever.

Security Affairs
DECEMBER 18, 2020
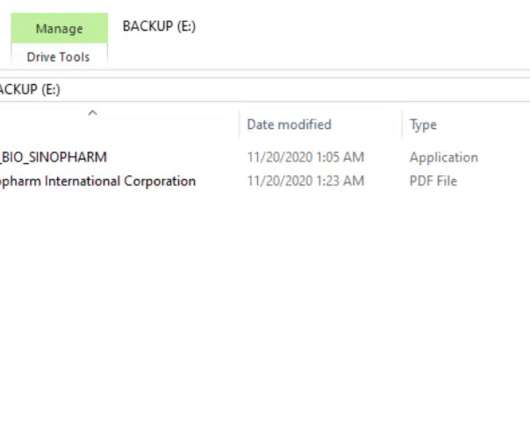
Cybercrime organizations continue to be very active while pharmaceutical organizations are involved in the development of a COVID-19 vaccine and medicines to cure the infections. The experts uncovered a large scale spear-phishing campaign that has been ongoing since September 2020. ” continues the report.
Security Affairs
DECEMBER 25, 2020
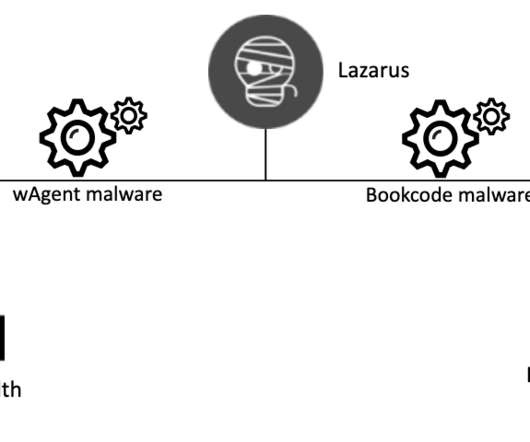
The attacks aimed at a Ministry of Health and a pharmaceutical company involved in the development of the COVID-19 vaccine. The systems at the pharmaceutical company were targeted with the BookCode malware, while in the attack against a Ministry of Health the APT group used the wAgent malware. .
Security Affairs
DECEMBER 10, 2020
Russia-link cyberespionage APT28 leverages COVID-19 as phishing lures to deliver the Go version of their Zebrocy (or Zekapab) malware. Russia-linked APT28 is leveraging COVID-19 as phishing lures in a new wave of attacks aimed at distributing the Go version of their Zebrocy (or Zekapab) malware. ” concludes the report.

Security Affairs
JUNE 9, 2020
Researchers from the IBM X-Force Incident Response and Intelligence Services (IRIS) reported that attackers launched a COVID-19-themed spear-phishing campaign to steal the user credentials of over 100 senior executives. The phishing messages originating from a Russia-based IP address 178[.]159[.]36[.]183, Pierluigi Paganini.
Security Affairs
JANUARY 18, 2022
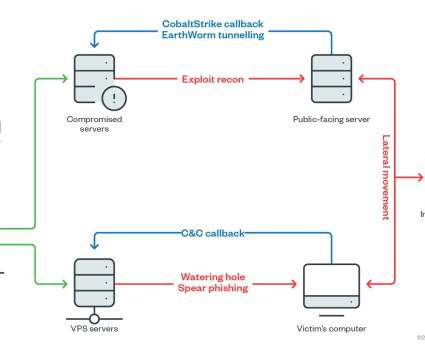
Trend Micro researchers spotted an elusive threat actor, called Earth Lusca, that targets organizations worldwide via spear-phishing and watering hole attacks. . The APT group targeted organizations in various industries, including the aviation, gaming, pharmaceuticals, technology, telecoms, and software development industries.

Security Affairs
NOVEMBER 13, 2020
“The targets include leading pharmaceutical companies and vaccine researchers in Canada, France, India, South Korea and the United States. Zinc APT targeted the centers with spear-phishing campaigns aimed at employees working at the targeted companies using messages pretending to be sent by recruiters.

Security Affairs
OCTOBER 18, 2020
Since August, FIN11 started targeting organizations in many industries, including defense, energy, finance, healthcare, legal, pharmaceutical, telecommunications, technology, and transportation. Researchers from FireEye’s Mandiant observed FIN11 hackers using spear-phishing messages distributing a malware downloader dubbed FRIENDSPEAK.
Security Affairs
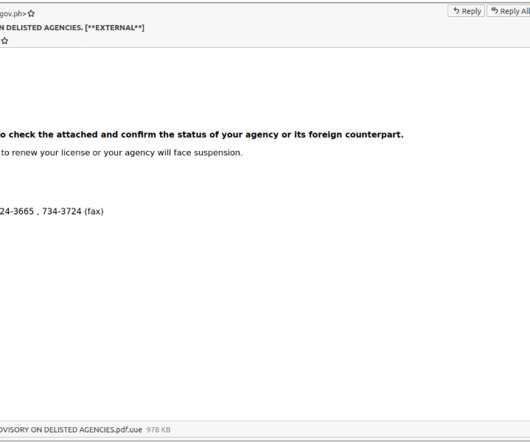
NOVEMBER 1, 2021
The group focuses on Shipping/Logistics, Manufacturing, Business Services, Pharmaceutical, and Energy entities, among others. The threat actors carried out spear-phishing attacks using spoofed email addresses. Victims of the group are located in North America, Europe, and Southeast Asia. .

Security Affairs
NOVEMBER 4, 2021
The ransomware operators used the Emotet distribution service in 2020 and TA551 in 2020 and 2021 to distribute QakBot via phishing email. CERT-FR published a detailed report on the activity of the Lockean ransomware gang that has been active since June 2020. ” reads the report published by CERT-FR.

Threatpost
NOVEMBER 17, 2020
After the breakout of the COVID-19 pandemic, mobile phishing attacks targeting pharmaceutical companies have shifted their focus from credential theft to malware delivery.

Security Affairs
DECEMBER 5, 2021
Hundreds of vulnerabilities in common Wi-Fi routers affect millions of users German BSI agency warns of ransomware attacks over Christmas holidays Cuba ransomware gang hacked 49 US critical infrastructure organizations CISA warns of vulnerabilities in Hitachi Energy products NSO Group spyware used to compromise iPhones of 9 US State Dept officials (..)

IT Governance
MAY 16, 2019
Earlier this month, two major pharmaceutical giants issued warnings about phishing emails targeting job hunters. Unfortunately, red flags like that are ignored in all kinds of phishing scams, and this scheme is a perfect example of why that happens. Can you spot a phishing scam?

Security Affairs
DECEMBER 21, 2018
In July 2018, FireEye observed a series of new attacks of the group leveraging spear-phishing emails using weaponized Word documents that attempt to deliver the UPPERCUT backdoor, also tracked as ANEL. Department of Energy’s Lawrence Berkeley National Laboratory. ” continues the DoJ’s Press release.

KnowBe4
SEPTEMBER 28, 2023
Insights from IBM’s Cost of a Data Breach Report on the Pharmaceutical Industry shows that while the overall cost has improved, there are clear areas of risk that need to be addressed.

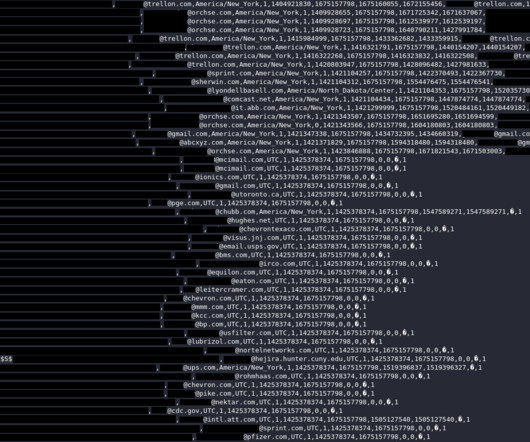
Troy Hunt
NOVEMBER 13, 2024
I would like to opt-out of here to reduce the SPAM and Phishing emails. That last one seems perfectly reasonable, and fortunately, DemandScience does have a link on their website to Do Not Sell My Information : Dammit! If, like me, you're part of the 99.5%

The Last Watchdog
OCTOBER 8, 2018
And by compromising activities on the IT side, stealing credentials, deploying phishing emails, and infecting websites with drive-by malware, criminals can infiltrate the OT network. With more connectivity between OT and IT the attack surface is broadened. Their intent is to disrupt society and establish power.
IT Governance
DECEMBER 1, 2020
Ransomware.

IT Governance
SEPTEMBER 21, 2020
For example, the pharmaceutical giant AstraZeneca, which is based in Cambridge, was last year imitated in a sophisticated phishing scam targeting job seekers. Unfortunately, these sectors are especially prone to cyber attacks due to the sensitive information that they keep.

The Last Watchdog
JUNE 20, 2023
•Use Only Official Websites : Using official airline and hotel apps for updates and notifications is much safer than relying on emails to reduce the risk of falling prey to phishing attempts. “Do not let the menace of cyber criminals overshadow a well-earned leisure time,” said Eitan Fogel, CEO of CybeReady.

Threatpost
OCTOBER 20, 2020
Hundreds of medical patients taking cancer drugs, Premarin, Lyrica and more are now vulnerable to phishing, malware and identity fraud.
IT Governance
DECEMBER 1, 2021
Community Medical Centers, Inc.

eSecurity Planet
OCTOBER 26, 2021
“They find a way in, whether it’s phishing or something else – but then to find all the valuable assets, they have to use lateral movements in those environments,” Kirner said. “And we stop that lateral movement.” ” One way to visualize that process, Kirner said, is to picture a submarine.

The Last Watchdog
FEBRUARY 28, 2021
Cybercriminals often leverage social engineering tactics like phishing and spear-phishing to propagate sophisticated malware. It was undisputedly the fastest spreading, most destructive worm that crippled hospitals, multinational companies and pharmaceutical giants globally by irreversibly encrypting systems’ master boot records.

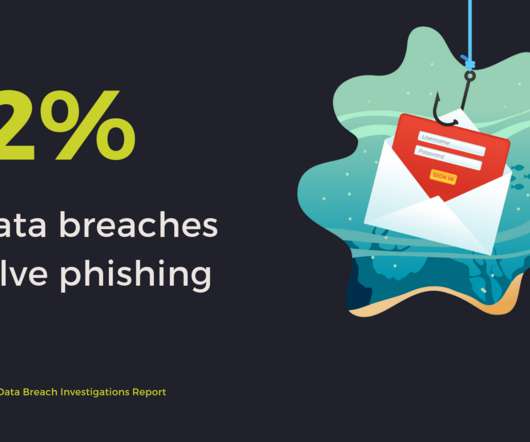
eSecurity Planet
AUGUST 11, 2021
A 2020 report showed how three out of four phishing attempts targeting pharmaceutical employees also delivered malware to victims. Some provide additional scanning to prevent or limit the risk of phishing, and some provide permissions warnings when an app is attempting to do something that requires more permissions than it should.

eSecurity Planet
JUNE 30, 2023
TA505 is well-known for its involvement in global phishing and malware dissemination. Their victims include hundreds of companies worldwide, and they engage in various illegal activities, including providing ransomware-as-a-service, acting as an initial access broker, and orchestrating large-scale phishing assaults and financial fraud.

IT Governance
MAY 4, 2021
discloses security incident (unknown) St. discloses security incident (unknown) St. discloses security incident (unknown) St.

IT Governance
SEPTEMBER 1, 2020
Cyber attacks. million) CO-based Mental Health Partners says an employee’s account was hacked (unknown) Sumitomo Forestry Co., Hitachi Chemical Co. Data breaches.

IT Governance
JUNE 1, 2021
Luke’s Healthcare says patient data was accessed by unauthorised person (17,655) Belgium’s parliament and universities hit by cyber attack (unknown) Orthopedic Associates of Dutchess County notifies patients of breach (331,376) CaptureRx issues notice after discovering security incident (1,919,938) SEIU 775 Benefits Group discloses security incident (..)

IT Governance
MAY 2, 2023
Culbertson Memorial Hospital working to recover from cyber security incident (unknown) Rogers Communications data allegedly sold on a hacker forum (unknown) NZZ has to shut down the newspaper production system after a cyber attack (unknown) Southern California’s San Bernardino County Sheriff’s Department said it experienced a “network disruption” (unknown) (..)

IBM Big Data Hub
FEBRUARY 14, 2024
Pharmaceuticals For the life sciences industry, drug discovery and production require an immense amount of data collection, collation, processing and analysis. Gear up robotics AI is not just about asking for a haiku written by a cat. Robots handle and move physical objects.
Security Affairs
AUGUST 31, 2023
User Table Schema | Source: Cybernews As a huge number of emails were leaked, platform users could potentially experience a surge in spam and phishing emails. It’s advisable for them to externally verify the information contained in emails and exercise caution when clicking links or opening attachments. Are the leaked passwords crackable?

ForAllSecure
NOVEMBER 18, 2021
Let's say phishing campaigns like very compelling phishing campaigns, targeted ones. This all is beginning to sound like a classic arms race. Macorin: that's ultimately where it's going to go. We've seen machine learning platforms being used by adversaries in order to automate.

ForAllSecure
APRIL 26, 2022
This is ransomware, starting with a phishing attack. Building Automation controllers from you know the leading manufacturers at your hospital than you do in your skyscraper or your pharmaceutical plant. So your pharmaceutical plants have clean rooms. So this power grid attack is sounding more credible. Here’s Robert M.

Security Affairs
NOVEMBER 23, 2018
The researchers of Yoroi ZLab, on 16 November, accessed to a new APT29’s dangerous malware which seems to be involved in the recent wave of attacks aimed at many important US entities, such as military agencies, law enforcement, defense contractors , media companies and pharmaceutical companies.

Security Affairs
NOVEMBER 19, 2018
The researchers of Yoroi ZLab, on 16 November, accessed to a new APT29’s dangerous malware which seems to be involved in the recent wave of attacks aimed at many important US entities, such as military agencies, law enforcement, defense contractors , media companies and pharmaceutical companies. cybersecurity firm FireEye.
Security Affairs
MARCH 3, 2024
Private Plane Owners’ Data Linked to LA Intl. Private Plane Owners’ Data Linked to LA Intl.

Security Affairs
NOVEMBER 10, 2024
CISA adds PTZOptics camera bugs to its Known Exploited Vulnerabilities catalog Canadian authorities arrested alleged Snowflake hacker Android flaw CVE-2024-43093 may be under limited, targeted exploitation July 2024 ransomware attack on the City of Columbus impacted 500,000 people Nigerian man Sentenced to 26+ years in real estate phishing scams Russian (..)
IT Governance
JANUARY 30, 2020
You can find detailed breakdowns of some of the more notable incidents by subscribing to our Weekly Round-up or by visiting our blog (where we have a dedicated series on phishing scams ). in phishing scam (unknown). Russian agents reportedly phished organisation at the centre of Trump impeachment scandal (unknown).
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content