GUEST ESSAY: The key differences between ‘information privacy’ vs. ‘information security’
The Last Watchdog
JUNE 12, 2023
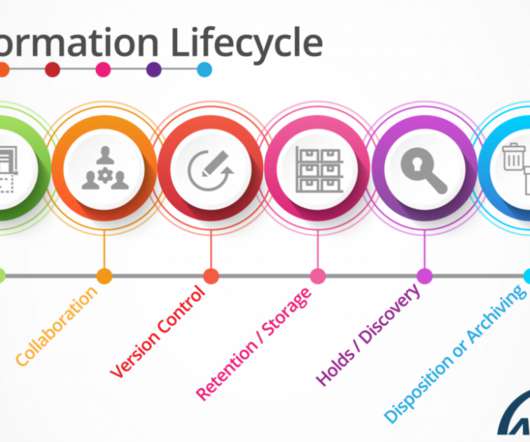
Information privacy and information security are two different things. Related: Tapping hidden pools of security talent Information privacy is the ability to control who (or what) can view or access information that is collected about you or your customers.





































Let's personalize your content