Cybersecurity Awareness Month: Resilient Multi-factor Authentication (MFA) and Strong Passwords
Thales Cloud Protection & Licensing
OCTOBER 4, 2022
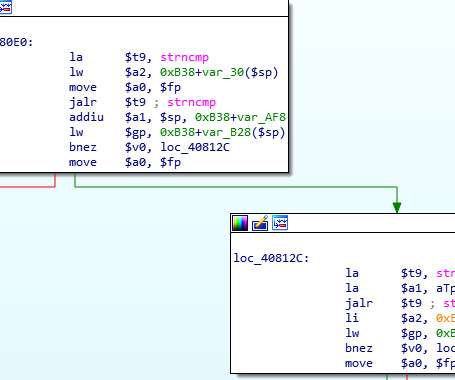
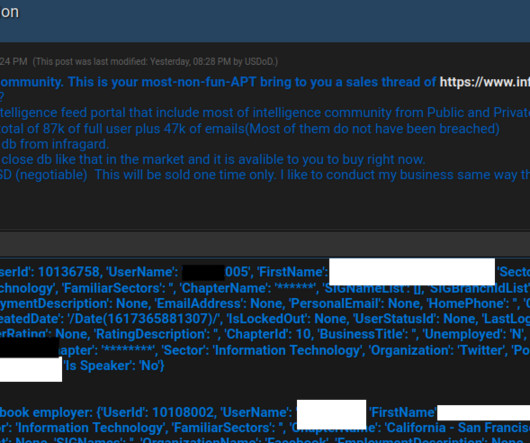
Cybersecurity Awareness Month: Resilient Multi-factor Authentication (MFA) and Strong Passwords. Historically, October has always been an important month for the cybersecurity community and a month of major cybersecurity events. Use strong passwords. Resilient multi-factor authentication and strong passwords are critical.









































Let's personalize your content