MY TAKE: What everyone should know about the promise and pitfalls of the Internet of Things
The Last Watchdog
SEPTEMBER 19, 2019

The Last Watchdog
SEPTEMBER 19, 2019

Dark Reading
SEPTEMBER 18, 2019
Social engineering is as old as mankind. But its techniques have evolved with time. Here are the latest tricks criminals are using to dupe end users.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Matters
SEPTEMBER 19, 2019
For years, companies seeking to block web scrapers from collecting the information on their website would invoke the Computer Fraud and Abuse Act (CFAA), a U.S. law that criminalizes accessing a computer “without authorization.” But the U.S. Court of Appeals for the Ninth Circuit has now ruled that merely instructing scrapers that they are not welcome on a public website, either through a restrictive terms of use or a cease-and-desist letter, is probably not enough to render their access “unauth

Thales Cloud Protection & Licensing
SEPTEMBER 19, 2019
Data is the most valuable online currency a consumer possesses. Yet most people don’t trust the companies they’re sharing data with, according to a new market trends study published by Gartner. In fact, 75% of consumers worry their online accounts may be hacked and the vast majority also believe companies are using or sharing their data without even telling them, according to the study.
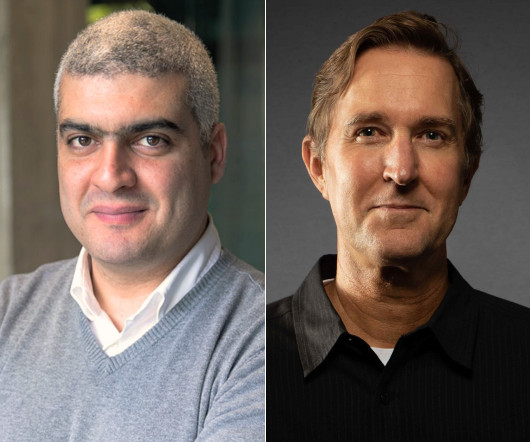
Speaker: Maher Hanafi, VP of Engineering at Betterworks & Tony Karrer, CTO at Aggregage
Executive leaders and board members are pushing their teams to adopt Generative AI to gain a competitive edge, save money, and otherwise take advantage of the promise of this new era of artificial intelligence. There's no question that it is challenging to figure out where to focus and how to advance when it’s a new field that is evolving everyday. 💡 This new webinar featuring Maher Hanafi, CTO of Betterworks, will explore a practical framework to transform Generative AI prototypes into

Troy Hunt
SEPTEMBER 17, 2019
Allow me to be controversial for a moment: arbitrary password restrictions on banks such as short max lengths and disallowed characters don't matter. Also, allow me to argue with myself for a moment: banks shouldn't have these restrictions in place anyway. I want to put forward cases for both arguments here because seeing both sides is important. I want to help shed some light on why this practice happens and argue pragmatically both for and against.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Krebs on Security
SEPTEMBER 18, 2019
A reader forwarded what he briefly imagined might be a bold, if potentially costly, innovation on the old Nigerian prince scam that asks for help squirreling away millions in unclaimed fortune: It was sent via the U.S. Postal Service, with a postmarked stamp and everything. In truth these old fashioned “advance fee” or “419” scams predate email and have circulated via postal mail in various forms and countries over the years.

AIIM
SEPTEMBER 16, 2019
It's become trite to note the speed at which technology changes, and that the speed of those changes continues to increase. But just because it's trite doesn't mean it's not true. This means that, for records managers to continue to remain relevant, we need to ensure that we are on top of new developments in records and information management that will significantly impact our organizations.

Data Matters
SEPTEMBER 18, 2019
Under the revised Payment Services Directive (2015/2366) (PSD2), the European Banking Authority (EBA) and the European Commission were required to develop and adopt regulatory technical standards on strong customer authentication and common and secure open standards of communication. These regulatory technical standards were passed into EU law as Commission Delegated Regulation (EU) 2018/389 (the RTS), which entered into effect on September 14, 2019.

Data Breach Today
SEPTEMBER 16, 2019
Intelligence Community May Be Incubating Snowden 2.0, Former NSA Employee Warns Ahead of the release of Edward Snowden's memoirs chronicling his decision to bring illegal "big data" domestic U.S. surveillance programs to light, a former NSA intelligence specialist points out that the U.S. still lacks a whistleblowing law to protect intelligence workers who spot illegal activity.

Advertisement
Generative AI is upending the way product developers & end-users alike are interacting with data. Despite the potential of AI, many are left with questions about the future of product development: How will AI impact my business and contribute to its success? What can product managers and developers expect in the future with the widespread adoption of AI?

erwin
SEPTEMBER 19, 2019
Data governance isn’t a one-off project with a defined endpoint. It’s an on-going initiative that requires active engagement from executives and business leaders. Data governance, today, comes back to the ability to understand critical enterprise data within a business context, track its physical existence and lineage, and maximize its value while ensuring quality and security.

AIIM
SEPTEMBER 18, 2019
On this episode of the AIIM on Air Podcast , your host Kevin Craine dives into the world of Intelligent Information Management in the Utilities Industry continuing the series of “I Am AIIM” member interviews. Kevin chats with two AIIM members from the Utilities Industry – Joanna Hammerschmidt , an Information Management Coordinator at a public water utility in Kansas City and John Daly , an Information Governance Manager for the Metropolitan St Louis Sewer District.

Thales Cloud Protection & Licensing
SEPTEMBER 17, 2019
As government agencies get back to work after summer barbeques, family vacations and once-in-a-lifetime getaways, the focus is on the priorities for the rest of 2019. Cybersecurity remains one of the top concerns and priorities for our government. The focus on the rest of 2019 and looking ahead to 2020 was very clear when I attended two recent industry events.

Data Breach Today
SEPTEMBER 17, 2019
New Surge in Activity Spotted After Four-Month Absence Emotet, one of the most powerful malware-spreading botnets, is active again after a four-month absence, according to several security researchers who noticed a surge in activity primarily against U.S., U.K. and German targets starting on Monday.
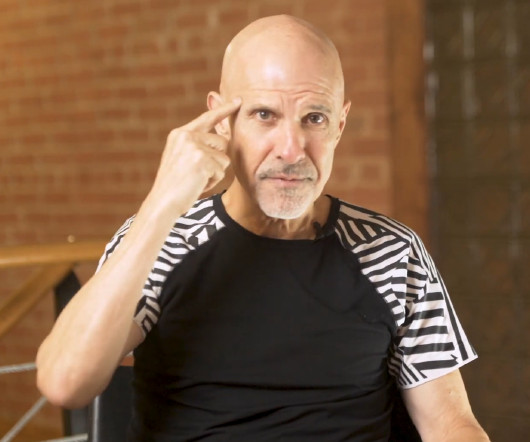
Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

Security Affairs
SEPTEMBER 17, 2019
Tens of millions of records belonging to passengers of two airline companies owned by Lion Air have been exposed and exchanged on forums. Data belonging to passengers of two airline companies owned by Lion Air have been exposed and exchanged on forums. The information was left exposed online on an unsecured Amazon bucket, the records were stored in two databases in a directory containing backup files mostly for Malindo Air and Thai Lion Air.

Schneier on Security
SEPTEMBER 16, 2019
Not that serious, but interesting : In late 2011, Intel introduced a performance enhancement to its line of server processors that allowed network cards and other peripherals to connect directly to a CPU's last-level cache, rather than following the standard (and significantly longer) path through the server's main memory. By avoiding system memory, Intel's DDIOshort for Data-Direct I/Oincreased input/output bandwidth and reduced latency and power consumption.

IT Governance
SEPTEMBER 17, 2019
We have good news for those looking for help complying with the GDPR (General Data Protection Regulation) : new guidance has been released on how to create effective data privacy controls. ISO 27701 explains what organisations must do to when implementing a PIMS (privacy information management system). The advice essentially bolts privacy processing controls onto ISO 27001 , the international standard for information security, and provides a framework to establish the best practices required by

Data Breach Today
SEPTEMBER 20, 2019
Vulnerability in Click2Gov Software Has Been Patched, Vendor Says Click2Gov municipal payment portals for eight U.S. cities were compromised after an apparent vulnerability in the software. More than 20,000 payment card records have turned up in underground markets, says Gemini Advisory.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

Security Affairs
SEPTEMBER 16, 2019
A flaw in LastPass password manager leaks credentials from previous site. An expert discovered a flaw in the LastPass password manager that exposes login credentials entered on a site previously visited by a user. Tavis Ormandy, the popular white-hat hacker at Google Project Zero, has discovered a vulnerability in the LastPass password manager that exposes login credentials entered on a site previously visited by a user.

Schneier on Security
SEPTEMBER 20, 2019
Maria Farrell has a really interesting framing of information/device privacy: What our smartphones and relationship abusers share is that they both exert power over us in a world shaped to tip the balance in their favour, and they both work really, really hard to obscure this fact and keep us confused and blaming ourselves. Here are some of the ways our unequal relationship with our smartphones is like an abusive relationship: They isolate us from deeper, competing relationships in favour of sup

Dark Reading
SEPTEMBER 19, 2019
The breach, which reportedly exposed data on millions of passengers, is one of many that have resulted from organizations leaving data publicly accessible in cloud storage buckets.

Data Breach Today
SEPTEMBER 18, 2019
Suit Seeks to Collect Book Profits Based on Alleged Violation of Nondisclosure Agreement The U.S. Justice Department has sued Edward Snowden over his new memoir, claiming that the former NSA contractor violated a nondisclosure agreement he signed when he worked for the government before becoming the world's best-known whistleblower. The suit seeks to collect all profits from the book.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Security Affairs
SEPTEMBER 15, 2019
Facebook addressed a vulnerability in Instagram that could have allowed attackers to access private user information. The security researcher @ZHacker13 discovered a flaw in Instagram that allowed an attacker to access account information, including user phone number and real name. ZHacker13 discovered the vulnerability in August and reported the issue to Facebook that asked for additional time to address the issue.

PerezBox
SEPTEMBER 16, 2019
In September of 2019 Mozilla will begin releasing DNS over HTTPS (DOH) in Firefox via their Trusted Recursive Resolver (TRR) program. A primer on DNS Security. The change is based. Read More. The post Mozilla Introduces Mechanism to Hijack all DNS Traffic in the Name of Privacy appeared first on PerezBox.

Schneier on Security
SEPTEMBER 20, 2019
Earlier this month I made fun of a company called Crown-Sterling, for.for.for being a company that deserves being made fun of. This morning, the company announced that they "decrypted two 256-bit asymmetric public keys in approximately 50 seconds from a standard laptop computer." Really. They did. This keylength is so small it has never been considered secure.

Data Breach Today
SEPTEMBER 16, 2019
Commission Finds That Phillip Capital Made Series of Missteps The U.S. Commodity Futures Trading Commission has hit Philips Capital Inc., a Chicago-based brokerage firm, with a $500,000 penalty for security missteps before and after a 2018 data breach, which resulted in the theft of $1 million from client accounts.

Advertisement
Start-ups & SMBs launching products quickly must bundle dashboards, reports, & self-service analytics into apps. Customers expect rapid value from your product (time-to-value), data security, and access to advanced capabilities. Traditional Business Intelligence (BI) tools can provide valuable data analysis capabilities, but they have a barrier to entry that can stop small and midsize businesses from capitalizing on them.

Security Affairs
SEPTEMBER 18, 2019
Researchers at Greenbone Networks vulnerability analysis and management company discovered 400 Million medical radiological images exposed online via unsecured PACS servers. The experts at Greenbone Networks vulnerability analysis and management company discovered 600 unprotected servers exposed online that contained medical radiological images. The research was conducted between mid-July 2019 and early September 2019.

Jamf
SEPTEMBER 18, 2019
macOS Catalina introduces a new user-mode framework called Endpoint Security. See what it is and how it impacts you.

IBM Big Data Hub
SEPTEMBER 19, 2019
Will AI take over the world? Or, more to the point, will it take over the humankind? It seems to have invaded the public consciousness, sparking concerns that AI will take away jobs. This fear is driven in part by companies using AI to deliver cost savings across their businesses, including areas related to labor.
Let's personalize your content