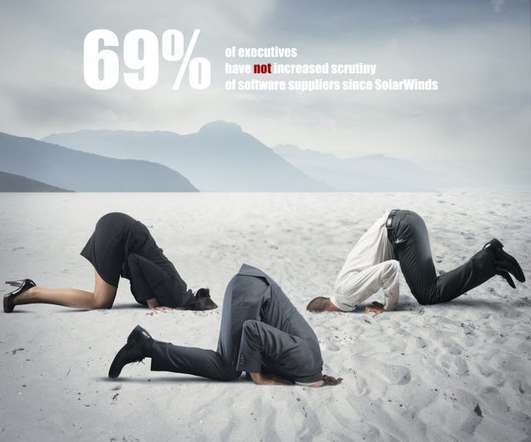
6 Eye-Opening Statistics About Software Supply Chain Security
Dark Reading
OCTOBER 27, 2021
The latest facts and figures on the state of software supply chain security in the enterprise.
Dark Reading
OCTOBER 27, 2021
The latest facts and figures on the state of software supply chain security in the enterprise.

eSecurity Planet
OCTOBER 26, 2021
As threat actors aim at IT supply chains , enhanced cybersecurity has been the recent driving force for industry adoption of the Software Bill of Materials (SBOM) framework. With a simple list of components that make up a software product, SBOMs enhance transparency between software buyers and sellers, provide the necessary visibility to identify vulnerabilities , and enable rapid incident response.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
OCTOBER 27, 2021
Why do so many HIPAA -covered entities and their vendors do such a poor job managing security risk and safeguarding patient's protected health information? Many critical factors come into play, say Roger Severino, ex- director of HHS OCR, and Bob Chaput, founder of security consultancy Clearwater.

Krebs on Security
OCTOBER 26, 2021
U.S. federal investigators today raided the Florida offices of PAX Technology , a Chinese provider of point-of-sale devices used by millions of businesses and retailers globally. KrebsOnSecurity has learned the raid is tied to reports that PAX’s systems may have been involved in cyberattacks on U.S. and E.U. organizations. FBI agents entering PAX Technology offices in Jacksonville today.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.
Security Affairs
OCTOBER 23, 2021
The U.S. CISA warned of crypto-mining malware hidden in a popular JavaScript NPM library, named UAParser.js, which has millions of weekly downloads. The U.S. Cybersecurity and Infrastructure Security Agency published an advisory to warn of the discovery of a crypto-mining malware in the popular NPM Package UAParser.js. The popular library has million of weekly downloads. “Versions of a popular NPM package named ua-parser-js was found to contain malicious code.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Data Breach Today
OCTOBER 25, 2021
Flaw in DarkSide and BlackMatter Enabled Security Firm to Decrypt Files for Free While ransomware might be today's top cybercrime boogeyman, attackers aren't infallible. The latest example: Errors in DarkSide - and its BlackMatter rebrand - enabled security experts to quietly decrypt many victims' files for free, saving millions in potential ransom payments.
Krebs on Security
OCTOBER 25, 2021
The Conti ransomware affiliate program appears to have altered its business plan recently. Organizations infected with Conti’s malware who refuse to negotiate a ransom payment are added to Conti’s victim shaming blog, where confidential files stolen from victims may be published or sold. But sometime over the past 48 hours, the cybercriminal syndicate updated its victim shaming blog to indicate that it is now selling access to many of the organizations it has hacked.

Security Affairs
OCTOBER 28, 2021
German authorities have identified a Russian man named Nikolay K. who is suspected to be a prominent member of the REvil ransomware gang. REvil ransomware gang is one of the most successful ransomware operations, the group and its affiliated hit hundreds of organizations worldwide. On July 2, the gang hit the Kaseya cloud-based MSP platform impacting MSPs and their customers, it asked $70 million worth of Bitcoin for decrypting all impacted systems.

WIRED Threat Level
OCTOBER 23, 2021
Plus: Data theft in Argentina, a Sinclair Broadcast Group hack, and more of the week’s top security news.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Data Breach Today
OCTOBER 25, 2021
Move by Colonial Pipeline Attackers Follows Law Enforcement Action Against REvil Following an outage of the REvil - aka Sodinokibi - ransomware operation due to coordinated law enforcement efforts involving the U.S. and foreign partners, the operators behind DarkSide ransomware have moved Bitcoin worth almost $7 million to multiple new wallets, making it more difficult to track.
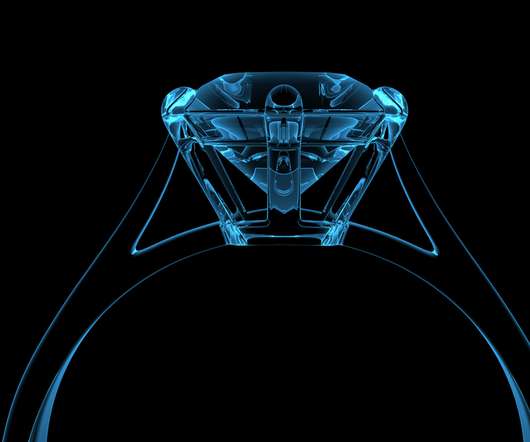
Krebs on Security
OCTOBER 28, 2021
In December 2018, bling vendor Signet Jewelers fixed a weakness in their Kay Jewelers and Jared websites that exposed the order information for all of their online customers. This week, Signet subsidiary Zales.com updated its website to remediate a nearly identical customer data exposure. Last week, KrebsOnSecurity heard from a reader who was browsing Zales.com and suddenly found they were looking at someone else’s order information on the website, including their name, billing address, sh

Security Affairs
OCTOBER 23, 2021
Cisco fixes an OS command-injection flaw, tracked as CVE-2021-1529, in Cisco SD-WAN that could allow privilege escalation and lead to arbitrary code execution. Cisco addressed a high-severity OS command-injection vulnerability, tracked as CVE-2021-1529, in Cisco SD-WAN that could allow privilege escalation and lead to arbitrary code execution. Cisco SD-WAN is a cloud-delivered overlay WAN architecture that enables digital and cloud transformation at enterprises, it allows to connect disparate of

The Last Watchdog
OCTOBER 26, 2021
Our Public Key Infrastructure is booming but also under a strain that manual certificate management workflows are not keeping up with. Related: A primer on advanced digital signatures. PKI and digital certificates were pivotal in the formation of the commercial Internet, maturing in parallel with ecommerce. With digital transformation leading to a boom in the use of digital certificates, our bedrock authentication and encryption framework is at an inflection point, where the demand and adoption

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.
Data Breach Today
OCTOBER 27, 2021
Rebranding Remains Easy for Ransomware Groups, While Affiliates Already Come and Go Will the notorious ransomware operation known as REvil, aka Sodinokibi, reboot yet again after someone apparently messed with its infrastructure? Experts suggest that the operation's brand is burned, and administrators will launch a new group. Many affiliates, meanwhile, already work with multiple groups.

WIRED Threat Level
OCTOBER 27, 2021
Advocates will once again be granted a DMCA exception to make accessible versions of texts. They argue that it's far past time to make it permanent.

Security Affairs
OCTOBER 26, 2021
The FBI published a flash alert to warn of the activity of the Ranzy Locker ransomware that had already compromised tens of US companies. The FBI published a flash alert to warn of Ranzy Locker ransomware operations that had already compromised at least 30 US companies this year. The gang has been active since at least 2020, threat actors hit organizations from various industries. “Unknown cyber criminals using Ranzy Locker ransomware had compromised more than 30 US businesses as of July 2

The Last Watchdog
OCTOBER 25, 2021
When it comes to cyber attacks, most businesses think: “It could never happen to us,” but some plots are just hitting a little too close to home. Related: T-Mobile breach reflects rising mobile device attacks. For instance, if you’ve ever played Grand Theft Auto, you know the goal is quite simply mass destruction: Use whatever resources you have at your disposal to cause as much damage as you possibly can and just keep going.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Data Breach Today
OCTOBER 28, 2021
Incident Is Among Latest Involving Healthcare Supply Chain Vendors A ransomware attack on a medical practice management services firm that included the theft of files containing patient information is among the latest security incidents involving similar third-party vendors.

WIRED Threat Level
OCTOBER 26, 2021
Operation Dark HunTor spanned eight countries—and put the focus on sellers more than marketplaces.

Security Affairs
OCTOBER 24, 2021
Microsoft uncovered an extensive series of credential phishing campaigns that employed a custom phishing kit tracked as TodayZoo. Microsoft researchers uncovered a custom phishing kit, dubbed TodayZoo, that was used in an extensive series of credential phishing campaigns. A “phishing kit” is a set of software or services aimed at facilitating phishing campaigns, In most cases a phishing kit is an archive file containing images, scripts, and HTML pages that allow threat actors to creat a phishing

The Last Watchdog
OCTOBER 28, 2021
Over the past five years, cryptocurrency exchanges have been the target of increasingly damaging “ 51% attacks ” resulting in the theft of over $30 million worth of cryptocurrency to date. Related: Wildland restores control of data to individuals. However, these attacks aren’t due to exchange security flaws; malicious actors are exploiting the underlying consensus protocols of blockchains themselves.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

Data Breach Today
OCTOBER 29, 2021
VMware’s Tom Kellermann on Defending Against Ransomware Attacks In ransomware attacks, cybercriminals attack through the backups because they know that security practitioners rely on backups to save themselves after a ransomware attack. Therefore, it is essential to have multiple backups, says Tom Kellermann, head of cybersecurity strategy at VMware.

WIRED Threat Level
OCTOBER 27, 2021
Google’s new flagship smartphone is its most secure yet, thanks to a little vertical integration.
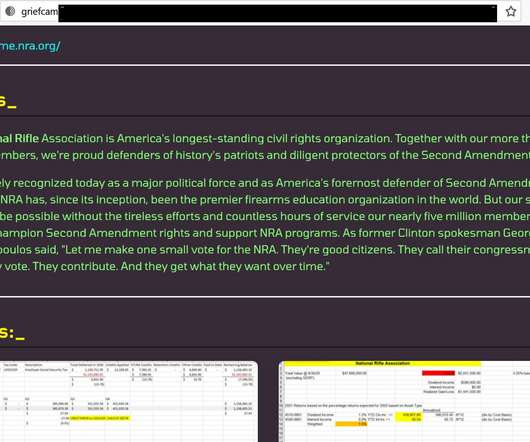
Security Affairs
OCTOBER 27, 2021
Grief ransomware operators claim to have compromised computer systems at US National Rifle Association (NRA) and added it to their leak site. Grief ransomware operators announced to have hacked US National Rifle Association (NRA) and threaten to leak the stolen data. The NRA was added to the list of compromised organizations on the leak site of the group, that gang also published a set of documents as proof of the hack.

IT Governance
OCTOBER 26, 2021
This Sunday is both Halloween and the end of National Cyber Security Awareness Month – and what better way to mark the occasion than with some cyber security horror stories? In this blog, we look at three ways in which fraudsters trick victims into handing over their sensitive data. Will you have nightmares over Evil Twins or be scared straight by phishing scams?

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.
Data Breach Today
OCTOBER 25, 2021
The Rant of the Day From Ian Keller, Ericsson In his second Rant of the Day for the CyberEdBoard Profiles in Leadershop blog, Ian Keller, security director at Ericsson and CyberEdBoard executive member, talks about what a CISO does - and what a CISO should do.

WIRED Threat Level
OCTOBER 24, 2021
Microsoft has rolled out its most secure operating system yet. Here's how to make the most of it.

Security Affairs
OCTOBER 28, 2021
Microsoft finds a flaw in macOS, dubbed Shrootless ( CVE-2021-30892 ), that can allow attackers to bypass System Integrity Protection (SIP). Microsoft discovered a vulnerability in macOS, dubbed Shrootless ( CVE-2021-30892 ), that can allow attackers to bypass System Integrity Protection (SIP) and perform malicious activities, such as gaining root privileges and installing rootkits on vulnerable devices.
Let's personalize your content