Why scaling agentic AI is a marathon, not a sprint
Collaboration 2.0
MARCH 28, 2025
It's up to humans to figure out how to create and use AI agents effectively, but this process will take some time.

Collaboration 2.0
MARCH 28, 2025
It's up to humans to figure out how to create and use AI agents effectively, but this process will take some time.

WIRED Threat Level
MARCH 24, 2025
DNA-testing company 23andMe has filed for bankruptcy, which means the future of the companys vast trove of customer data is unknown. Heres what that means for your genetic data.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
MARCH 26, 2025
It starts with a ripple of confusion, then panic. Hospital systems freeze mid-procedure. Electronic medical records become inaccessible. Related: Valuable intel on healthcare system cyber exposures In the ICU, alarms blare as doctors and nurses scramble to stabilize critical patients without access to real-time data. Admissions come to a standstill.

Security Affairs
MARCH 24, 2025
The FBI warns of a significant increase in scams involving free online document converters to infect users with malware. The FBI warns that threat actors use malicious online document converters to steal users sensitive information and infect their systems with malware. “The FBI Denver Field Office is warning that agents are increasingly seeing a scam involving free online document converter tools, and we want to encourage victims to report instances of this scam.” reads the alert. &

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.
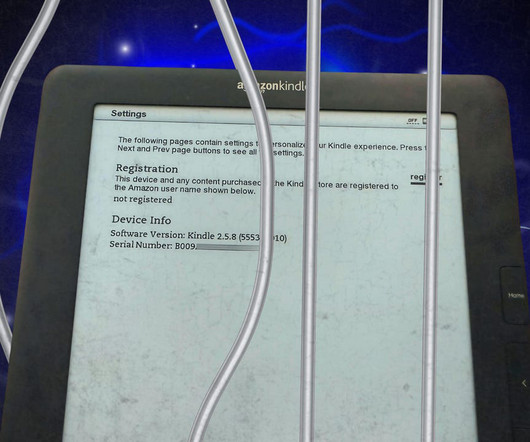
Collaboration 2.0
MARCH 26, 2025
Your old Kindle's not dead yet; it's just waiting for a jailbreak. Let me show you how it's done.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

The Last Watchdog
MARCH 24, 2025
Quantum computings ability to break todays encryption may still be years awaybut security leaders cant afford to wait. Forresters The Future of Quantum Security makes it clear: the transition to quantum-safe cryptography must start now. Related: Quantum standards come of age The real threat isnt just the eventual arrival of quantum decryptionits that nation-state actors are already stockpiling encrypted data in harvest now, decrypt later attacks.

Security Affairs
MARCH 26, 2025
Google fixed a flaw in the Chrome browser for Windows that was actively exploited in attacks targeting organizations in Russia. Google has released out-of-band fixes to address a high-severity security vulnerability, tracked as CVE-2025-2783 , in Chrome browser for Windows. The flaw was actively exploited in attacks targeting organizations in Russia.

Collaboration 2.0
MARCH 23, 2025
For a laptop with Linux pre-installed, the Tuxedo Computers Infinity Book Pro 14 (Gen 9) offers a stunning display and strong performance.

Schneier on Security
MARCH 26, 2025
Cloudflare has a new feature —available to free users as well—that uses AI to generate random pages to feed to AI web crawlers: Instead of simply blocking bots, Cloudflare’s new system lures them into a “maze” of realistic-looking but irrelevant pages, wasting the crawler’s computing resources. The approach is a notable shift from the standard block-and-defend strategy used by most website protection services.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

eSecurity Planet
MARCH 24, 2025
A sophisticated supply chain hack targeting Oracle Cloud has exfiltrated a staggering 6 million records. CloudSEKs XVigil uncovered that threat actor rose87168 began selling the stolen data on March 21. The breach, exploiting a vulnerability in Oracles cloud infrastructure, now endangers over 140,000 tenants and has raised serious questions about cloud security practices.

Security Affairs
MARCH 26, 2025
Broadcom addressed a high-severity authentication bypass vulnerability, tracked as CVE-2025-22230, in VMware Tools for Windows. Broadcom released security updates to address a high-severity authentication bypass vulnerability, tracked as CVE-2025-22230 (CVSS score 9.8), impacting VMware Tools for Windows. VMware Tools for Windows is a suite of utilities that enhances the performance and usability of virtual machines (VMs) running on VMware hypervisors like VMware Workstation, Fusion, and vSphere

Collaboration 2.0
MARCH 25, 2025
Signal is in the news for all the wrong reasons. Here's what to know about it and why it remains a top choice for protecting conversations.
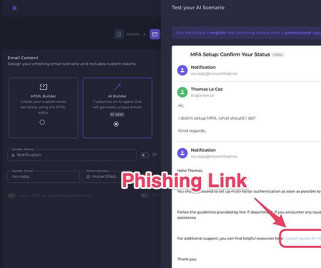
The Last Watchdog
MARCH 24, 2025
Paris, France, Mar. 24, 2025, CyberNewswire — Arsen , a leading cybersecurity company specializing in social engineering defense, today announced the full release of Conversational Phishing, a groundbreaking feature embedded in its phishing simulation platform. This AI-powered tool introduces dynamic, adaptive phishing conversations to train employees against evolving threats more effectively than ever before.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

WIRED Threat Level
MARCH 24, 2025
The ad hoc addition to the otherwise tightly controlled White House information environment could create blind spots and security exposures while setting potentially dangerous precedent.
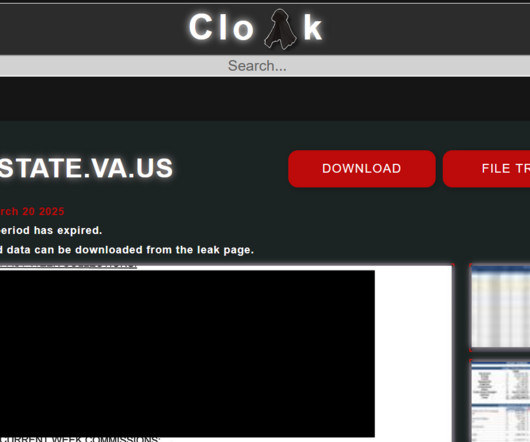
Security Affairs
MARCH 24, 2025
The Cloak ransomware group claims responsibility for a cyberattack on the Virginia Attorney Generals Office that occurred in February. The ransomware group Cloak has claimed responsibility for a February cyberattack on the Virginia Attorney General Office. A cyberattack on the Virginia Attorney Generals Office forced officials to shut down IT systems, including email and VPN, and revert to paper filings.

Collaboration 2.0
MARCH 27, 2025
You'll get priceless Linux experience from developers such as Linux Foundation Fellow Shuah Khan and kernel stable maintainer Greg Kroah-Hartman. Here's how to apply.

Data Breach Today
MARCH 26, 2025
Cybersecurity Firm Finds Rash of Apps Coded With Microsoft.NET MAUI Cybercriminals are using a Microsoft cross-platform app development framework to create Android malware that bypasses security measures, evades detection and steals user data. Malicious apps spotted by McAfee researchers aren't traditional Android malware.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

OpenText Information Management
MARCH 24, 2025
In 2024, a staggering 67% 1 of healthcare organizations worldwide faced ransomware attacksthe highest rate in years. The healthcare industry, with its treasure trove of protected health information (PHI) and critical infrastructure, has become a prime target for cybercriminals. From massive data breaches at major organizations to skyrocketing recovery costs, the stakes have never been higher.
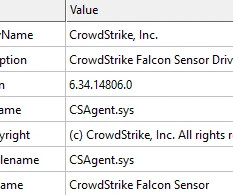
Security Affairs
MARCH 24, 2025
Medusa ransomware uses a malicious Windows driver ABYSSWORKER to disable security tools, making detection and mitigation more difficult. Elastic Security Labs tracked a financially driven MEDUSA ransomware campaign using a HEARTCRYPT-packed loader and a revoked certificate-signed driver, ABYSSWORKER, to disable EDR tools. The attackers used a 64-bit Windows PE driver named smuol.sys, disguised as a CrowdStrike Falcon driver, which is VMProtect-protected and signed with a revoked Chinese certific
Collaboration 2.0
MARCH 27, 2025
Before diving into the Windows 11 2024 update, know that you may encounter some problems. Here's the bug report now.

AIIM
MARCH 27, 2025
One of my favorite mottos is "Start small, grow big." When organizations approach me about building an information management program from scratch, they often feel overwhelmed by the magnitude of the task. Let me share how to make this process more digestible.

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.

OpenText Information Management
MARCH 27, 2025
Generative AI, particularly Large Language Models (LLMs) are finding important applications in many industries including cybersecurity. Organizations are using LLMs and other Generative AI models effectively for the detection of Malware and Software Vulnerabilities. Generative AI can be used in different ways for Malware and Vulnerability detection.

Security Affairs
MARCH 26, 2025
Resecurity found an LFI flaw in the leak site of BlackLock ransomware, exposing clearnet IPs and server details. Resecurity has identified a Local File Include (LFI) vulnerability in Data Leak Site (DLS) of BlackLock Ransomware. Cybersecurity experts were able to exploit misconfiguration in vulnerable web-app used by ransomware operators to publish victims data – leading to clearnet IP addresses disclosure related to their network infrastructure behind TOR hidden services (hosting them) an

Collaboration 2.0
MARCH 27, 2025
If you're looking for extra power outlets but don't have space for a traditional strip, Baseus' 32W charging station has you covered.

Data Breach Today
MARCH 27, 2025
Also: The Treasury Department Lifts Tornado Cash Sanctions This week, Abracadabra hack, updates on Tornado Cash and Bybit, $7M scam money recovery, man faces prison for stabbing crypto CEO, movie director charged for swindle, Ripple-SEC case wrap-up, Grinex is the new Garantex, Gotbit plea deal, Coinbase in supply chain hack and Binance insider risk threat.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!
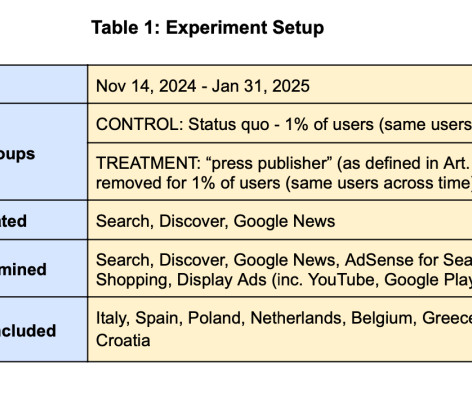
John Battelle's Searchblog
MARCH 26, 2025
There’s an old maxim in the news business: Stories in which a dog bites a man are uninteresting. But a man biting a dog? Now that’s worth writing up! Last week Google released a report on the value of news to its business. Its conclusions minced no words. Here’s the money quote: “…news content in Search has no measurable impact on ad revenue for Google.” On first glance, Google’s experiment feels like a Dog Bites Man story – everyone knows news doe

Security Affairs
MARCH 24, 2025
A critical flaw in the Next.js React framework could be exploited to bypass authorization checks under certain conditions. Maintainers of Next.js React framework addressed a critical vulnerability tracked as CVE-2025-29927 (CVSS score of 9.1) with the release of versions versions 12.3.5, 13.5.9, 14.2.25, and 15.2.3. “Next.js version 15.2.3 has been released to address a security vulnerability ( CVE-2025-29927 ).

Collaboration 2.0
MARCH 28, 2025
The Nothing Phone 3a Pro proves that not all Androids have to look the same. Its unique design is matched by an approachable price point.
Let's personalize your content