Banks and Airlines Disrupted as Mass Outage Hits Windows PCs
Data Breach Today
JULY 19, 2024
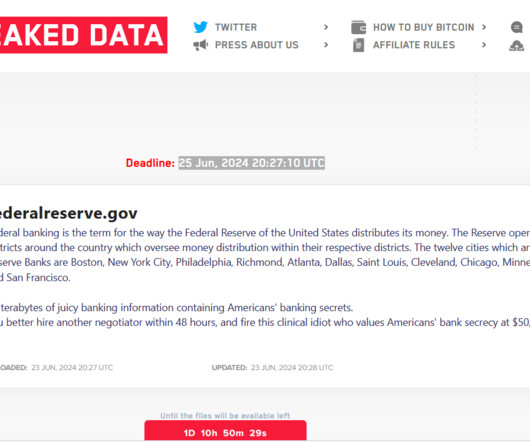
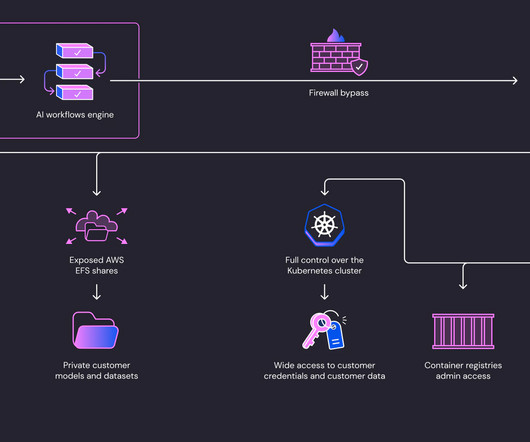
CrowdStrike Confirms Faulty Software Update for Falcon Sensor, Is Deploying Fix Banks, airlines, media giants and others are being disrupted by a mass, global IT outage tied to Windows PCs. While CrowdStrike has issued a workaround tied to a Falcon software update that appears to be the culprit, many IT administrators say it so far remains difficult to implement at scale.




































Let's personalize your content