The Worst Hacks of 2024
WIRED Threat Level
DECEMBER 26, 2024
From Chinese cyberspies breaching US telecoms to ruthless ransomware gangs disrupting health care for millions of people, 2024 saw some of the worst hacks, breaches, and data leaks ever.

WIRED Threat Level
DECEMBER 26, 2024
From Chinese cyberspies breaching US telecoms to ruthless ransomware gangs disrupting health care for millions of people, 2024 saw some of the worst hacks, breaches, and data leaks ever.
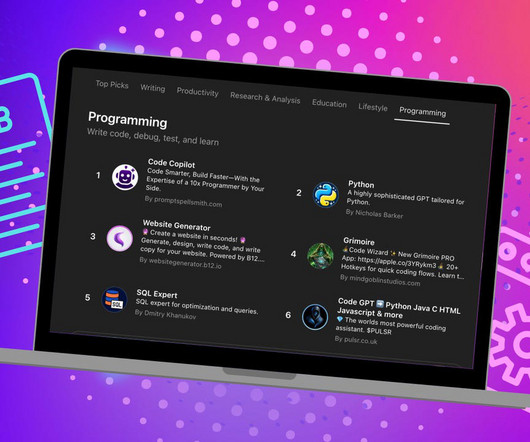
Collaboration 2.0
DECEMBER 24, 2024
In just two years, AI has gone from hype to essential skill, offering massive productivity gains and increasing creativity among teams who use it. Here's how.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
DECEMBER 23, 2024
Italy’s data protection watchdog fined OpenAI 15 million for ChatGPT’s improper collection of personal data. Italys privacy watchdog, Garante Privacy, fined OpenAI 15M after investigating ChatGPT’s personal data collection practices. The Italian Garante Priacy also obliges OpenAI to conduct a six-month informational campaign over ChatGPTs data management violations.
Data Breach Today
DECEMBER 24, 2024
Cybercriminals Say They Hacked 66 Companies The Clop cybercriminal group is threatening to make public the companies swept up by its mass hacking of managed file-transfer software built by Cleo Communications. In a Dec. 24 update to its dark web leak site, Clop asserted it has "data of many companies who use Cleo.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

WIRED Threat Level
DECEMBER 27, 2024
Smartphones and face recognition are being combined to create new digital travel documents. The paper passports days are numbereddespite new privacy risks.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Security Affairs
DECEMBER 27, 2024
Palo Alto Networks addressed a high-severity PAN-OS flaw that could trigger denial-of-service (DoS) on vulnerable devices. Palo Alto Networks addressed a high-severity flaw, tracked as CVE-2024-3393 (CVSS score: 8.7), in PAN-OS software that could cause a denial-of-service (DoS) condition. An unauthenticated attacker can exploit this vulnerability to reboot the firewall by sending a malicious packet through its data plane.

Data Breach Today
DECEMBER 23, 2024
Infrastructure Problems Blamed; Users Appear to Move to Similar FlowerStorm Service As the end of the year approaches, it's out with the old and in with the new as researchers report that Rockstar 2FA, which once facilitated prolific phishing-as-a-service hits, has crashed and burned, apparently leading many one-time users to move to rival FlowerStorm.

WIRED Threat Level
DECEMBER 25, 2024
AI voice cloning and deepfakes are supercharging scams. One method to protect your loved ones and yourself is to create secret code words to verify someones identity in real time.
Collaboration 2.0
DECEMBER 24, 2024
I've used and covered Linux for nearly 30 years. Here's my top pick for my favorite open-source distro in 2024.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.
AIIM
DECEMBER 26, 2024
As an Information Leader, selecting the right imaging technology for your organization is a critical decision that impacts information flow, accessibility, and management. With the rapid evolution of cloud and mobile technologies, it's crucial to choose solutions that are not only effective today but also future-proof. The TWAIN Working Group standards, particularly TWAIN Direct, offer a framework for making informed decisions.

Security Affairs
DECEMBER 24, 2024
Adobe released out-of-bandsecurity updates to address a critical ColdFusion vulnerability, experts warn of a PoC exploit code available for it. Adobe released out-of-bandsecurity updates to address a critical vulnerability, tracked as CVE-2024-53961 (CVSS score 7.4), in ColdFusion. Experts warn of the availability of a proof-of-concept (PoC) exploit code for this vulnerability.

WIRED Threat Level
DECEMBER 23, 2024
In Russias war against Ukraine, electronic warfare, including signal-jamming, anti-drone weapons, and innovative protections for critical military systems, has become a key piece of the conflict.

Collaboration 2.0
DECEMBER 24, 2024
If you're looking for a laptop with Linux pre-installed, Tuxedo Computers' Infinity Book Pro 14 (Gen 9) has a gorgeous display and impressive performance.

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.

Data Breach Today
DECEMBER 27, 2024
Unauthenticated Attackers Using Malicious Packet to Crash Devices' PAN-OS Software Security giant Palo Alto Networks is pushing updates to fix a denial-of-service vulnerability in its PAN-OS device software that unauthenticated, remote attackers have been actively exploiting. The flaw can be triggered by sending firewalls "a malicious packet," which will crash the devices.

Security Affairs
DECEMBER 27, 2024
A Brazilian citizen faces U.S. charges for allegedly threatening to release data stolen from a company in a March 2020 security breach. The U.S. government has charged the Brazilian citizen Junior Barros De Oliveira, 29, with allegedly threatening to release data stolen from a company during a March 2020 security breach. De Oliveira was charged with four counts of extortionate threats involving information obtained from protected computers in violation of Title 18, United States Code, Section 10

WIRED Threat Level
DECEMBER 21, 2024
Plus: Googles U-turn on creepy fingerprint tracking, the LockBit ransomware gangs teased comeback, and a potential US ban on the most popular routers in America.

Collaboration 2.0
DECEMBER 23, 2024
USB-C is great, but the ports can be fragile and vulnerable to damage. This breakaway accessory eliminates the chances of damaging your port.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Data Breach Today
DECEMBER 26, 2024
Also, US Court Rules NSO Group Violated Hacking Laws With Pegasus Spyware This week, cyberattack disrupts Japan Airlines, U.S. court rules NSO Group violated hacking laws, the European Space Agencys web store hacked, FTC orders Marriott to overhaul data security, Sophos patches critical firewall flaws and Apache fixes critical SQL injection in Traffic Control.

Schneier on Security
DECEMBER 24, 2024
A judge has found that NSO Group, maker of the Pegasus spyware, has violated the US Computer Fraud and Abuse Act by hacking WhatsApp in order to spy on people using it. Jon Penney and I wrote a legal paper on the case.
KnowBe4
DECEMBER 23, 2024
KnowBe4 is a big believer in focusing on decreasing human risk as the best way to decrease cybersecurity risk in most environments.

Collaboration 2.0
DECEMBER 24, 2024
If you're a mobile gamer, the Redmagic 10 Pro was designed specifically for you, and I highly recommend it.

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.

Data Breach Today
DECEMBER 23, 2024
Researchers Trace 61% of Known Losses This Year to Pyongyang-Backed Hackers Hackers tied to North Korea's cash-strapped totalitarian dictatorship this year stole a record amount of cryptocurrency, totaling $1.34 billion across 47 incidents, or about double their known haul for 2023, reported blockchain analytics firm Chainalysis.

Schneier on Security
DECEMBER 27, 2024
The basic strategy is to place a device with a hidden camera in a position to capture normally hidden card values, which are interpreted by an accomplice off-site and fed back to the player via a hidden microphone. Miniaturization is making these devices harder to detect. Presumably AI will soon obviate the need for an accomplice.

KnowBe4
DECEMBER 24, 2024
CyberheistNews Vol 14 #52 [Heads Up] Bad Actors Use Voice Phishing in Microsoft Teams To Spread Malware

Collaboration 2.0
DECEMBER 23, 2024
In 2024, AI became truly helpful. Here are 15 clever ways I integrated it into my workflow for quicker, better results - and what I hope to do with it in 2025.

Advertisement
Large enterprises face unique challenges in optimizing their Business Intelligence (BI) output due to the sheer scale and complexity of their operations. Unlike smaller organizations, where basic BI features and simple dashboards might suffice, enterprises must manage vast amounts of data from diverse sources. What are the top modern BI use cases for enterprise businesses to help you get a leg up on the competition?

Data Breach Today
DECEMBER 27, 2024
American Addiction Centers Says 422,424 Individuals' Private Details Exposed Substance abuse treatment company American Addiction Centers is warning nearly half a million patients that ransomware-wielding attackers stole their personal details, including names and Social Security numbers. The Rhysida ransomware operation claimed to perpetrate the attack.

Schneier on Security
DECEMBER 26, 2024
Scammers are hacking Google Forms to send email to victims that come from google.com. Brian Krebs reports on the effects. Boing Boing post.
KnowBe4
DECEMBER 23, 2024
Trend Micro warns that the Russian state-sponsored threat actor Earth Koshchei (also known as APT29 or Cozy Bear) is using spear phishing emails to trick victims into connecting to rogue Remote Desktop Protocol (RDP) relays.
Let's personalize your content