The Time Is Now for IoT Security Standards
Dark Reading
AUGUST 11, 2022
Industry standards would provide predictable and understandable IoT security frameworks.

Dark Reading
AUGUST 11, 2022
Industry standards would provide predictable and understandable IoT security frameworks.
Krebs on Security
AUGUST 10, 2022
One way to tame your email inbox is to get in the habit of using unique email aliases when signing up for new accounts online. Adding a “+” character after the username portion of your email address — followed by a notation specific to the site you’re signing up at — lets you create an infinite number of unique email addresses tied to the same account.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
AUGUST 6, 2022
Vulnerability Allowed Threat Actors to Gain Access to Personal Information Twitter confirms that a zero-day vulnerability allowed threat actors to gain access to the personal information of 5.4 million user account profiles. The company was notified about this specific vulnerability in Twitter's systems through their bug bounty program in January.

The Last Watchdog
AUGUST 8, 2022
Our technological world is advancing at dizzying speeds. Related: The coming of a ‘bio digital twin” Over the last decade, we have seen the introduction of 4G and 5G telecommunication service, the iPad, Instagram, and the introduction, acceptance, and adoption of cloud services from Microsoft, Google, and Amazon, as well as cloud computing.
Speaker: Maher Hanafi, VP of Engineering at Betterworks & Tony Karrer, CTO at Aggregage
Executive leaders and board members are pushing their teams to adopt Generative AI to gain a competitive edge, save money, and otherwise take advantage of the promise of this new era of artificial intelligence. There's no question that it is challenging to figure out where to focus and how to advance when it’s a new field that is evolving everyday. 💡 This new webinar featuring Maher Hanafi, CTO of Betterworks, will explore a practical framework to transform Generative AI prototypes into

eSecurity Planet
AUGUST 9, 2022
Regulatory compliance and data privacy issues have long been an IT security nightmare. And since the EU’s General Data Protection Regulation (GDPR) took effect May 25, 2018, IT compliance issues have been at the forefront of corporate concerns. GDPR, the EU’s flagship data privacy and “right to be forgotten” regulation, has made the stakes of a data breach higher than ever.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.
Data Breach Today
AUGUST 10, 2022
Monthly Dump Includes Patches for 141 Flaws, Including 17 'Critical' Fixes More than two years after being notified of it, Microsoft issued a fix for a Microsoft Windows Support Diagnostic Tool vulnerability known as DogWalk. The fix is part of the operating system giant's newest Patch Tuesday dump, which includes patches for 141 flaws.

IT Governance
AUGUST 9, 2022
Welcome to our August 2022 review of phishing attacks, in which we explore the latest email scams and the tactics that cyber criminals use to trick people into handing over their personal data. This month, we look at a scam targeting verified Twitter users and the latest in a series of phishing campaigns that are designed to steal the contents of cryptocurrency wallets.
Security Affairs
AUGUST 7, 2022
A massive cyberattack hit the website of the German Chambers of Industry and Commerce (DIHK) this week. A massive attack hit the website of the German Chambers of Industry and Commerce (DIHK) forcing the organization to shut down its IT systems as a precautionary measure for security reasons. Aktuell wird intensiv an Lösung und Abwehr gearbeitet. Wir informieren Sie hier, welche Anwendungen wieder funktionsfähig sind: [link] #IHK #DIHK pic.twitter.com/5OHMOLH7Mz — DIHK (@DIHK_News) August

Threatpost
AUGUST 11, 2022
Belgian researcher Lennert Wouters revealed at Black Hat how he mounted a successful fault injection attack on a user terminal for SpaceX’s satellite-based internet system.

Advertisement
Generative AI is upending the way product developers & end-users alike are interacting with data. Despite the potential of AI, many are left with questions about the future of product development: How will AI impact my business and contribute to its success? What can product managers and developers expect in the future with the widespread adoption of AI?

Data Breach Today
AUGUST 9, 2022
Victims Often Attacked Simultaneously by Multiple Ransomware Groups Cybercriminals monitor leak sites for newly listed ransomware victims in a bid to try their own hand at dropping encryption malware, says Sophos. The cybersecurity firm says it's seen an uptick in incidents involving multiple criminal gangs demanding a ransom for unencrypted victims' files.

eSecurity Planet
AUGUST 8, 2022
Companies spend a staggering amount of money on cybersecurity products to defend their networks and data from hackers, but a couple of industry pros say that money is wasted if companies don’t change their internal cybersecurity culture. In September 2021, Cybersecurity Ventures anticipated in a report that the total global cybersecurity spending would exceed a staggering $1.75 trillion by 2025.

Security Affairs
AUGUST 9, 2022
Cybersecurity researchers from Kaspersky linked the Maui ransomware to the North Korea-backed Andariel APT group. Kaspersky linked with medium confidence the Maui ransomware operation to the North Korea-backed APT group Andariel , which is considered a division of the Lazarus APT Group, . North Korean nation-state actors used Maui ransomware to encrypt servers providing healthcare services, including electronic health records services, diagnostics services, imaging services, and intranet servic
Dark Reading
AUGUST 11, 2022
Ransomware gang gained access to the company's VPN in May by convincing an employee to accept a multifactor authentication (MFA) push notification.
Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.
Data Breach Today
AUGUST 10, 2022
An ISMG Overview of the Technology Buzz Leading Up to Black Hat Conference 2022 ISMG caught up with 11 security executives in Las Vegas on Tuesday to discuss everything from open-source intelligence and Web3 security to training new security analysts and responding to directory attacks. Here's a look at some of the most interesting things we heard from industry leaders.
eSecurity Planet
AUGUST 10, 2022
From mass production of cheap malware to ransomware as a service (RaaS) , cyber criminals have industrialized cybercrime, and a new HP Wolf Security report warns that cybercriminals are adapting advanced persistent threat (APT) tactics too. That means hackers will increasingly mimic nation-state threat groups by establishing a long-term presence inside networks to mine highly sensitive data.
Security Affairs
AUGUST 10, 2022
Cisco discloses a security breach, the Yanluowang ransomware group breached its corporate network in late May and stole internal data. Cisco disclosed a security breach, the Yanluowang ransomware group breached its corporate network in late May and stole internal data. The investigation conducted by Cisco Security Incident Response (CSIRT) and Cisco Talos revealed that threat actors compromised a Cisco employee’s credentials after they gained control of a personal Google account where credential

Hunton Privacy
AUGUST 9, 2022
On July 27, 2022, Google announced that it is delaying its plans to phase out third-party cookies in the Chrome web browser. Google’s Vice President of Privacy Sandbox, Anthony Chavez, announced the company is extending the full deprecation of third-party cookies to “the second half of 2024,” to continue the testing window for the Privacy Sandbox. Chavez indicated that Google extended the timeline after receiving consistent feedback that developers need more time to evaluate and test the new Pri

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

Data Breach Today
AUGUST 8, 2022
Penalties for Anyone in US Jurisdiction Who Uses the Cryptocurrency Mixer The federal government today sanctioned Tornado Cash. The Department of Treasury ordered assets of the Ethereum blockchain cryptocurrency mixer to be frozen and says civil and potentially criminal penalties await anyone under U.S. jurisdiction who uses the service.

KnowBe4
AUGUST 9, 2022
According to the CS Hub Mid-Year Market Report 2022, new findings shows that 75% of survey respondents believe that social engineering and phishing attacks are the top threat vector to cybersecurity within their organization.

Security Affairs
AUGUST 7, 2022
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. Greek intelligence service used surveillance malware to spy on a journalist, Reuters reports Slack resets passwords for about 0.5% of its users due to the exposure of salted password hashes Twitter confirms zero-day used to access data of 5.4 millio

Hunton Privacy
AUGUST 11, 2022
On August 11, 2022, the Federal Trade Commission announced it is seeking public comment regarding its advance notice of proposed rulemaking (“ANPR”) on commercial surveillance and data security, on which we previously reported. The FTC defines “commercial surveillance” as the business of collecting, analyzing and profiting from consumer data. Specifically, the FTC seeks comment on whether the Commission should implement new rules concerning the ways in which companies (1) collect, aggregate, pro

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.
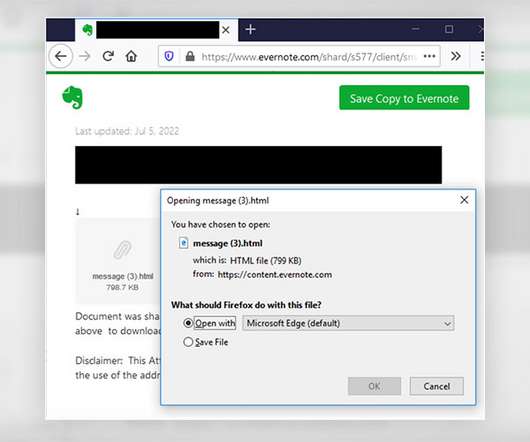
Data Breach Today
AUGUST 12, 2022
Scam Uses 'Secure Message' Theme and Trojan to Harvest Credentials A "secure message-themed" phishing campaign targeting healthcare providers aims to lure recipients to an Evernote notepad website in an attempt by hackers to harvest security credentials, federal authorities warn, saying the scheme puts entities at risk for potential data security compromises.

KnowBe4
AUGUST 11, 2022
In a recent article by Forbes, Cisco confirmed that they were hacked by a ransomware group as the group of cybercriminals published a partial list of files that were claimed to be exfiltrated.
Security Affairs
AUGUST 9, 2022
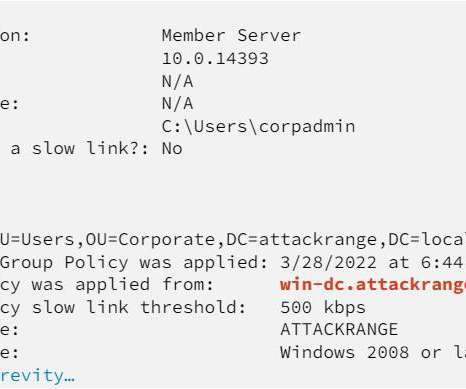
Microsoft Patch Tuesday security updates for August 2022 addressed a zero-day attack remote code execution vulnerability in Windows. Microsoft Patch Tuesday security updates for August 2022 addressed 118 CVEs in multiple products, including.NET Core, Active Directory Domain Services, Azure Batch Node Agent, Azure Real Time Operating System, Azure Site Recovery, Azure Sphere, Microsoft ATA Port Driver, Microsoft Bluetooth Driver, Microsoft Edge (Chromium-based), Microsoft Exchange Server, Microso

Dark Reading
AUGUST 9, 2022
A Q&A with NCC Group's Viktor Gazdag ahead of a Black Hat USA session on CI/CD pipeline risks reveals a scary, and expanding, campaign vector for software supply chain attacks and RCE.

Advertisement
Start-ups & SMBs launching products quickly must bundle dashboards, reports, & self-service analytics into apps. Customers expect rapid value from your product (time-to-value), data security, and access to advanced capabilities. Traditional Business Intelligence (BI) tools can provide valuable data analysis capabilities, but they have a barrier to entry that can stop small and midsize businesses from capitalizing on them.

Data Breach Today
AUGUST 8, 2022
Watters Can't Wait to Combine Google Analytics With Mandiant Intelligence Engine Combining the data analytics of Google Chronicle with Mandiant's ability to identify signals of abnormal behavior is an unbeatable combination, says Mandiant President and COO John Watters. Google agreed in March to purchase threat intelligence and incident response titan Mandiant for $5.4 billion.

KnowBe4
AUGUST 9, 2022
If you're a Coinbase user, you are most likely the next target of a new phishing campaign. Cybercriminals have managed to infiltrate two-factor authentication and deploying other social engineering strategies with the crypto currency exchange platform.

Security Affairs
AUGUST 10, 2022
Cisco addressed a high severity flaw, tracked as CVE-2022-20866, affecting Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) software. Cisco addressed a high severity vulnerability in its Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) software. The flaw, tracked as CVE-2022-20866 , impacts the handling of RSA keys on devices running Cisco ASA Software and FTD Software, an unauthenticated, remote attacker can trigger it to retrieve an RSA private key.
Let's personalize your content