A Dangerous Year in America Enters Its Most Dangerous Month
WIRED Threat Level
OCTOBER 5, 2020
Seven distinct factors between now and the election threaten to combine, compound, and reinforce each other in unpredictable ways.

WIRED Threat Level
OCTOBER 5, 2020
Seven distinct factors between now and the election threaten to combine, compound, and reinforce each other in unpredictable ways.

IT Governance
OCTOBER 5, 2020
Are you trying to figure out the best way to protect your organisation from cyber attacks and data breaches? It can be tricky to know where to begin, which is why our Cyber Security Risk Scorecard contains a simple guide to help you secure your systems. We’ve run through some of the essential steps in this blog, or download the full, free checklist from our website.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Dark Reading
OCTOBER 5, 2020
A new initiative will run throughout the month of October, invites the general public to play cybersecurity games (and win fabulous prizes).

Security Affairs
OCTOBER 5, 2020
A China-linked threat actor used UEFI malware based on code from Hacking Team in attacks aimed at organizations with an interest in North Korea. Researchers from Kaspersky have spotted a UEFI malware that was involved in attacks on organizations with an interest in North Korea. The experts were investigating several suspicious UEFI firmware images when discovered four components, some of which were borrowing the source code a Hacking Team spyware.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Krebs on Security
OCTOBER 9, 2020
A week ago, KrebsOnSecurity broke the news that someone was attempting to disrupt the Trickbot botnet , a malware crime machine that has infected millions of computers and is often used to spread ransomware. A new report Friday says the coordinated attack was part of an operation carried out by the U.S. military’s Cyber Command. Image: Shuttstock.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

WIRED Threat Level
OCTOBER 6, 2020
The Checkm8 vulnerability that exposed years of iPhones to jailbreaking has finally been exploited in Macs as well.

Security Affairs
OCTOBER 5, 2020
Threat actors have hacked at least three Swiss universities, including the University of Basel and managed to drain employee salary transfers. Threat actors have managed to steal employee salary payments at several Swiss universities, including the University of Basel. “According to our information, several universities in Switzerland have been affected,” explained Martina Weiss, Secretary General of the Rectors’ Conference of the Swiss Universities.

Krebs on Security
OCTOBER 8, 2020
There’s an old adage in information security: “Every company gets penetration tested, whether or not they pay someone for the pleasure.” Many organizations that do hire professionals to test their network security posture unfortunately tend to focus on fixing vulnerabilities hackers could use to break in. But judging from the proliferation of help-wanted ads for offensive pentesters in the cybercrime underground, today’s attackers have exactly zero trouble gaining that in

Data Breach Today
OCTOBER 5, 2020
In an exclusive interview, Roger Severino, director of the HHS Office for Civil Rights, which enforces HIPAA, spells out critical steps healthcare organizations must take to safeguard patient information and ensure patient safety in light of the surge in ransomware and other hacking incidents.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

WIRED Threat Level
OCTOBER 8, 2020
While it's still far more common on PCs, mobile ransomware has undergone a worrying evolution, new research shows.
Security Affairs
OCTOBER 5, 2020
Security researchers provided technical details about an IoT botnet dubbed Ttint that has been exploiting two zero-days in Tenda routers. Security researchers at Netlab, the network security division Qihoo 360, have published a report that details an IoT botnet dubbed Ttint. The experts are monitoring the Mirai-based botnet since November 2019 and observed it exploiting two Tenda router 0-day vulnerabilities to spread a Remote Access Trojan (RAT).

Krebs on Security
OCTOBER 7, 2020
September featured two stories on a phony tech investor named John Bernard , a pseudonym used by a convicted thief named John Clifton Davies who’s fleeced dozens of technology companies out of an estimated $30 million with the promise of lucrative investments. Those stories prompted a flood of tips from Davies’ victims that paint a much clearer picture of this serial con man and his cohorts, including allegations of hacking, smuggling, bank fraud and murder.

Data Breach Today
OCTOBER 3, 2020
Researchers Note Similarities to Sekhmet Crypto-Locking Malware Security researchers with Appgate are warning about a recently uncovered ransomware variant called Egregor that appears to have infected about a dozen organizations worldwide over the past several months. The gang behind this crypto-locking malware is threatening to release data if victims don't pay.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

WIRED Threat Level
OCTOBER 5, 2020
The tool attacks a device’s UEFI firmware—which makes it especially hard to detect and destroy.

Security Affairs
OCTOBER 3, 2020
University Hospital New Jersey paid a $670,000 ransom this month to prevent the leak of 240 GB of stolen data, including patient information. The University Hospital New Jersey (UHNJ) in Newark (New Jersey) has finally paid a $670,000 ransom to prevent the publishing of 240 GB of stolen data, including patient info. In September, systems at the University Hospital New Jersey (UHNJ) were encrypted with the SunCrypt ransomware , threat actors also stolen documents from the institution and leaked

AIIM
OCTOBER 6, 2020
Digitally Transforming IS the Future. Most organizations and departments have a mandate to continuously improve operations. A conventional change agenda involves better tools and technology, better behaviors, and better processes, all focused on generating better efficiencies and improved productivity - a transition called Digital Transformation. Ultimately, AIIM believes this Digital Transformation extends beyond conventional change.
Data Breach Today
OCTOBER 7, 2020
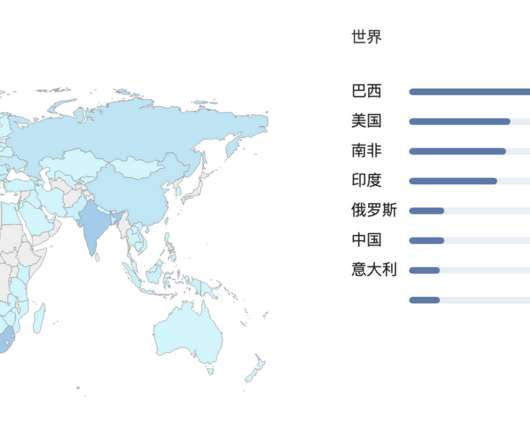
Yet Another Report Warns of Nation-State Influence Operations In the latest in a series of election security reports from government agencies, the U.S. Department of Homeland Security says Russia poses the most serious nation-state disruption threat to the U.S. presidential election, with China and Iran also posing threats.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

WIRED Threat Level
OCTOBER 8, 2020
The company, launched by Oculus cofounder Palmer Luckey, is building software to connect multiple Air Force systems—allowing officers to act more quickly.

Security Affairs
OCTOBER 4, 2020
Visa revealed that two unnamed North American hospitality merchants have been infected with some strains of point-of-sale (POS) malware. US payments processor Visa revealed that two North American hospitality merchants have been hacked, threat actors infected the systems of the two unnamed organizations with some strains of point-of-sale (POS) malware.

Data Protector
OCTOBER 4, 2020
We are what we are We don't want praise, we don't want pity We bang our own drum Some think it's noise, we think it's pretty We promise that your human rights we will not mangle We're the ones that try to see things from a different angle Join us we’re going far Join us and shout out Revise the GDPR We are what we are And what we are needs no excuses We’ll find a new way To cut out spam, stop data abuses Our private lives, there's no consent you get no look in Our private lives, you can't tell a
Data Breach Today
OCTOBER 5, 2020
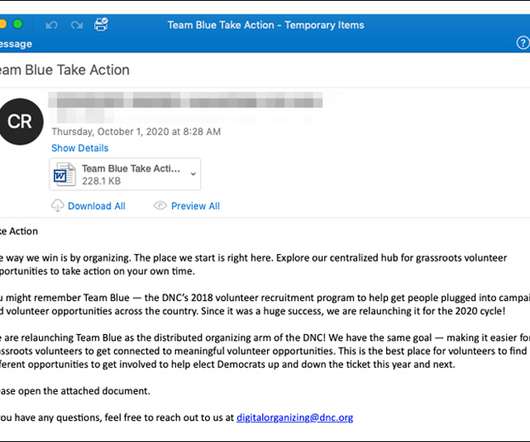
Proofpoint and KnowBe4 Spot Malicious Messages Disguised as Political Announcements Security researchers are warning of a fresh wave of phishing emails with election-related lures that are designed to get users to click, opening the door to spreading the Emotet botnet or harvesting users' credentials.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

WIRED Threat Level
OCTOBER 3, 2020
Plus: A Grindr bug, a Joker explosion, and more of the week's top security news.

Security Affairs
OCTOBER 8, 2020
Cybersecurity researchers from Cyble have spotted a threat actor sharing leaked data of Airlink International UAE for free on two different platforms. Cybersecurity researchers from Cyble have found a threat actor sharing leaked data of Airlink International UAE for free on two platforms on the dark web. The availability of the data on the dark web could pose organizations to serious risk, threat actors could use this data to carry out multiple malicious attacks.

erwin
OCTOBER 8, 2020
More and more companies are looking at cloud migration. Migrating legacy data to public, private or hybrid clouds provide creative and sustainable ways for organizations to increase their speed to insights for digital transformation, modernize and scale their processing and storage capabilities, better manage and reduce costs, encourage remote collaboration, and enhance security, support and disaster recovery.

Data Breach Today
OCTOBER 9, 2020
The latest edition of the ISMG Security Report analyzes why clothing retailer H&M was hit with a hefty fine for violating the EU's General Data Protection Rule. Also featured: The coming of age of digital identities; deputy CSO at Mastercard on top priorities for 2021.

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.
WIRED Threat Level
OCTOBER 7, 2020
The latest Gboard feature needs to know as much as possible about your digital life to work—but doesn't share that data with Google.

Security Affairs
OCTOBER 4, 2020
HP published details of three vulnerabilities in the HP Device Manager that could be exploited by attackers to take over Windows systems. HP released a security advisory that includes details for three critical and high severity vulnerabilities, tracked as CVE-2020-6925, CVE-2020-6926, and CVE-2020-6927, that impact the HP Device Manager. The IT giant revealed that an attacker could exploit the vulnerabilities to take over Windows systems.
Let's personalize your content