Most Americans Fail Cybersecurity Quiz
Threatpost
OCTOBER 9, 2019
Study participants fail to correctly identify core security concepts and tools to help them stay safe online.

Threatpost
OCTOBER 9, 2019
Study participants fail to correctly identify core security concepts and tools to help them stay safe online.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Guardian Data Protection
OCTOBER 8, 2019
David Omand warns festival Cheltenham festival audience of threat to democracy from monetisation of data Big internet firms know more about the lives of private individuals than any intelligence agency ever has and that is a dangerous threat to democracy, the former head of the spy agency GCHQ has said. David Omand was at the centre of British intelligence for decades, beginning his career at GCHQ after he graduated from Cambridge in 1969 and becoming its director from 1996-97.

Data Breach Today
OCTOBER 7, 2019
Pulse Secure, Palo Alto and Fortinet Devices Being Hit by APT Groups, NCSC Warns Nation-state attackers have been targeting known flaws that customers have yet to patch in their Pulse Secure, Palo Alto and Fortinet VPN servers, Britain's National Cyber Security Center warns, adding that any organization that didn't immediately apply patches should review logs for signs of hacking.
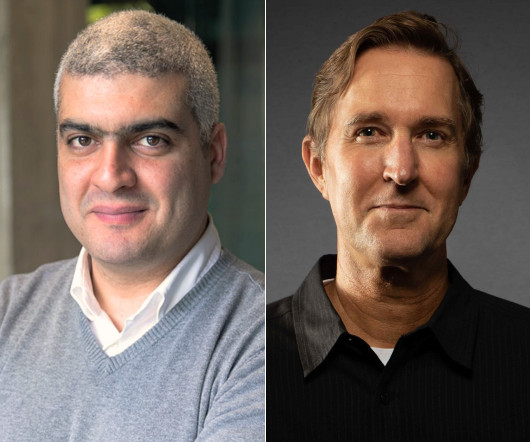
Speaker: Maher Hanafi, VP of Engineering at Betterworks & Tony Karrer, CTO at Aggregage
Executive leaders and board members are pushing their teams to adopt Generative AI to gain a competitive edge, save money, and otherwise take advantage of the promise of this new era of artificial intelligence. There's no question that it is challenging to figure out where to focus and how to advance when it’s a new field that is evolving everyday. 💡 This new webinar featuring Maher Hanafi, CTO of Betterworks, will explore a practical framework to transform Generative AI prototypes into

The Last Watchdog
OCTOBER 10, 2019
Cloud Access Security Brokers – aka “caz-bees” — have come a long way in a short time. CASBs, a term coined by tech industry consultancy Gartner, first cropped about seven years ago to help organizations enforce security and governance policies as they commenced, in earnest, their march into the cloud. Related: Implications of huge Capital One breach CASBs supplied a comprehensive set of tools to monitor and manage the multitude of fresh cyber risks spinning out of the rise in in corporate
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Thales Cloud Protection & Licensing
OCTOBER 10, 2019
It’s hard to believe it’s mid-October. Along with autumn, comes National Cybersecurity Awareness Month (NCSAM). The NCSAM 2019 focuses on personal accountability. Driven through mass public engagement, the ‘Own IT. Secure. IT. Protect IT.’ theme will help to encourage personal accountability and proactive behavior in digital privacy, security best practices, common cyber threats and cybersecurity careers.

Data Breach Today
OCTOBER 10, 2019
Europol Report: Ransomware, DDoS, Business Email Compromises Are Persistent Threats Online attack threats continue to intensify, with criminals preferring ransomware, DDoS attacks and business email compromises, warns Europol, the EU's law enforcement intelligence agency. After numerous successful disruptions by police, criminals have responded by launching increasingly complex attacks.

The Last Watchdog
OCTOBER 9, 2019
To pay or not to pay? That’s the dilemma hundreds of organizations caught in the continuing surge of crippling ransomware attacks have faced. Related: How ransomware became such a scourge The FBI discourages it, as you might have guessed. What’s more, the U.S. Conference of Mayors this summer even passed a resolution declaring paying hackers for a decryption key anathema.

Security Affairs
OCTOBER 11, 2019
With the right cybersecurity certifications, you can attain your goals seamlessly and in a fast way and speed up your career. Cyber attacks are making headlines almost every day in today’s era. The attacks have increased both in number and complexity. Because of this natural demand, it is now crucial for companies and specialized firms to reinforce and invest in professionals to face a problem that technology can’t solve.

Advertisement
Generative AI is upending the way product developers & end-users alike are interacting with data. Despite the potential of AI, many are left with questions about the future of product development: How will AI impact my business and contribute to its success? What can product managers and developers expect in the future with the widespread adoption of AI?

Schneier on Security
OCTOBER 8, 2019
Two speakers were censored at the Australian Information Security Association's annual conference this week in Melbourne. Thomas Drake , former NSA employee and whistleblower, was scheduled to give a talk on the golden age of surveillance, both government and corporate. Suelette Dreyfus , lecturer at the University of Melbourne, was scheduled to give a talk on her work -- funded by the EU government -- on anonymous whistleblowing technologies like Dropbox and how they reduce corruption in countr

Data Breach Today
OCTOBER 7, 2019
Google Security Evangelist Mike Burr Describes Android Security Measures Mike Burr of Google provides an overview of Android security efforts, including using artificial intelligence to scan Android apps.

The Last Watchdog
OCTOBER 7, 2019
It seems like any discussion of cybersecurity these days invariably circles back to automation. Our growing fixation with leveraging artificial intelligence to extract profits from Big Data – for both constructive and criminal ends—is the order of the day. Related: Why Cyber Pearl Harbor is upon us Vigilante is a cybersecurity startup that cuts against that grain.

Security Affairs
OCTOBER 7, 2019
Researchers at Fortinet’s FortiGuard Labs have publicly disclosed a critical remote code execution vulnerability affecting some models of D-Link routers. Security experts at Fortinet’s FortiGuard Labs disclosed a remote code execution vulnerability tracked as CVE-2019-16920. The vulnerability is an unauthenticated command injection issue that was discovered on September 2019.
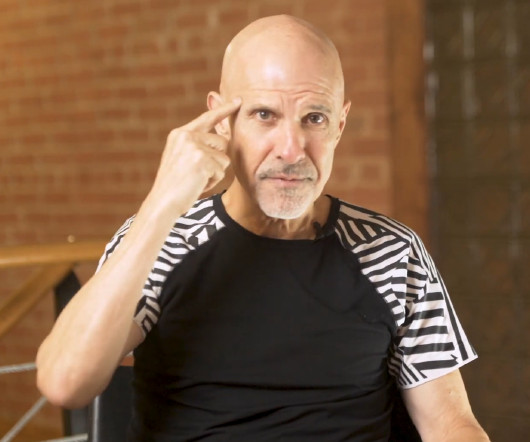
Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

Dark Reading
OCTOBER 9, 2019
How a new open source initiative for interoperable security tools and a wave of consolidation could finally provide some relief for overwhelmed security analysts and SOCs.

Data Breach Today
OCTOBER 9, 2019
Threat Actors Using Social Engineering, Other Technical Techniques to Circumvent MFA Protections The FBI is warning banks, businesses and other organizations that cybercriminals are using social engineering and other technical techniques to circumvent multifactor authentication security protections.

Schneier on Security
OCTOBER 9, 2019
Interesting : German investigators said Friday they have shut down a data processing center installed in a former NATO bunker that hosted sites dealing in drugs and other illegal activities. Seven people were arrested. [.]. Thirteen people aged 20 to 59 are under investigation in all, including three German and seven Dutch citizens, Brauer said. Authorities arrested seven of them, citing the danger of flight and collusion.

Security Affairs
OCTOBER 11, 2019
Good news for the victims of the Nemty Ransomware , security researchers have released a free decryptor that could be used to recover files. I have great news for the victims of the recently discovered Nemty Ransomware , security researchers have released a free decryptor tool that could be used to recover files. In mid-August, the Nemty ransomware appeared in the threat landscape, the name of the ransomware comes after the extension it adds to the encrypted file names.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

Dark Reading
OCTOBER 10, 2019
One in four malicious URLs employed a legitimate domain, making it more difficult for potential victims to spot possible dangers, a mid-year report finds.

Data Breach Today
OCTOBER 10, 2019
Audit Finds Agencies Not Following State's Cybersecurity Law The personal data of Mississippi citizens is susceptible to breaches because many state agencies, universities and other organizations are failing to comply with all the mandates of the state's cybersecurity law, according to a report issued by the Office of the State Auditor.

IT Governance
OCTOBER 10, 2019
The ISO/IEC 270001 family of standards, also known as the ISO 27000 series, is a series of best practices to help organisations improve their information security. Published by ISO (the International Organization for Standardization) and the IEC (International Electrotechnical Commission) , the series explains how to implement an ISMS (information security management system).

Security Affairs
OCTOBER 6, 2019
A database containing details of 92 million Brazilians was auctioned by a threat actor on underground forums along with a search service focused on Brazilians. Someone is auctioning on several restricted underground forums a database containing personal information of 92 million Brazilian citizens. The threat actor, registered as X4Crow, is also advertising a search service that allows retrieving detailed information on Brazilian citizens.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Dark Reading
OCTOBER 10, 2019
In the arms race of computer security, it's never been more important to develop an adversarial mindset that can identify assumptions and determine if and how they can be violated.

Data Breach Today
OCTOBER 11, 2019
Prosecutors, Defense Attorneys Ask Judge for Delay, Citing Massive Amounts of Data to Review Defense and prosecution attorneys are asking for a delay in the trial of alleged Capital One hacker Paige A. Thompson, citing the overwhelming amount of digital evidence in the case and the ongoing forensics investigation. Prosecutors also expect to file additional charges.

Schneier on Security
OCTOBER 10, 2019
Free Wi-Fi hotspots can track your location , even if you don't connect to them. This is because your phone or computer broadcasts a unique MAC address. What distinguishes location-based marketing hotspot providers like Zenreach and Euclid is that the personal information you enter in the captive portal -- like your email address, phone number, or social media profile -- can be linked to your laptop or smartphone's Media Access Control (MAC) address.

Security Affairs
OCTOBER 9, 2019
Hackers have compromised the infrastructure of Volusion and are distributing malicious software skimmers to steal payment card data provided by users. Volusion is a privately-held technology company that provides ecommerce software and marketing and web design services for small and medium sized businesses. The company has over 250 employees and has served more than 180,000 customers since its founding in 1999.

Advertisement
Start-ups & SMBs launching products quickly must bundle dashboards, reports, & self-service analytics into apps. Customers expect rapid value from your product (time-to-value), data security, and access to advanced capabilities. Traditional Business Intelligence (BI) tools can provide valuable data analysis capabilities, but they have a barrier to entry that can stop small and midsize businesses from capitalizing on them.

OpenText Information Management
OCTOBER 7, 2019
Today, supply chains are considered strategic to the business, and meeting customer expectations for ethical and sustainable supply chain operations is increasingly becoming a top priority for supply chain managers. Last year, supply chain research specialists APICS found that 83% of supply chain professionals thought ethics were extremely or very important for their organization.

Data Breach Today
OCTOBER 10, 2019
To ensure privacy is protected, governments need to make sure standards and regulations keep pace with the latest technology developments, including facial recognition and other forms of artificial intelligence, says Steven Feldstein, an associate professor at Boise State University.

Schneier on Security
OCTOBER 8, 2019
A new iOS exploit allows jailbreaking of pretty much all version of the iPhone. This is a huge deal for Apple, but at least it doesn't allow someone to remotely hack people's phones. Some details : I wanted to learn how Checkm8 will shape the iPhone experience -- particularly as it relates to security -- so I spoke at length with axi0mX on Friday.
Let's personalize your content