Selecting an Intelligent Document Processing Solution
AIIM
NOVEMBER 14, 2024
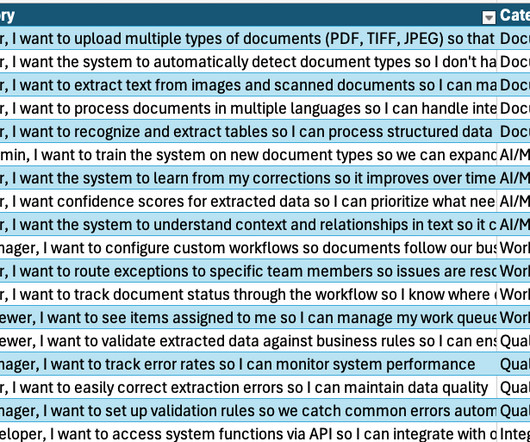
Intelligent document processing (IDP) solutions are emerging that combine AI with IDP to revolutionize client and document onboarding and processing. Particularly useful in the printing, financial services, banking, insurance and healthcare industries, these solutions automate traditionally manual and time-consuming document tasks, drastically reducing onboarding times and errors.































Let's personalize your content