The Rising Importance of Information Management in the Age of AI
AIIM
SEPTEMBER 17, 2024
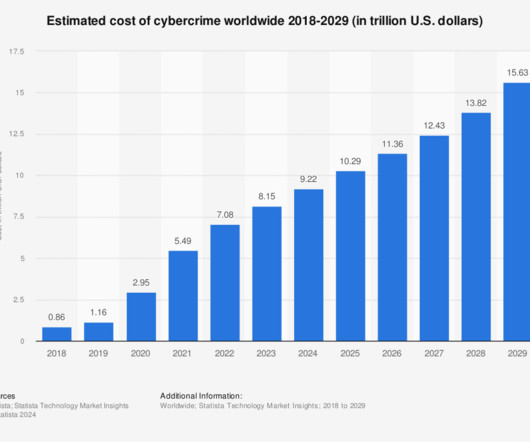
As the potential of Generative AI (Gen AI) continues to unfold, one resounding theme emerges: better AI starts with better information management. The ability of Gen AI to deliver reliable and valuable outputs is directly contingent upon the quality and curation of the underlying data.





































Let's personalize your content