Exploit for Critical Windows Defender Bypass Goes Public
Dark Reading
NOVEMBER 21, 2023
Threat actors were actively exploiting CVE-2023-36025 in Windows SmartScreen as a zero-day vulnerability before Microsoft patched it in November.

Dark Reading
NOVEMBER 21, 2023
Threat actors were actively exploiting CVE-2023-36025 in Windows SmartScreen as a zero-day vulnerability before Microsoft patched it in November.

WIRED Threat Level
NOVEMBER 20, 2023
A WIRED analysis of leaked police documents verifies that a secretive government program is allowing federal, state, and local law enforcement to access phone records of Americans who are not suspected of a crime.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
NOVEMBER 20, 2023
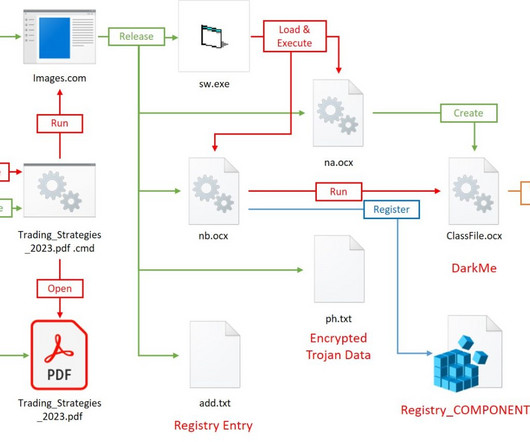
The DarkCasino APT group leveraged a recently disclosed WinRAR zero-day vulnerability tracked as CVE-2023-38831. Researchers at cybersecurity firm NSFOCUS analyzed DarkCasino attack pattern exploiting the WinRAR zero-day vulnerability tracked as CVE-2023-38831. The economically motivated APT group used specially crafted archives in phishing attacks against forum users through online trading forum posts. “DarkCasino is an APT threat actor with strong technical and learning ability, who is g

The Last Watchdog
NOVEMBER 19, 2023
A hacking gang known as Scattered Spiders soundly defeated the cybersecurity defenses of MGM and Caesars casinos. Related: Russia puts the squeeze on US supply chain This cost the Las Vegas gambling meccas more than $100 million while damaging their reputations. As the companies face nine federal lawsuits for failing to protect customer data, it’s abundantly clear hackers have checkmated multi-factor authentication (MFA).

Speaker: Frank Taliano
Document-heavy workflows slow down productivity, bury institutional knowledge, and drain resources. But with the right AI implementation, these inefficiencies become opportunities for transformation. So how do you identify where to start and how to succeed? Learn how to develop a clear, practical roadmap for leveraging AI to streamline processes, automate knowledge work, and unlock real operational gains.

Data Breach Today
NOVEMBER 23, 2023
Also, Kansas Courts Say Ongoing Outage Traces to Attack; Confidential Data Stolen This week's data breach roundup: Chinese-affiliated hackers target the Philippine government; Kansas Courts confirm data theft; officials warn of exploited flaws in Sophos, Oracle and Microsoft software; AutoZone discloses a Clop ransomware attack; Optus' CEO resigns after network outage.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.
Security Affairs
NOVEMBER 24, 2023
Almost a million files with minors’ data, including home addresses and photos were left open to anyone on the internet, posing a threat to children. During a recent investigation, the Cybernews research team discovered that IT company Appscook – which develops applications used by more than 600 schools in India and Sri Lanka for education management – leaked a staggering amount of sensitive data, including photos of minors, home addresses, and birth certificates, due to a misconfiguration

AIIM
NOVEMBER 21, 2023
Recently, I was lucky enough to be part of a networking group that got to see a real world demo of Chat GPT in a highly practical use case. The use case was focused on internal search within an organization and utilized the strengths of Chat GPT as a Large Language Model (LLM). The organization demonstrating the use case explained they used a conversational use interface (UI) that focused on user experience and making it easier for the user to find the information they were looking for without h

Data Breach Today
NOVEMBER 20, 2023
77 Million Individuals' Information Exposed, as More Victims Continue to Be Counted Trackers of the tally of individuals affected by the Clop ransomware group's mass hack attack on MOVEit servers added another 4.5 million patients' data to the ever-ascending total. The incident currently affects more than 2,600 organizations and 77 million individuals.

WIRED Threat Level
NOVEMBER 21, 2023
From Russia to Iran, the feds have charged Binance with allegedly conducting well over $1 billion in transactions with sanctioned countries and criminal actors.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.
Security Affairs
NOVEMBER 19, 2023
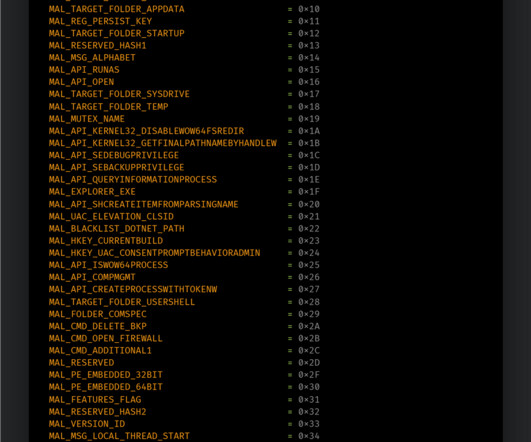
8Base ransomware operators were observed using a variant of the Phobos ransomware in a recent wave of attacks. Cisco Talos researchers observed 8Base ransomware operators using a variant of the Phobos ransomware in recent attacks. Phobos variants are usually distributed by the SmokeLoader , but in 8Base campaigns, it has the ransomware component embedded in its encrypted payloads.

Dark Reading
NOVEMBER 20, 2023
China pairs cyber and kinetic attacks in the South Pacific as it continues to wrangle control of the South China Sea.

Data Breach Today
NOVEMBER 20, 2023
OpenAI Board Thwarts Altman's Return, Names Ex-Twitch Boss Emmett Shear Interim CEO OpenAI co-founders Sam Altman and Greg Brockman will lead a new advanced AI research team at Microsoft after OpenAI's board decided not to bring them back, Satya Nadella said. The nonprofit behind ChatGPT opted instead to name longtime Twitch CEO Emmett Shear as its new interim leader Sunday night.
WIRED Threat Level
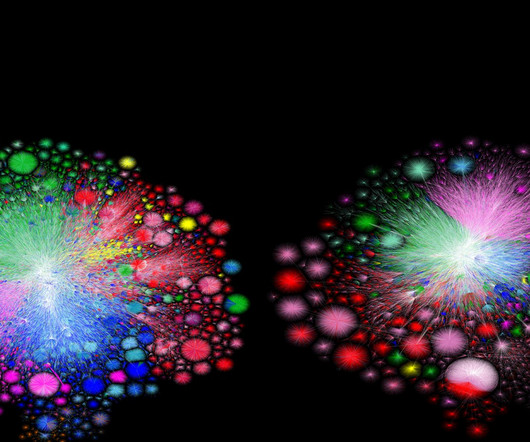
NOVEMBER 24, 2023
Security researcher Barrett Lyon, who makes visualizations of the internet's network infrastructure, is back with a new piece chronicling the rise of the IPv6 protocol.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m
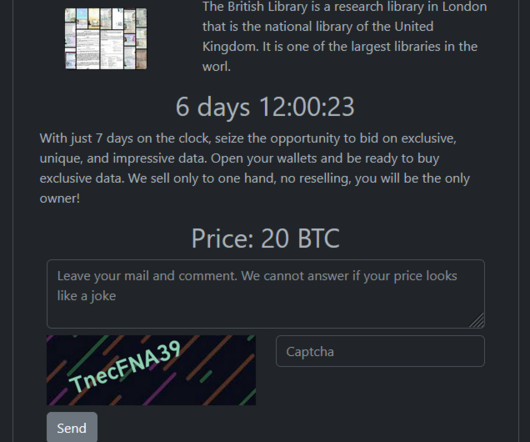
Security Affairs
NOVEMBER 20, 2023
The Rhysida ransomware group claimed responsibility for the recent cyberattack on the British Library that has caused a major IT outage. The Rhysida ransomware gang added the British Library to the list of victims on its Tor leak site. The British Library is a research library in London that is the national library of the United Kingdom. It is one of the largest libraries in the world.

Thales Cloud Protection & Licensing
NOVEMBER 21, 2023
Thales and HPE GreenLake Expand Partnership to Offer Enhanced Data Protection sparsh Wed, 11/22/2023 - 06:41 In a significant stride towards bolstering data security and simplifying key management, Thales is thrilled to announce an expanded partnership with HPE GreenLake. This newfound collaboration paves the way for launching a Centralized Key Management complimentary product offering, an initiative poised to reshape the landscape of data protection and security for enterprises worldwide.

Data Breach Today
NOVEMBER 21, 2023
LockBit and Nation-State Groups Using Session Tokens to Access Patched Devices With experts warning that NetScaler ADC and Gateway devices are being exploited by nation-state and cybercrime groups, the manufacturer has again urged all users to "patch immediately as well as terminate active sessions, which attackers can otherwise use to access devices even post-patch.

WIRED Threat Level
NOVEMBER 18, 2023
Plus: The FBI's baffling inaction on a ransomware group, a massive breach of Danish electric utilities, and more.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

Security Affairs
NOVEMBER 24, 2023
Researchers warn of publicly exposed Kubernetes configuration secrets that could pose a threat of supply chain attack for organizations. Aqua Nautilus researchers warn of publicly exposed Kubernetes configuration secrets that put organizations at risk of supply chain attacks. The experts noticed that these misconfigurations impact hundreds of organizations and open-source projects.

CGI
NOVEMBER 22, 2023
Founded in 1976, CGI is among the largest IT and business consulting services firms in the world. We are insights-driven and outcomes-based to help accelerate returns on your investments.

Data Breach Today
NOVEMBER 21, 2023
Hacktivists Leak Sensitive Employee Information From Idaho National Laboratory The hacktivist group SiegedSec has taken responsibility for a massive data breach targeting Idaho National Laboratory, a leading nuclear energy testing lab. Concerns are now growing over what data was stolen from the laboratory - and who might have access to it.

WIRED Threat Level
NOVEMBER 18, 2023
Beyond the blinding speeds and sharp turns on new terrain, the teams at this weekend’s big F1 race are preparing for another kind of danger.

Speaker: Yohan Lobo and Dennis Street
In the accounting world, staying ahead means embracing the tools that allow you to work smarter, not harder. Outdated processes and disconnected systems can hold your organization back, but the right technologies can help you streamline operations, boost productivity, and improve client delivery. Dive into the strategies and innovations transforming accounting practices.
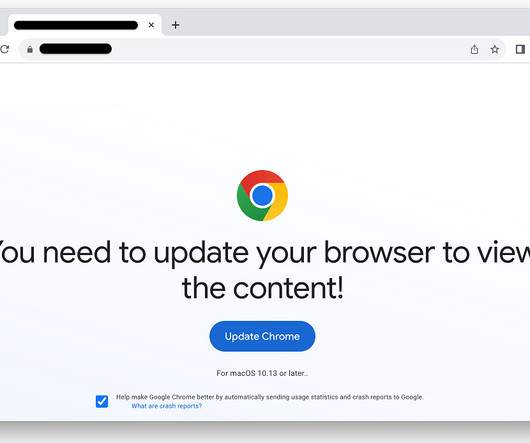
Security Affairs
NOVEMBER 23, 2023
Threat actors spread Atomic Stealer (AMOS) macOS information stealer via a bogus web browser update as part of the ClearFake campaign. Atomic Stealer (AMOS) macOS information stealer is now being delivered via a fake browser update chain tracked as ClearFake, Malwarebytes researchers warn. The malware focuses on macOS, designed to pilfer sensitive information from the compromised systems.

Schneier on Security
NOVEMBER 20, 2023
Generative AI is going to be a powerful tool for data analysis and summarization. Here’s an example of it being used for sentiment analysis. My guess is that it isn’t very good yet, but that it will get better.

Data Breach Today
NOVEMBER 23, 2023
Also: Kronos Loses $25 Million via API Breach; Regulators Charge Kraken This week's cryptocurrency hack roundup features hackers stealing $87 million from Heco, Kronos reporting $25 million stolen via an API breach, regulators filing charges against Kraken, feds charging three people with stealing $10 million as well as seizing $9 million tied to a pig butchering scam.

KnowBe4
NOVEMBER 22, 2023
Another day, another warning about holiday scams! Lookout Inc., a data-centric cloud security company, is warning employees and businesses that phishing attacks are expected to more than double this week , based on historical data. With more corporate data residing in the cloud and a massive amount of employees still working remotely, mobile has become the endpoint of choice for the modern workforce.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!
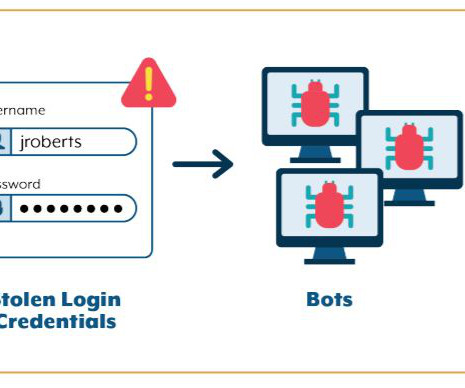
Security Affairs
NOVEMBER 20, 2023
US teenager Joseph Garrison pleads guilty to carrying out a credential stuffing attack on a betting website. US teenager Joseph Garrison (19) has pleaded guilty to his involvement in a credential stuffing campaign that targeted user accounts at a fantasy sports and betting website.3 On or about November 18, 2022, the man launched a credential stuffing attack on the Betting Website and gained access to approximately 60,000 accounts.

Schneier on Security
NOVEMBER 22, 2023
Signal has had the ability to manually authenticate another account for years. iMessage is getting it : The feature is called Contact Key Verification, and it does just what its name says: it lets you add a manual verification step in an iMessage conversation to confirm that the other person is who their device says they are. (SMS conversations lack any reliable method for verification—sorry, green-bubble friends.

Data Breach Today
NOVEMBER 23, 2023
Supply Chain Attacks: Hackers Target Zero-Days in Widely Used Software, Alert Warns North Korean state-affiliated hackers are continuing to exploit zero-days in popular software applications as part of global supply chain attack campaigns for espionage and financial theft purposes, British and South Korean cybersecurity and intelligence officials said.
Let's personalize your content