Exploit for Critical Windows Defender Bypass Goes Public
Dark Reading
NOVEMBER 21, 2023
Threat actors were actively exploiting CVE-2023-36025 in Windows SmartScreen as a zero-day vulnerability before Microsoft patched it in November.

Dark Reading
NOVEMBER 21, 2023
Threat actors were actively exploiting CVE-2023-36025 in Windows SmartScreen as a zero-day vulnerability before Microsoft patched it in November.

The Last Watchdog
NOVEMBER 19, 2023
A hacking gang known as Scattered Spiders soundly defeated the cybersecurity defenses of MGM and Caesars casinos. Related: Russia puts the squeeze on US supply chain This cost the Las Vegas gambling meccas more than $100 million while damaging their reputations. As the companies face nine federal lawsuits for failing to protect customer data, it’s abundantly clear hackers have checkmated multi-factor authentication (MFA).
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
NOVEMBER 23, 2023
Also, Kansas Courts Say Ongoing Outage Traces to Attack; Confidential Data Stolen This week's data breach roundup: Chinese-affiliated hackers target the Philippine government; Kansas Courts confirm data theft; officials warn of exploited flaws in Sophos, Oracle and Microsoft software; AutoZone discloses a Clop ransomware attack; Optus' CEO resigns after network outage.

AIIM
NOVEMBER 21, 2023
Recently, I was lucky enough to be part of a networking group that got to see a real world demo of Chat GPT in a highly practical use case. The use case was focused on internal search within an organization and utilized the strengths of Chat GPT as a Large Language Model (LLM). The organization demonstrating the use case explained they used a conversational use interface (UI) that focused on user experience and making it easier for the user to find the information they were looking for without h
Speaker: Maher Hanafi, VP of Engineering at Betterworks & Tony Karrer, CTO at Aggregage
Executive leaders and board members are pushing their teams to adopt Generative AI to gain a competitive edge, save money, and otherwise take advantage of the promise of this new era of artificial intelligence. There's no question that it is challenging to figure out where to focus and how to advance when it’s a new field that is evolving everyday. 💡 This new webinar featuring Maher Hanafi, CTO of Betterworks, will explore a practical framework to transform Generative AI prototypes into

WIRED Threat Level
NOVEMBER 20, 2023
A WIRED analysis of leaked police documents verifies that a secretive government program is allowing federal, state, and local law enforcement to access phone records of Americans who are not suspected of a crime.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Data Breach Today
NOVEMBER 20, 2023
77 Million Individuals' Information Exposed, as More Victims Continue to Be Counted Trackers of the tally of individuals affected by the Clop ransomware group's mass hack attack on MOVEit servers added another 4.5 million patients' data to the ever-ascending total. The incident currently affects more than 2,600 organizations and 77 million individuals.
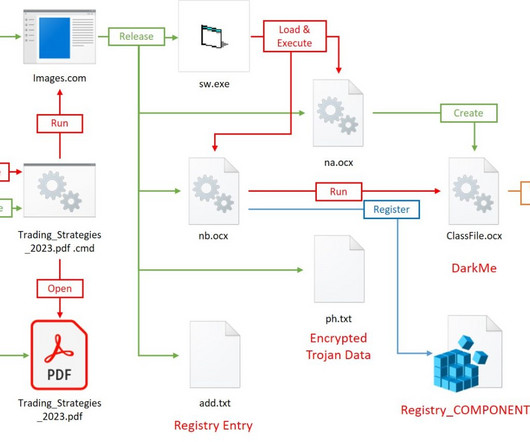
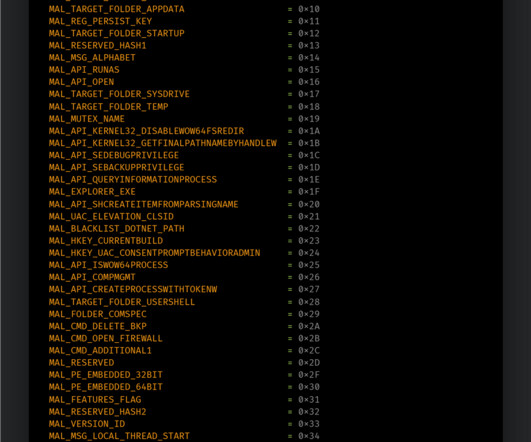
Security Affairs
NOVEMBER 20, 2023
The DarkCasino APT group leveraged a recently disclosed WinRAR zero-day vulnerability tracked as CVE-2023-38831. Researchers at cybersecurity firm NSFOCUS analyzed DarkCasino attack pattern exploiting the WinRAR zero-day vulnerability tracked as CVE-2023-38831. The economically motivated APT group used specially crafted archives in phishing attacks against forum users through online trading forum posts. “DarkCasino is an APT threat actor with strong technical and learning ability, who is g

WIRED Threat Level
NOVEMBER 21, 2023
The North Atlantic Fellas Organization is trying to shut down Trump’s flailing social media platform before the 2024 election—by shitposting.

Dark Reading
NOVEMBER 20, 2023
China pairs cyber and kinetic attacks in the South Pacific as it continues to wrangle control of the South China Sea.

Advertisement
Generative AI is upending the way product developers & end-users alike are interacting with data. Despite the potential of AI, many are left with questions about the future of product development: How will AI impact my business and contribute to its success? What can product managers and developers expect in the future with the widespread adoption of AI?

Data Breach Today
NOVEMBER 20, 2023
OpenAI Board Thwarts Altman's Return, Names Ex-Twitch Boss Emmett Shear Interim CEO OpenAI co-founders Sam Altman and Greg Brockman will lead a new advanced AI research team at Microsoft after OpenAI's board decided not to bring them back, Satya Nadella said. The nonprofit behind ChatGPT opted instead to name longtime Twitch CEO Emmett Shear as its new interim leader Sunday night.
Security Affairs
NOVEMBER 19, 2023
8Base ransomware operators were observed using a variant of the Phobos ransomware in a recent wave of attacks. Cisco Talos researchers observed 8Base ransomware operators using a variant of the Phobos ransomware in recent attacks. Phobos variants are usually distributed by the SmokeLoader , but in 8Base campaigns, it has the ransomware component embedded in its encrypted payloads.

KnowBe4
NOVEMBER 22, 2023
Another day, another warning about holiday scams! Lookout Inc., a data-centric cloud security company, is warning employees and businesses that phishing attacks are expected to more than double this week , based on historical data. With more corporate data residing in the cloud and a massive amount of employees still working remotely, mobile has become the endpoint of choice for the modern workforce.

WIRED Threat Level
NOVEMBER 23, 2023
There’s a devastating amount of heavy news these days. Psychology experts say you need to know your limits—and when to put down the phone.
Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

Data Breach Today
NOVEMBER 21, 2023
LockBit and Nation-State Groups Using Session Tokens to Access Patched Devices With experts warning that NetScaler ADC and Gateway devices are being exploited by nation-state and cybercrime groups, the manufacturer has again urged all users to "patch immediately as well as terminate active sessions, which attackers can otherwise use to access devices even post-patch.
Security Affairs
NOVEMBER 23, 2023
Threat actors spread Atomic Stealer (AMOS) macOS information stealer via a bogus web browser update as part of the ClearFake campaign. Atomic Stealer (AMOS) macOS information stealer is now being delivered via a fake browser update chain tracked as ClearFake, Malwarebytes researchers warn. The malware focuses on macOS, designed to pilfer sensitive information from the compromised systems.

Dark Reading
NOVEMBER 22, 2023
The actor behind the high-profile MGM incident jumps across segmentations in under an hour, in a ransomware attack spanning Okta, Citrix, Azure, SharePoint, and more.

Schneier on Security
NOVEMBER 22, 2023
Signal has had the ability to manually authenticate another account for years. iMessage is getting it : The feature is called Contact Key Verification, and it does just what its name says: it lets you add a manual verification step in an iMessage conversation to confirm that the other person is who their device says they are. (SMS conversations lack any reliable method for verification—sorry, green-bubble friends.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

Data Breach Today
NOVEMBER 21, 2023
Hacktivists Leak Sensitive Employee Information From Idaho National Laboratory The hacktivist group SiegedSec has taken responsibility for a massive data breach targeting Idaho National Laboratory, a leading nuclear energy testing lab. Concerns are now growing over what data was stolen from the laboratory - and who might have access to it.
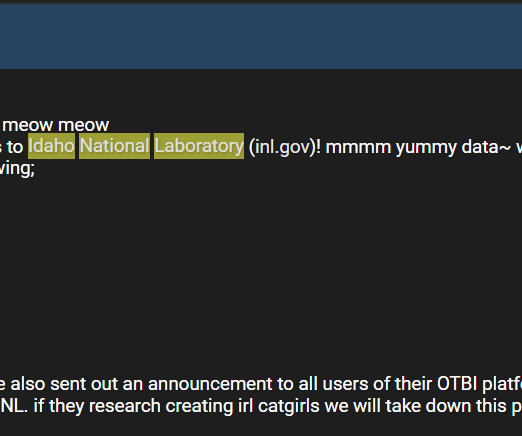
Security Affairs
NOVEMBER 22, 2023
The Idaho National Laboratory (INL) disclosed a data breach after the SiegedSec hacktivist group leaked stolen human resources data. SiegedSec hacktivists group claimed responsibility for the hack of The Idaho National Laboratory (INL) and leaked stolen human resources data. SiegedSec is a threat actor that last year carried out multiple attacks against U.S. organizations, especially U.S. municipalities.

IBM Big Data Hub
NOVEMBER 20, 2023
Advanced organizations know their greatest assets are their employees. However, keeping employees happy and engaged can be challenging, especially when considering available resources and the need to meet other organizational goals. An organization is only as strong as its talent pool, so organizations have increasingly embraced talent management as a core component of their overarching strategy.

KnowBe4
NOVEMBER 21, 2023
Scammers are using a compromised X (formerly Twitter) account belonging to Bloomberg Crypto to send users to a phishing site designed to steal Discord credentials, BleepingComputer reports.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Data Breach Today
NOVEMBER 23, 2023
Also: Kronos Loses $25 Million via API Breach; Regulators Charge Kraken This week's cryptocurrency hack roundup features hackers stealing $87 million from Heco, Kronos reporting $25 million stolen via an API breach, regulators filing charges against Kraken, feds charging three people with stealing $10 million as well as seizing $9 million tied to a pig butchering scam.
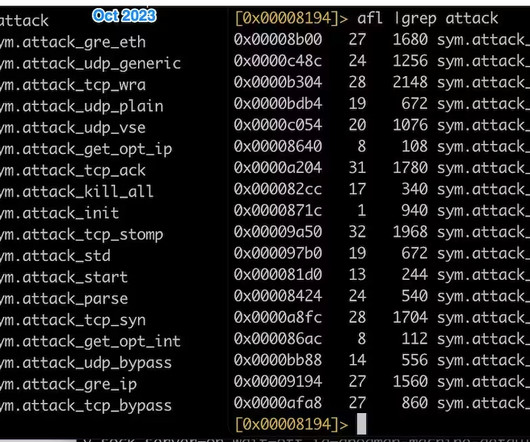
Security Affairs
NOVEMBER 22, 2023
Mirai-based botnet InfectedSlurs has been spotted exploiting two zero-day RCE flaws to compromise routers and video recorder (NVR) devices. Akamai discovered a new Mirai-based DDoS botnet, named InfectedSlurs, actively exploiting two zero-day vulnerabilities to infect routers and video recorder (NVR) devices. The researchers discovered the botnet in October 2023, but they believe it has been active since at least 2022.

IBM Big Data Hub
NOVEMBER 21, 2023
Apache Kafka is a well-known open-source event store and stream processing platform and has grown to become the de facto standard for data streaming. In this article, developer Michael Burgess provides an insight into the concept of schemas and schema management as a way to add value to your event-driven applications on the fully managed Kafka service, IBM Event Streams on IBM Cloud ® What is a schema?

Schneier on Security
NOVEMBER 20, 2023
Generative AI is going to be a powerful tool for data analysis and summarization. Here’s an example of it being used for sentiment analysis. My guess is that it isn’t very good yet, but that it will get better.

Advertisement
Start-ups & SMBs launching products quickly must bundle dashboards, reports, & self-service analytics into apps. Customers expect rapid value from your product (time-to-value), data security, and access to advanced capabilities. Traditional Business Intelligence (BI) tools can provide valuable data analysis capabilities, but they have a barrier to entry that can stop small and midsize businesses from capitalizing on them.

Data Breach Today
NOVEMBER 24, 2023
Parliamentarians Pass Resolution Calling For Immediate Executive Branch Action European lawmakers slammed the EU executive branch's inaction after a parliamentary committee called for tougher rules designed to prevent spyware abuse across the trading bloc. More than half of European Parliament lawmakers backed a resolution demanding rapid action.
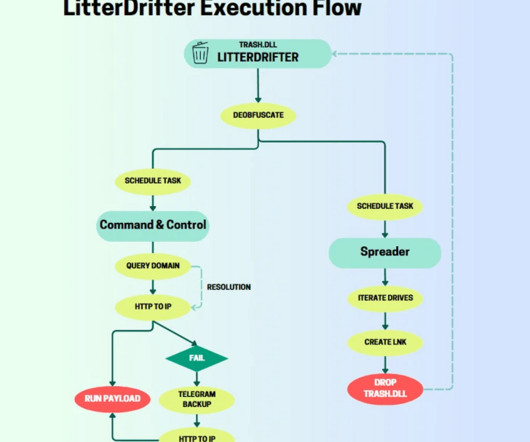
Security Affairs
NOVEMBER 18, 2023
Russia-linked cyberespionage group Gamaredon has been spotted propagating a worm called LitterDrifter via USB. Check Point researchers observed Russia-linked Gamaredon spreading the worm called LitterDrifter via USB in attacks against Ukraine. Gamaredon (aka Shuckworm, Actinium, Armageddon, Primitive Bear, UAC-0010, and Trident Ursa) has been active since 2014 and its activity focuses on Ukraine, the group was observed using the multistage backdoor Pteranodon / Pterodo.

KnowBe4
NOVEMBER 21, 2023
I recently wrote about how 1 in 34 organizations globally has experienced an attempted ransomware attack. But that statistic doesn’t provide enough context around the impact felt by the organizations that do business in one form or another with those that are attacked.
Let's personalize your content