3 Ways ChatGPT Will Change Infosec in 2023
Dark Reading
JANUARY 27, 2023
OpenAI's chatbot has the promise to revolutionize how security practitioners work.
Dark Reading
JANUARY 27, 2023
OpenAI's chatbot has the promise to revolutionize how security practitioners work.
Data Breach Today
JANUARY 6, 2023
Database Will Provide Intelligence of Use to Online Criminals, Expert Warns Expect the recently leaked database containing over 200 million Twitter records to be an ongoing resource for hackers, fraudsters and other criminals operating online, even though 98% of the email addresses it contains have appeared in prior breaches, experts warn.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Krebs on Security
JANUARY 9, 2023
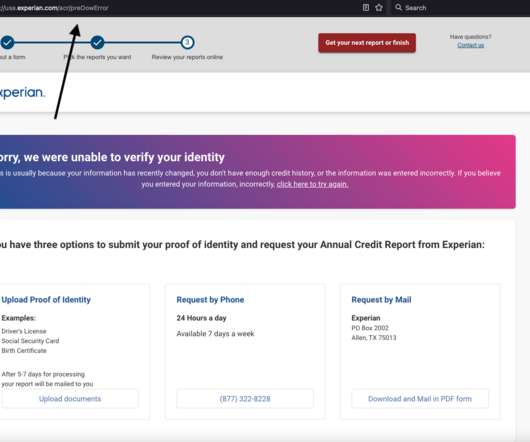
Identity thieves have been exploiting a glaring security weakness in the website of Experian , one of the big three consumer credit reporting bureaus. Normally, Experian requires that those seeking a copy of their credit report successfully answer several multiple choice questions about their financial history. But until the end of 2022, Experian’s website allowed anyone to bypass these questions and go straight to the consumer’s report.

The Last Watchdog
JANUARY 16, 2023
My name is Eden Zaraf. I’ve been driven by my passion for technology for as long as I can remember. Somewhere around the age of 13, I learned to code. I developed scripts, websites and got involved in security which led me to penetration testing. Related: Leveraging employees as detectors. Penetration Testing is a never-ending challenge. Five years ago, my friend Sahar Avitan began developing an automatic penetration testing tool for our own use.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Dark Reading
JANUARY 31, 2023
Everyone on Twitter wants a blue check mark. But Microsoft Azure's blue badges are even more valuable to a threat actor stealing your data via malicious OAuth apps.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.
Security Affairs
JANUARY 31, 2023
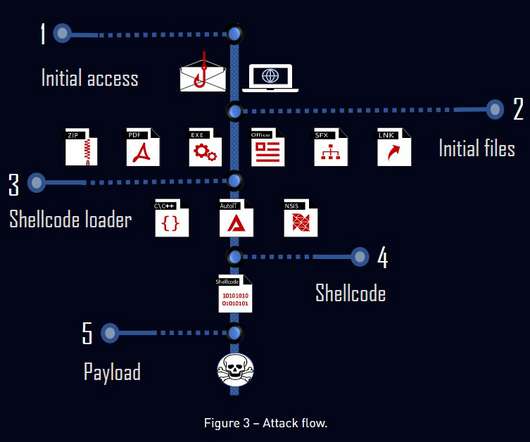
TrickGate is a shellcode-based packer offered as a service to malware authors to avoid detection, CheckPoint researchers reported. TrickGate is a shellcode-based packer offered as a service, which is used at least since July 2016, to hide malware from defense programs. A packer (aka “Crypter” and “FUD”) implements a series of functionalities to make it harder for antivirus programs to detect the malware.

Data Breach Today
JANUARY 12, 2023
Attack Is Disrupting International Mail Export Services The cyber incident at the Royal Mail that is impeding exports from the United Kingdom is reportedly a ransomware attack by the LockBit ransomware-as-a-service group. Britain's national postal service told customers Thursday not to post export items.

Krebs on Security
JANUARY 19, 2023
T-Mobile today disclosed a data breach affecting tens of millions of customer accounts, its second major data exposure in as many years. In a filing with federal regulators, T-Mobile said an investigation determined that someone abused its systems to harvest subscriber data tied to approximately 37 million current customer accounts. Image: customink.com In a filing today with the U.S.

The Last Watchdog
JANUARY 22, 2023
Small and medium-sized businesses are facing immense security challenges and these are the same as those of mid-size or larger enterprises. Related: Myths about safe browsing Clearly, SMBs need to be alert for cyberattacks, but they also need to stay focused on their business and not sacrifice productivity. Organizations are confronted with a severe security threats landscape, and it is critical that they have the ability to prevent, detect and respond to these threats in a timely manner.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m
KnowBe4
JANUARY 24, 2023
KnowBe4's latest reports on top-clicked phishing email subjects have been released for 2022 and Q4 2022. We analyze 'in the wild' attacks reported via our Phish Alert Button , top subjects globally clicked on in phishing tests , top attack vector types, and holiday email phishing subjects.

WIRED Threat Level
JANUARY 18, 2023
Animal rights activists have captured the first hidden-camera video from inside a carbon dioxide “stunning chamber” in a US meatpacking plant.

Security Affairs
JANUARY 31, 2023
Horizon3 security researchers released proof-of-concept (PoC) code for VMware vRealize Log Insight RCE vulnerability CVE-2022-31706. Last week, researchers from Horizon3’s Attack Team announced the release of PoC exploit code for remote code execution in VMware vRealize Log tracked as CVE-2022-31706 (CVSS base 9.8/10). The PoC exploit code will trigger a series of flaws in VMware vRealize Log to achieve remote code execution on vulnerable installs.

Data Breach Today
JANUARY 23, 2023
As Funding From Ransoms Goes Down, Gangs Embrace Re-Extortion, Researchers Warn Bad news for ransomware groups: Experts find it's getting tougher to earn a crypto-locking payday at the expense of others. The bad guys can blame a move by law enforcement to better support victims, and more organizations having robust defenses in place, which makes them tougher to take down.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.
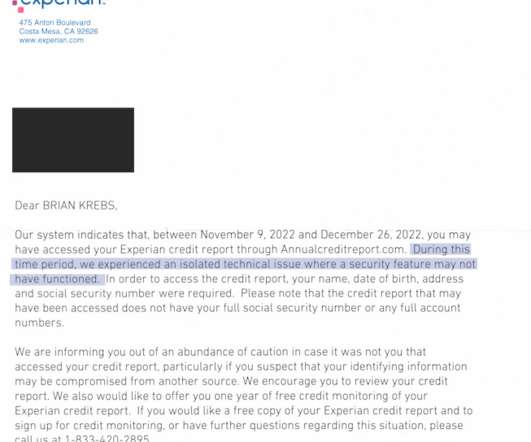
Krebs on Security
JANUARY 25, 2023
On Dec. 23, 2022, KrebsOnSecurity alerted big-three consumer credit reporting bureau Experian that identity thieves had worked out how to bypass its security and access any consumer’s full credit report — armed with nothing more than a person’s name, address, date of birth, and Social Security number. Experian fixed the glitch, but remained silent about the incident for a month.

The Last Watchdog
JANUARY 8, 2023
In golf there’s a popular saying: play the course, not your opponent. Related: How ‘CAASM’ closes gaps. In an enterprise, it’s the same rule. All areas of an organization need to be free to “play their own game.”. And when malware, ransomware, or other cyber threats get in the way, the focus shifts from forward progress to focused co-operation.

Schneier on Security
JANUARY 3, 2023
A group of Chinese researchers have just published a paper claiming that they can—although they have not yet done so—break 2048-bit RSA. This is something to take seriously. It might not be correct, but it’s not obviously wrong. We have long known from Shor’s algorithm that factoring with a quantum computer is easy. But it takes a big quantum computer, on the orders of millions of qbits, to factor anything resembling the key sizes we use today.

WIRED Threat Level
JANUARY 6, 2023
The January 6 Committee’s 841-page report will go down as one of the most important documents in US history. These key details stand out.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Security Affairs
JANUARY 31, 2023
The Pro-Russia group Killnet is launching a series of DDoS attacks against the websites of US healthcare organizations and hospitals. The Pro-Russia group Killnet launched a series of DDoS attacks against US healthcare organizations and hospitals. The group announced the attacks on its Telegram channel, calling for action against the US government healthcare.

Data Breach Today
JANUARY 2, 2023
Paying for Promises That Can't Be Audited Paints a Repeat-Attack Target on Victims Many ransomware-wielding attackers are expert at preying on their victims' compulsion to clean up the mess. Witness victims' continuing willingness to pay a ransom - separate to a decryptor - in return from a promise from extortionists that they will delete stolen data.

Krebs on Security
JANUARY 10, 2023
Microsoft today released updates to fix nearly 100 security flaws in its Windows operating systems and other software. Highlights from the first Patch Tuesday of 2023 include a zero-day vulnerability in Windows, printer software flaws reported by the U.S. National Security Agency , and a critical Microsoft SharePoint Server bug that allows a remote, unauthenticated attacker to make an anonymous connection.

The Last Watchdog
JANUARY 3, 2023
For the average user, the Internet is an increasingly dangerous place to navigate. Related: Third-party snooping is widespread. Consider that any given website experiences approximately 94 malicious attacks a day , and that an estimated 12.8 million websites are infected with malware. So, in response to these numbers, users are seeking ways to implement a more secure approach to web browsing.

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.

Schneier on Security
JANUARY 17, 2023
No details , though: According to the complaint against him, Al-Azhari allegedly visited a dark web site that hosts “unofficial propaganda and photographs related to ISIS” multiple times on May 14, 2019. In virtue of being a dark web site—that is, one hosted on the Tor anonymity network—it should have been difficult for the site owner’s or a third party to determine the real IP address of any of the site’s visitors.

WIRED Threat Level
JANUARY 10, 2023
More than 120 models of Siemens' S7-1500 PLCs contain a serious vulnerability—and no fix is on the way.

Security Affairs
JANUARY 31, 2023
IT Army of Ukraine claims to have breached the infrastructure of the Russian energy giant Gazprom and had access to a 1.5 GB archive. The collective IT Army of Ukraine announced it has gained access to a 1.5 GB archive belonging to the Russian energy giant Gazprom. The group of hacktivists announced the hack on their Telegram channel claiming that the archive contains more than 6,000 files of the companies of the Gazprom group.
Data Breach Today
JANUARY 13, 2023
Bug Exploited Symbolic Links to Find a File Path to Sensitive Data A high-severity vulnerability patched by Google Chrome a few months ago allowed hackers to steal sensitive files such as crypto wallets. Hackers increasingly are targeting individuals and organizations that hold cryptocurrencies, writes Imperva security researcher Ron Masas, who discovered the flaw.

Advertisement
Large enterprises face unique challenges in optimizing their Business Intelligence (BI) output due to the sheer scale and complexity of their operations. Unlike smaller organizations, where basic BI features and simple dashboards might suffice, enterprises must manage vast amounts of data from diverse sources. What are the top modern BI use cases for enterprise businesses to help you get a leg up on the competition?
Krebs on Security
JANUARY 17, 2023
Most people who operate DDoS-for-hire businesses attempt to hide their true identities and location. Proprietors of these so-called “booter” or “stresser” services — designed to knock websites and users offline — have long operated in a legally murky area of cybercrime law. But until recently, their biggest concern wasn’t avoiding capture or shutdown by the feds: It was minimizing harassment from unhappy customers or victims, and insulating themselves ag

The Last Watchdog
JANUARY 17, 2023
To get network protection where it needs to be, legacy cybersecurity vendors have begun reconstituting traditional security toolsets. The overarching goal is to try to derive a superset of very dynamic, much more tightly integrated security platforms that we’ll very much need, going forward. Related: The rise of security platforms. This development has gained quite a bit of steam over the past couple of years with established vendors of vulnerability management (VM,) endpoint detection and respo
eSecurity Planet
JANUARY 20, 2023
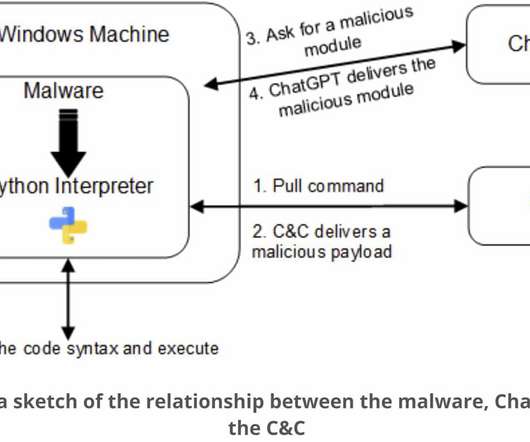
CyberArk researchers are warning that OpenAI’s popular new AI tool ChatGPT can be used to create polymorphic malware. “[ChatGPT]’s impressive features offer fast and intuitive code examples, which are incredibly beneficial for anyone in the software business,” CyberArk researchers Eran Shimony and Omer Tsarfati wrote this week in a blog post that was itself apparently written by AI. “However, we find that its ability to write sophisticated malware that holds no mali
Let's personalize your content