LastPass Data Breach: It's Time to Ditch This Password Manager
WIRED Threat Level
DECEMBER 28, 2022
The password manager's most recent data breach is so concerning, users need to take immediate steps to protect themselves.
WIRED Threat Level
DECEMBER 28, 2022
The password manager's most recent data breach is so concerning, users need to take immediate steps to protect themselves.

Dark Reading
DECEMBER 29, 2022
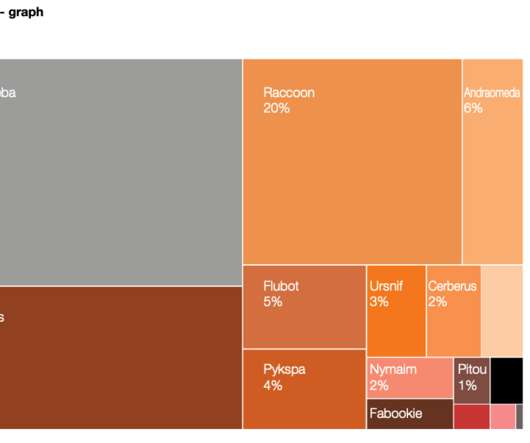
Attackers are harvesting credentials from compromised systems. Here's how some commonly used tools can enable this.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Krebs on Security
DECEMBER 19, 2022
Photo: BrandonKleinPhoto / Shutterstock.com. Two U.S. men have been charged with hacking into the Ring home security cameras of a dozen random people and then “swatting” them — falsely reporting a violent incident at the target’s address to trick local police into responding with force. Prosecutors say the duo used the compromised Ring devices to stream live video footage on social media of police raiding their targets’ homes, and to taunt authorities when they arri
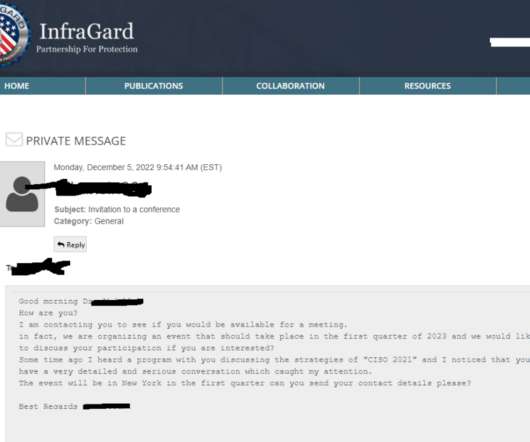
Krebs on Security
DECEMBER 13, 2022
InfraGard , a program run by the U.S. Federal Bureau of Investigation (FBI) to build cyber and physical threat information sharing partnerships with the private sector, this week saw its database of contact information on more than 80,000 members go up for sale on an English-language cybercrime forum. Meanwhile, the hackers responsible are communicating directly with members through the InfraGard portal online — using a new account under the assumed identity of a financial industry CEO tha

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Data Breach Today
DECEMBER 19, 2022
Move Infrastructure to the Cloud and Hone Incident Response Plans, Experts Say To avoid having to even consider paying a ransom, experts have long urged all organizations to put in place appropriate defenses. Two defensive strategies for healthcare firms are moving backup and recovery to the cloud and practicing incident response scenarios.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

WIRED Threat Level
DECEMBER 12, 2022
A confluence of factors is leading people in the nation to gravitate toward extremist views.

The Last Watchdog
DECEMBER 14, 2022
There is much that can be gleaned from helping companies identify and manage their critical vulnerabilities 24X7. Related: The case for proactive pentests. Based on insights from our team of elite security researchers here at Bugcrowd, these are three trends gaining steam as 2022 comes to a close – trends that I expect to command much attention in 2023.

Schneier on Security
DECEMBER 30, 2022
Yet another smartphone side-channel attack: “ EarSpy: Spying Caller Speech and Identity through Tiny Vibrations of Smartphone Ear Speakers “: Abstract: Eavesdropping from the user’s smartphone is a well-known threat to the user’s safety and privacy. Existing studies show that loudspeaker reverberation can inject speech into motion sensor readings, leading to speech eavesdropping.
Krebs on Security
DECEMBER 14, 2022
The U.S. Department of Justice (DOJ) today seized four-dozen domains that sold “booter” or “stresser” services — businesses that make it easy and cheap for even non-technical users to launch powerful Distributed Denial of Service (DDoS) attacks designed knock targets offline. The DOJ also charged six U.S. men with computer crimes related to their alleged ownership of the popular DDoS-for-hire services.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Data Breach Today
DECEMBER 13, 2022
Victims Still Learning Their Personal Data Was Illegally Accessed, Copied in 2021 A ransomware attack on the Irish healthcare system in 2021 has cost the government 80 million euros in damages and counting. The Irish Health Service continues to notify victims of the incident that their personal information was illegally accessed and copied.
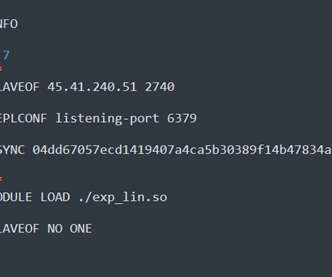
Security Affairs
DECEMBER 1, 2022
Redigo is a new Go-based malware employed in attacks against Redis servers affected by the CVE-2022-0543 vulnerability. Researchers from security firm AquaSec discovered a new Go-based malware that is used in a campaign targeting Redis servers. Threat actors are exploiting a critical vulnerability, tracked as CVE-2022-0543 , in Redis (Remote Dictionary Server) servers.

WIRED Threat Level
DECEMBER 9, 2022
Are you thinking about uploading some selfies and buying a pack of ‘Magic Avatars’? Consider these expert tips first.

The Last Watchdog
DECEMBER 13, 2022
It’s all too easy to take for granted the amazing digital services we have at our fingertips today. Related: Will Matter 1.0 ignite the ‘Internet of Everything’ Yet, as 2022 ends, trust in digital services is a tenuous thing. A recent survey highlights the fact that company leaders now understand that digital trust isn’t nearly what it needs to be.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

eSecurity Planet
DECEMBER 15, 2022
Released on November 30, ChatGPT has instantly become a viral online sensation. In a week, the app gained more than one million users. Unlike most other AI research projects, ChatGPT has captivated the interest of ordinary people who do not have PhDs in data science. They can type in queries and get human-like responses. The answers are often succinct.
Krebs on Security
DECEMBER 8, 2022
Ransomware groups are constantly devising new methods for infecting victims and convincing them to pay up, but a couple of strategies tested recently seem especially devious. The first centers on targeting healthcare organizations that offer consultations over the Internet and sending them booby-trapped medical records for the “patient.” The other involves carefully editing email inboxes of public company executives to make it appear that some were involved in insider trading.

Data Breach Today
DECEMBER 20, 2022
Breach Is Latest in Long List of Complex Vendor Incidents An Oklahoma-based provider of administrative and technology services to healthcare organizations is notifying more than 271,000 individuals that their personal information may have been compromised in a hacking incident involving a third-party data storage vendor.
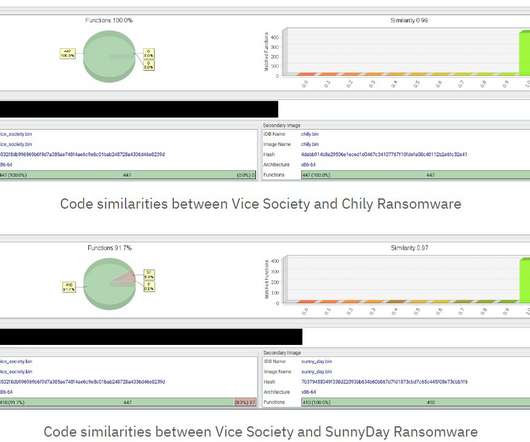
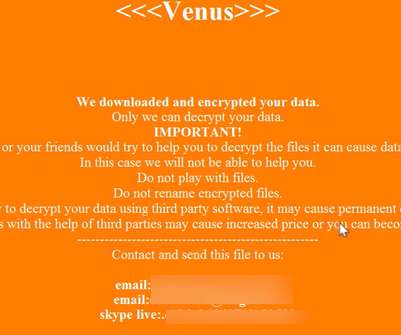
Security Affairs
DECEMBER 22, 2022
The Vice Society ransomware group has adopted new custom ransomware, with a strong encryption scheme, in recent intrusions. SentinelOne researchers discovered that the Vice Society ransomware gang has started using a custom ransomware that implements a robust encryption scheme, using NTRUEncrypt and ChaCha20-Poly1305 algorithms. Vice Society ransomware has been active since June 2021, it is considered by researchers a spin-off of the HelloKitty ransomware , the malware targets both Windows and L

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

WIRED Threat Level
DECEMBER 10, 2022
Plus: Chinese hackers stealing US Covid relief funds, a cyberattack on the Met Opera website, and more.

The Last Watchdog
DECEMBER 6, 2022
Much more effective authentication is needed to help protect our digital environment – and make user sessions smoother and much more secure. Related: Why FIDO champions passwordless systems. Consider that some 80 percent of hacking-related breaches occur because of weak or reused passwords, and that over 90 percent of consumers continue to re-use their intrinsically weak passwords.

eSecurity Planet
DECEMBER 7, 2022
It has certainly been a rough year for the tech industry. There have been many layoffs, the IPO market has gone mostly dark, and venture funding has decelerated. Despite all this, there is one tech category that has held up fairly well: Cybersecurity. Just look at a report from M&A advisory firm Houlihan Lokey , which found that private cybersecurity company funding grew by 9.4% to $26.9 billion between September 2021 and September 2022.
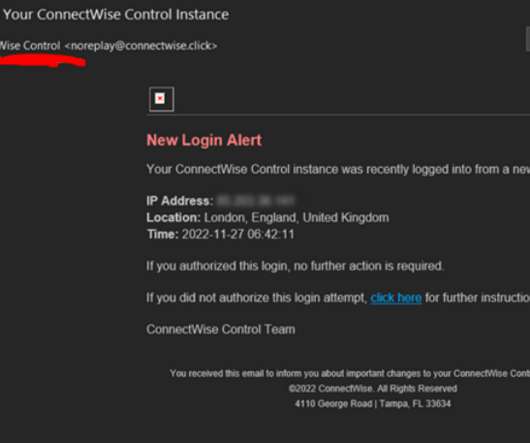
Krebs on Security
DECEMBER 1, 2022
ConnectWise , which offers a self-hosted, remote desktop software application that is widely used by Managed Service Providers (MSPs), is warning about an unusually sophisticated phishing attack that can let attackers take remote control over user systems when recipients click the included link. The warning comes just weeks after the company quietly patched a vulnerability that makes it easier for phishers to launch these attacks.

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.

Data Breach Today
DECEMBER 2, 2022
Some Customers at Risk of Identity Theft, South Staffordshire Water Belatedly Warns Is a four-month delay between learning your systems were breached and notifying affected customers acceptable? After spotting an attack in August, private utility South Staffordshire Water in England is only beginning to alert customers that they're at risk of identity theft.
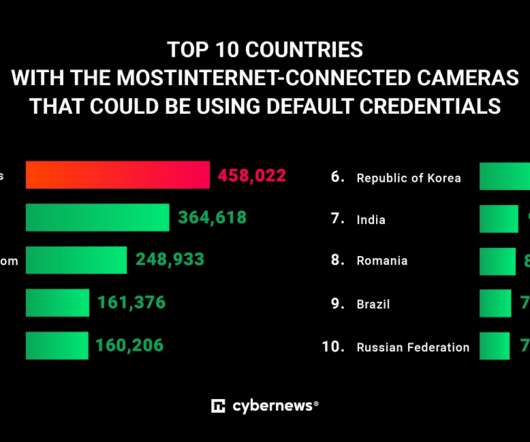
Security Affairs
DECEMBER 14, 2022
The number of internet-facing cameras in the world is growing exponentially. Some of the most popular brands don’t enforce a strong password policy, meaning anyone can peer into their owners’ lives. Original post at [link]. When you spy on your neighborhood or your cafe customers, do you wonder if someone is watching Big Brother – you, in this case?

WIRED Threat Level
DECEMBER 15, 2022
Navigation system monitors have seen a recent uptick in interruptions since Ukraine began launching long-range drone attacks.

The Last Watchdog
DECEMBER 8, 2022
Over the years, bad actors have started getting more creative with their methods of attack – from pretending to be a family member or co-worker to offering fortunes and free cruises. Related: Deploying employees as human sensors. Recent research from our team revealed that while consumers are being exposed to these kinds of attacks (31 percent of respondents reported they received these types of messages multiple times a day), they continue to disregard cyber safety guidelines.

Advertisement
Large enterprises face unique challenges in optimizing their Business Intelligence (BI) output due to the sheer scale and complexity of their operations. Unlike smaller organizations, where basic BI features and simple dashboards might suffice, enterprises must manage vast amounts of data from diverse sources. What are the top modern BI use cases for enterprise businesses to help you get a leg up on the competition?

eSecurity Planet
DECEMBER 8, 2022
SafeBreach Labs researcher Or Yair has uncovered zero-day vulnerabilities in several leading endpoint detection and response ( EDR ) and antivirus ( AV ) solutions that enabled him to turn the tools into potentially devastating next-generation wipers. “This wiper runs with the permissions of an unprivileged user yet has the ability to wipe almost any file on a system, including system files, and make a computer completely unbootable,” Yair warned in a blog post detailing the findings
Krebs on Security
DECEMBER 5, 2022
In December 2021, Google filed a civil lawsuit against two Russian men thought to be responsible for operating Glupteba , one of the Internet’s largest and oldest botnets. The defendants, who initially pursued a strategy of counter suing Google for interfering in their sprawling cybercrime business, later brazenly offered to dismantle the botnet in exchange for payment from Google.

Data Breach Today
DECEMBER 8, 2022
Indian Firm Accuses 'Notorious Cyber Security Company' in Ongoing Incident Indian cybersecurity firm CloudSEK says another cybersecurity firm used a compromised collaboration platform credential to obtain access to its training webpages. CEO Rahul Sasi did not identify the alleged perpetrator and says the hacker did not obtain access to the company code base and database.
Let's personalize your content