Expert: Keep Calm, Avoid Overhyping China's AI Capabilities
Data Breach Today
SEPTEMBER 19, 2023
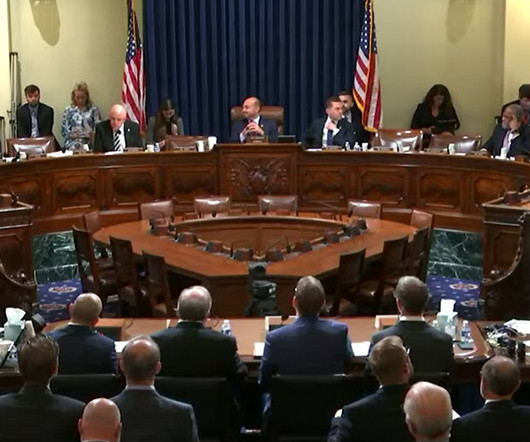
China's Ability to Diffuse AI Across Economy Lags Ability to Make Big Breakthroughs A researcher advised lawmakers to "keep calm and avoid overhyping China's AI capabilities" since the authoritarian regime struggles to drive widespread adoption of new technology. He urged Congress to embrace an "open system of innovation" around AI even it that results in some IP leaking to China.








































Let's personalize your content