I spent hours testing ChatGPT Tasks - and its refusal to follow directions was mildly terrifying
Collaboration 2.0
JANUARY 17, 2025
ChatGPT tasks offers AI prompt scheduling and automation, but what happens when things go wrong?

Collaboration 2.0
JANUARY 17, 2025
ChatGPT tasks offers AI prompt scheduling and automation, but what happens when things go wrong?

Security Affairs
JANUARY 17, 2025
noyb files complaints against TikTok, AliExpress, and other Chinese companies for illegal EU user data transfers to China, violating data protection laws. Austrian privacy non-profit group None of Your Business (noyb) has filed complaints accusing companies like TikTok, AliExpress, SHEIN, Temu, WeChat, and Xiaomi of violating data protection regulations in the European Union by unlawfully transferring users’ data to China. noyb filed GDPR complaints against the above companies for unlawful
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Collaboration 2.0
JANUARY 17, 2025
If you're wondering which apps take priority on your new Linux machine, these 10 will help you get the most out of the OS.
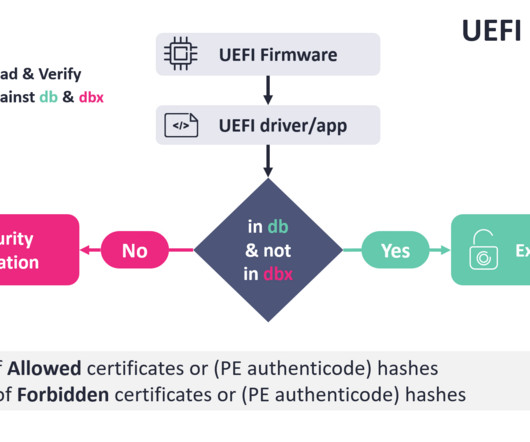
Security Affairs
JANUARY 17, 2025
Researchers detailed a now-patched vulnerability that could allow a bypass of the Secure Boot mechanism in UEFI systems. ESET disclosed details of a now-patched vulnerability, tracked as CVE-2024-7344 (CVSS score: 6.7), that could allow a bypass of the Secure Boot mechanism in UEFI systems. The Unified Extensible Firmware Interface (UEFI) is a specification that defines a software interface between an operating system and platform firmware.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Collaboration 2.0
JANUARY 17, 2025
If you have an aging computer and want to repurpose it, these lightweight Linux distributions will serve you for years to come.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Collaboration 2.0
JANUARY 17, 2025
The OnePlus 13R undercuts the competition by hundreds of dollars, leveraging the same winning formula from the OnePlus 12R to help it stand out.

Data Breach Today
JANUARY 17, 2025
Department of Treasury Imposes Sanctions The U.S. federal government said Friday it's traced the source of Chinese hacker intrusions into telecom networks to a government contractor located in hacking hotbed Sichuan. The Department of Treasury imposed sanctions on the firm, Sichuan Juxinhe Network Technology.

Collaboration 2.0
JANUARY 17, 2025
The Asus RT-BE86U is loaded with security tools, letting you enjoy the next generation of high-speed internet safely.
WIRED Threat Level
JANUARY 17, 2025
As the US faces the worst telecommunications hack in our nations history, by Chinas Salt Typhoon hackers, the outgoing FCC chair is determined to bolster network security if its the last thing she does.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Collaboration 2.0
JANUARY 17, 2025
The OnePlus 13R undercuts the competition by hundreds of dollars while offering a display and performance package that's easy to appreciate.

Data Breach Today
JANUARY 17, 2025
Also: Bringing AML and Fraud Programs Together; the Global AI Arms Race In this week's update, ISMG editors discussed a U.K. proposal to mandate ransomware payment reporting, tackling financial crime by bringing together fraud and AML teams, and the global AI arms race as countries compete to lead innovation while balancing regulation and ethics.
Collaboration 2.0
JANUARY 17, 2025
The expansion of Samsung's device protection program means you won't pay anything (extra) to fix a cracked screen.

Data Breach Today
JANUARY 17, 2025
Enzo Biochem Previously Paid Three States $4.5M in Fines for Same Breach Biotech firm Enzo Biochem has agreed to pay $7.5 million to settle a consolidated proposed class action lawsuit involving a 2023 ransomware attack affecting 2.5 million people. The company has already paid $4.5 million in fines to three state attorneys general for the same incident.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

Collaboration 2.0
JANUARY 17, 2025
There may even be AI 'layoffs' as programs are replaced by more highly capable versions.

Data Breach Today
JANUARY 17, 2025
Actively Targeted Zero-Day Patched; Warning Issued After Device Configurations Leak Fortinet has released patches to fix a zero-day vulnerability being actively exploited by attackers. Separately, researchers are warning customers to review their infrastructure after attackers leaked configuration details - including firewall rules and plaintext VPN passwords - for 15,000 devices.

Collaboration 2.0
JANUARY 17, 2025
Your staff will take matters into their own hands if you don't take a tight grip on generative AI. Here's how to wrestle back control.

Data Breach Today
JANUARY 17, 2025
Google Says Platforms Shouldn't Use Emails as Unique Identifiers A security researcher purchased abandoned online domains belonging to failed startups and found he could recreate email addresses and access third party services containing sensitive information collected by the shuttered companies by signing onto the platforms using "Sign in with Google.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

Collaboration 2.0
JANUARY 17, 2025
Grab a 4-pack of Apple AirTags for $29 off right now at Amazon so you can help the iPhone user in your life monitor their keys, wallet, luggage, and more.

KnowBe4
JANUARY 17, 2025
Ransomware groups claimed responsibility for 5,461 attacks in 2024, with 1,204 of these attacks being publicly confirmed by victim organizations, according to Comparitechs latest Ransomware Roundup report.

Collaboration 2.0
JANUARY 17, 2025
The Galaxy S25 series is expected at the event, but we may also get surprise appearances on the wearables side.
KnowBe4
JANUARY 17, 2025
I have helped people detect romance scams for decades. It is still very common for romance scammers to leverage both pictures of celebrities and pictures of innocent, everyday people as part of these scams.

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.

Collaboration 2.0
JANUARY 17, 2025
As big brands chase the latest AI trends, they're losing touch with their audience - making this the perfect time for you to join a movement that's reshaping e-commerce. Here's how.
KnowBe4
JANUARY 17, 2025
Social engineering and phishing are involved in 70% - 90% of data breaches. No other root cause of malicious hacking (e.g., unpatched software and firmware, eavesdropping, cryptography attacks, physical theft, etc.) comes close.

Collaboration 2.0
JANUARY 17, 2025
Running ethernet wiring can be messy and expensive. If you have cable outlets, you can use a Trendnet Ethernet over Coax adapter to set up a high-speed wired connection with minimal effort.

KnowBe4
JANUARY 17, 2025
Check out the December updates in Compliance Plus so you can stay on top of featured compliance training content.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Collaboration 2.0
JANUARY 17, 2025
The Nuwa Pen incorporates three tiny cameras to transcribe what you write (on paper!) to the app, acting as a digital solution for those who prefer using a pen and notebook.

Data Protection Report
JANUARY 17, 2025
On 24 December 2024, Malaysias Minister of Digital stipulated the dates on which the provisions of the Malaysian Personal Data Protection (Amendment) Act 2024 ( Amendment Act ) will come into force. The Amendment Act will take effect in three tranches, which we summarise and discuss below with thanks to Malaysian law firm Skrine. This development marks the first stage in implementing the changes to Malaysias data protection landscape brought about by the watershed revisions to Malaysias Personal

Collaboration 2.0
JANUARY 17, 2025
Most people never touch their TV's default settings. But if you have one from Samsung, try these modifications to improve its visual output.
Let's personalize your content