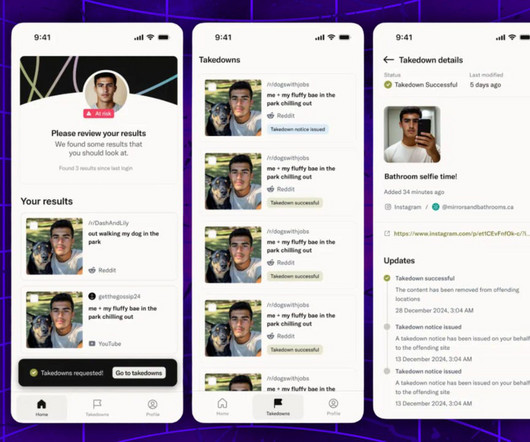
Deepfake detection service Loti AI expands access to all users - for free
Collaboration 2.0
MARCH 21, 2025
Once exclusive to celebrities, this company claims it can automatically remove any unapproved likeness within 17 hours.
Collaboration 2.0
MARCH 21, 2025
Once exclusive to celebrities, this company claims it can automatically remove any unapproved likeness within 17 hours.

Data Breach Today
MARCH 21, 2025
What Do You Mean, Hospital-Targeting Sociopath Ransomware Wielders Continue to Lie? A ransomware group reusing the Babuk ransomware brand claims to have stolen data from the likes of Amazon, Delta and US Bank. Just one problem: Security experts found a startling overlap between its claimed victims and previous attacks scored by the likes of Clop, LockBit and RansomHub.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Collaboration 2.0
MARCH 21, 2025
It was the shot heard 'round the world - a neural network that finally fulfilled decades of theoretical promise.

Data Breach Today
MARCH 21, 2025
'Wave of Ransomware Attacks' Hitting FortiOS and FortiProxy Devices, Warn Experts Cyber defenders said they're seeing a "wave of ransomware attacks" unleashed by attackers who gain initial access by targeting two known vulnerabilities in Fortinet FortiOS and FortiProxy devices. Hackers sometimes patch the devices to hide their persistent remote access.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Collaboration 2.0
MARCH 21, 2025
The new Mac Studio delivers impressive performance courtesy of its M4 Max chip. This hardware and its space-saving design make the desktop a must-have for professionals and creatives.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Collaboration 2.0
MARCH 21, 2025
The latest version patches a critical security flaw that could allow a web page to run malicious code in the browser.

Data Breach Today
MARCH 21, 2025
UAT-5918 Breaches Taiwan's Critical Sectors Using N-Day Flaws for Cyberespionage Hackers with ties to China-based hacking groups including Volt Typhoon are breaching Taiwan's critical infrastructure by exploiting unpatched web and application servers as entry points for a cyberespionage campaign. Cisco Talos threat hunters identified the new threat actor as UAT-5918.

Collaboration 2.0
MARCH 21, 2025
The budget-friendly RingConn Gen 2 delivers features and health data that competes with the big dogs.

Data Breach Today
MARCH 21, 2025
Dave DeWalt's NightDragon and HSBC to Back New Product Rollouts and Global Growth Dataminr received $85 million in convertible pre-IPO funding from Dave DeWalts NightDragon and HSBC. The investment will support the rollout of context agents and pre-generative AI capabilities, and enable the company to scale internationally ahead of its planned initial public offering.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Collaboration 2.0
MARCH 21, 2025
It was the shot heard 'round the world - a neural network that finally fulfilled decades of theoretical promise.

Data Breach Today
MARCH 21, 2025
Google Aims to Match Microsoft Defender With $32B Buy of Wiz's Cloud Security Tech Google's plan to buy cloud security firm Wiz for $32 billion highlights its drive to compete with Microsoft Defender and expand multi-cloud protection, and will put pressure on AWS to respond. Forrester Analyst Andras Cser says Wiz will likely remain independent for now, easing integration hurdles.

Collaboration 2.0
MARCH 21, 2025
The Suunto Aqua Light lives up to its name as a lightweight open-ear headset that are comfortable enough to go unnoticed during your workout.

Data Breach Today
MARCH 21, 2025
Open Power AI Consortium Members Include Nvidia and Microsoft Tech giants and utility providers on Thursday formed an alliance to harness artificial intelligence for a more resilient power grid. More than two dozen organizations are participating in the Open Power AI Consortium led by the Electric Power Research Institute.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

Collaboration 2.0
MARCH 21, 2025
Garmin's Forerunner 255S is a reliable, long-lasting smartwatch that suggests workouts and offers morning reports on your sleep. Multiple models are currently on sale.

Data Breach Today
MARCH 21, 2025
Researcher Found Unsecured Database Server Containing 1,864 GB of OrthoMinds' Data An orthodontic practice software vendor is notifying an undisclosed number of patients that their data was exposed to the internet for 10 days last November. The security researcher who discovered the data leak said the incident appears to have lasted longer and affected more than 200,000 patients.

Collaboration 2.0
MARCH 21, 2025
After Windows defenses improved, the attackers switched to targeting Mac and Safari users with these very effective scams.

Data Breach Today
MARCH 21, 2025
Judge Orders DOGE Staffers to Delete Social Security Data in Scathing Order A federal judge has issued a temporary restraining order restricting Department of Government Efficiency employees from accessing data containing personally identifiable information at the Social Security Administration. DOGE "essentially engaged in a fishing expedition," the judge wrote.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.
Collaboration 2.0
MARCH 21, 2025
The fake listings were part of a scam that used the old bait-and-switch tactic to prey on people - and there may be more lurking out there.

KnowBe4
MARCH 21, 2025
Bitdefender warns that a major ad fraud campaign in the Google Play Store resulted in more than 60 million downloads of malicious apps.

Collaboration 2.0
MARCH 21, 2025
The new Mac Studio delivers impressive performance courtesy of its M4 Max chip. This hardware and its space-saving design make the desktop a must-have for professionals and creatives.

Schneier on Security
MARCH 21, 2025
The UK’s National Computer Security Center (part of GCHQ) released a timeline —also see their blog post —for migration to quantum-computer-resistant cryptography. It even made The Guardian.

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.

Collaboration 2.0
MARCH 21, 2025
A few quick tweaks and troubleshooting steps can help you eliminate judder and reduce lag on your smart TV. Here's how to get a smoother picture.

KnowBe4
MARCH 21, 2025
In todays world, cybersecurity is more critical than ever. Organizations and individuals alike face a constant barrage of cyber threats, and often, the weakest link in our defenses is something as simple as a password.

Collaboration 2.0
MARCH 21, 2025
Configuring a VPN for your entire home can be a hassle. I tested one of the leading options, Privacy Hero 2. Here's what I found.

Jamf
MARCH 21, 2025
Employee satisfaction, productivity gains and maximized ROIdrive Mac adoption in enterprises. Learnhow emerging cybersecurity trends highlightAI-driven threats, compliance risksand the need for security parity across platforms through Zero Trust leadstrategic decision-making for IT leaders.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Collaboration 2.0
MARCH 21, 2025
The Amazon Echo Frames (3rd Gen) may be the most subtle-looking pair of smart glasses on the market, and they're $90 off now.

Security Affairs
MARCH 21, 2025
Russian zero-day broker Operation Zero is looking for exploits for the popular messaging app Telegram, offering up to $4 million for them. Operation Zero, a Russian zero-day broker, is offering up to $4 million for Telegram exploits, the news was first reported by Tech Crunch. The Russian firm seeks up to $500K for one-click RCE, $1.5M for zero-click RCE, and $4M for a full-chain exploit that could allow full device compromise.

Collaboration 2.0
MARCH 21, 2025
Atlas has breakdance moves too. See for yourself.
Let's personalize your content