You have 2 days to update Firefox before everything breaks
Collaboration 2.0
MARCH 19, 2025
Don't find out the hard way that this upgrade isn't optional.

Collaboration 2.0
MARCH 19, 2025
Don't find out the hard way that this upgrade isn't optional.

Data Breach Today
MARCH 19, 2025
Cyber Agency Urges Critical Infrastructure Operators to Migrate Within the Deadline The British cybersecurity agency urged critical infrastructure operators to adopt to post-quantum cryptography by 2035 as it and other government agencies prepare for the inevitability of quantum computers capable of breaking current encryption algorithms.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Collaboration 2.0
MARCH 19, 2025
Here's why I no longer have to keep my phone on silent mode to protect my peace.

Data Breach Today
MARCH 19, 2025
Why Are Facilities Caring for the Elderly 'Targets of Opportunity' For Cybercrime? More than a half dozen nursing homes and rehabilitation centers have reported an assortment of major hacks in the last month affecting a total of more than 130,000 individuals. What makes facilities caring for elderly and disabled patients an attractive and vulnerable target to cybercriminals?

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Collaboration 2.0
MARCH 19, 2025
Is your password on the list? If so - tsk, tsk.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.
Collaboration 2.0
MARCH 19, 2025
Engineering careers are evolving, and LinkedIn's latest Skills on the Rise report highlights the must-have skills for 2025. From AI development to people management, here's how to future-proof your career.

Data Breach Today
MARCH 19, 2025
Paste-and-Run Schemes Trick Users Into Running Attacker-Provided Malicious Code Social engineering tactics designed to trick users into installing malware, oftentimes by "fixing" a fake problem, are growing more common. Experts say a majority of these ClickFix - aka ClearFix or paste-and-run - attacks now lead to information-stealing malware infections.

Collaboration 2.0
MARCH 19, 2025
Consumers are turning to AI for shopping advice more and more. Here's what retailers need to know.

Data Breach Today
MARCH 19, 2025
Over 10K Exploit Attempts Recorded in a Week From a Single Malicious IP Hackers are exploiting a vulnerability in ChatGPT's infrastructure to redirect users to malicious websites, with security researchers recording more than 10,000 exploit attempts in a week from a single malicious IP address. The financial sector has borne the brunt of the attacks.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Collaboration 2.0
MARCH 19, 2025
A default installation of Windows 11 includes dozens of Microsoft apps. Which ones are worth keeping, and which ones should you uninstall? These are my top picks.

Data Breach Today
MARCH 19, 2025
Get the Most Out of Your Event by Planning, Networking and Following Up Conference season is upon us, and there's no better time to work on your career at one or more of the major cybersecurity conferences in the United States this spring and summer. These conferences do cost money, but with a bit of preparation, you can invest in your career.
Collaboration 2.0
MARCH 19, 2025
Tired of traditional social media? Here's why I've been turning to Substack more and more - and why you might do the same if you give it a try.

Data Breach Today
MARCH 19, 2025
Researchers Examined 7 LLMs to Determine How they Dealt with Flawed Code Large language models trained on flawed data tend to replicate those mistakes, researchers found. "In bug-prone tasks, the likelihood of LLMs generating correct code is nearly the same as generating buggy code," found researchers from institutions including the Chinese Academy of Sciences.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

Collaboration 2.0
MARCH 19, 2025
Need to keep track of collections of things for your home or business? Here's all you need to get started, add new items, and search for them.

Data Breach Today
MARCH 19, 2025
Google Boosts Native Cloud Security with Wiz, But Deal Raises Multi-Cloud Concerns Googles $32 billion deal to acquire Wiz boosts its cloud security capabilities, shifting away from third-party partnerships. Wizs market leadership and acquisitions make it a valuable asset, but concerns remain about its future neutrality in multi-cloud environments and AWS, Azure relationships.

Collaboration 2.0
MARCH 19, 2025
If you're looking for the best CRM software on the market, we have you covered. These options can help your team manage customer relationships, lead management, and more.

KnowBe4
MARCH 19, 2025
Business email compromise (BEC) attacks rose 13% last month, with the average requested wire transfer increasing to $39,315, according to a new report from Fortra.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

Collaboration 2.0
MARCH 19, 2025
If you're looking for a pair of headphones with sonic clarity and brilliant EQ, the Dali IO-8 will transport you to audio nirvana.

CILIP
MARCH 19, 2025
Severing Elsevier Will more universities follow Sheffield, Surrey and York out of big deals with Elsevier? The moment of truth for the sector will come in December 2025. THE decision by three universities not to extend their Jisc-negotiated transformative agreements (TA) with Elsevier was largely driven by the financial crisis in higher education, but many hope it will be a positive development.

Collaboration 2.0
MARCH 19, 2025
The smart ring is coming to the big box retailer starting on Wednesday.

Jamf
MARCH 19, 2025
Revolutionize campus communication with Kitcast, Apple TV, and Jamf. A scalable, cost-effective digital signage solution for real-time updates and easy management.

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.

Collaboration 2.0
MARCH 19, 2025
This repair set by Jakemy has everything you need to effortlessly repair computers, smartphones, tablets, eyeglasses, and more.

Security Affairs
MARCH 19, 2025
California Cryobank, the largest US sperm bank, suffered a data breach exposing customer information. California Cryobank (CCB) is the largest sperm bank in the U.S., providing frozen donor sperm and reproductive services, including egg and embryo storage. It operates in all 50 states and over 30 countries worldwide, helping individuals and couples with fertility treatments.

Collaboration 2.0
MARCH 19, 2025
Kids can now tap-to-pay using their Android phone - with a parent's approval.
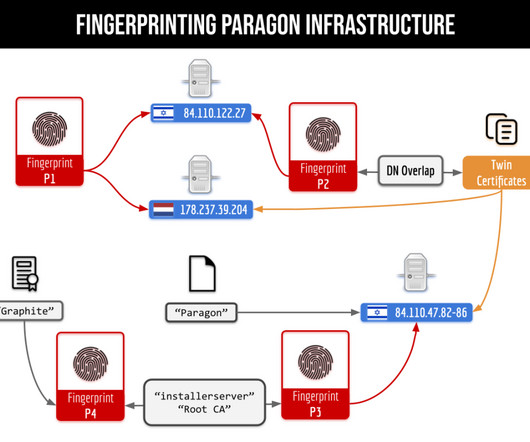
Security Affairs
MARCH 19, 2025
WhatsApp fixed a zero-click, zero-day vulnerability used to install Paragon’s Graphite spyware on the devices of targeted individuals. WhatsApp has addressed a zero-click, zero-day vulnerability exploited to install Paragon’s Graphite spyware on the devices of targeted individuals. WhatsApp blocked a spyware campaign by Paragon targeting journalists and civil society members after reports of the Citizen Lab group from the University of Toronto.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Collaboration 2.0
MARCH 19, 2025
How do you tell the difference between trustworthy open-source developers and hackers? Here's one idea.
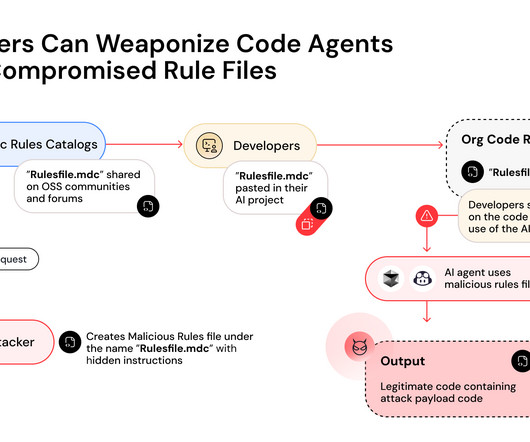
Security Affairs
MARCH 19, 2025
The Rules File Backdoor attack targets AI code editors like GitHub Copilot and Cursor, making them inject malicious code via a supply chain vulnerability. Pillar Security researchers uncovered a dangerous new supply chain attack vector called ‘ Rules File Backdoor.’ Threat actors could use the technique to silently compromise AI-generated code by injecting malicious code.

Collaboration 2.0
MARCH 19, 2025
The mid-range model features a fresh design and several upgrades that are hidden in plain sight.
Let's personalize your content