Udderly Insecure: Researchers Spot Cow-Tracking Collar Flaws
Data Breach Today
NOVEMBER 27, 2023
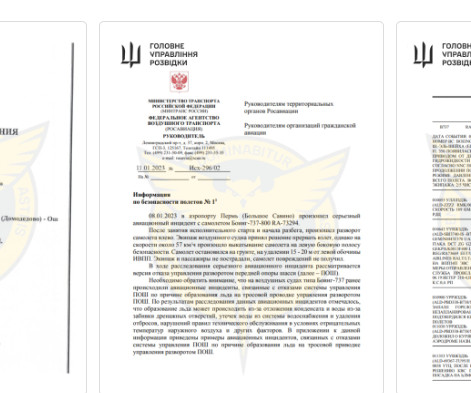
IoT Hackers Could Inject Data to Fool 'Smart' Farmers and Vets About Animal Welfare Not even dairy cows appear to be safe from internet of things flaws, researchers report after reverse-engineering health-monitoring collars for cows and finding they could eavesdrop on and alter data. Once addressed by the manufacturer, they said the non-updateable collars would have to be replaced.




































Let's personalize your content