Your Android phone just got a huge audio upgrade for free - including Google and Samsung
Collaboration 2.0
MARCH 17, 2025
Ever been at a crowded restaurant or bar and wanted to hear that one muted TV? Now you can with Auracast.

Collaboration 2.0
MARCH 17, 2025
Ever been at a crowded restaurant or bar and wanted to hear that one muted TV? Now you can with Auracast.
Data Breach Today
MARCH 17, 2025
Over 23,000 Code Repositories at Risk After Malicious Code Added to GitHub Actions Attackers subverted a widely used tool for software development environment GitHub, potentially allowing them to steal secrets from thousands of private code repositories as well as compromise other widely used "open source libraries, binaries and artifacts" that use the tool, experts warned.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Collaboration 2.0
MARCH 17, 2025
The developers of one of the coolest Linux distros just dropped a new version, and it makes the old one look boring.

Data Breach Today
MARCH 17, 2025
Ransomware Attack in 2023 Affected More Than 6 Million People Indian IT services giant Infosys said its U.S. subsidiary Infosys McCamish Systems agreed to pay $17.5 million to settle six class action lawsuits related to a cybersecurity incident that compromised the personal information of more than 6 million people.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Collaboration 2.0
MARCH 17, 2025
If you're finally ready to leave Chrome behind, these are my top recommendations and when to use them.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Collaboration 2.0
MARCH 17, 2025
You'll have to reinstall the AI or wait until Microsoft fixes the glitch.

Data Breach Today
MARCH 17, 2025
Regulators Say FIIG Lacked Basic Security Measures to Prevent 2023 Breach The Australian financial regulator has filed a lawsuit against FIIG Securities Limited, accusing the leading investment and financing company of having inadequate cybersecurity controls to stop a threat actor from stealing the confidential personal information of 18,000 customers.

Collaboration 2.0
MARCH 17, 2025
Sony's new RGB LED display features superior color accuracy and image detail. And TVs with this tech may arrive as soon as later this year.

Data Breach Today
MARCH 17, 2025
NetWitness is RSA's 4th Divestiture Since STG Purchased the Identity Giant in 2020 Clearlake Capital and Symphony Technology Group offloaded another RSA business unit, selling threat detection, investigation and response vendor NetWitness to PartnerOne. PartnerOne said it'll help NetWitness boost its technology, fuel its capabilities and solidify its position as a market leader.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Collaboration 2.0
MARCH 17, 2025
AI Companion has a bunch of new tricks up its sleeve.

Data Breach Today
MARCH 17, 2025
CPA Says Clients' Employee Benefit Plan Information Compromised in 2024 Incident A certified public accounting firm that provides services to labor unions, non-profits and other organizations for employee benefit plans is notifying nearly 217,000 people of a 2024 hack. The firm is already facing at least five proposed federal class action lawsuits related to the breach.

Collaboration 2.0
MARCH 17, 2025
Did you know you can install the most recent Linux kernel on some distributions? We'll show you how it's done on Ubuntu (and why you may or may not) want to do it.

Data Breach Today
MARCH 17, 2025
Carnegie Mellon CERT's Dan Costa on Addressing Root Causes of Insider Risk As layoffs and AI-driven workflows reshape workplace security, insider risk is becoming more complex. Dan Costa, technical manager for the CERT division at Carnegie Mellon University's Software Engineering Institute, outlines proactive strategies to manage insider risk effectively.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

Collaboration 2.0
MARCH 17, 2025
Here is exactly how to spot your big idea, validate it, and get started before everyone else.
CGI
MARCH 17, 2025
Artificial Intelligence (AI) is advancing at an unprecedented pace with breakthroughs and disruptions occurring almost weekly. From large language models to advanced automation systems with agentic AI, AI's impact is rapidly reshaping industries and redefining how businesses operate.

Collaboration 2.0
MARCH 17, 2025
They're called Experience Agents, and aim to provide personalized, empathetic responses in real time.
CGI
MARCH 17, 2025
Artificial Intelligence (AI) is advancing at an unprecedented pace with breakthroughs and disruptions occurring almost weekly. From large language models to advanced automation systems with agentic AI, AI's impact is rapidly reshaping industries and redefining how businesses operate.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

Collaboration 2.0
MARCH 17, 2025
Looking for a web browser that is as cool looking as it is secure and private? Take a look at this fork of Floorp.

Docuware
MARCH 17, 2025
Todays manufacturers are expected to be familiar with all new technology that promises to make their businesses more efficient. In the past, manufacturing companies put the focus of technology investments on improving production processes. Now, getting control of documents and data is just as important, especially when quality management is involved.

Collaboration 2.0
MARCH 17, 2025
Apple's flagship M4 laptop won't dazzle you with flashy features or a fresh design, but it's almost so polished that you can't complain.
Security Affairs
MARCH 17, 2025
Threat actors exploit Cascading Style Sheets (CSS) to bypass spam filters and detection engines, and track users actions and preferences. Cisco Talos observed threat actors abusing Cascading Style Sheets (CSS) to evade detection and track user behavior, raising security and privacy concerns, including potential fingerprinting. Cascading Style Sheets (CSS) is a stylesheet language used to control the appearance and layout of web pages.

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.

Collaboration 2.0
MARCH 17, 2025
Amazon's annual spring sale is likely coming soon, but now is the perfect time to grab Apple's budget-friendly desktop at an even lower price.
Security Affairs
MARCH 17, 2025
Threat actors began exploiting a recently disclosed Apache Tomcat vulnerability immediately after the release of a PoC exploit code. A newly disclosed Apache Tomcat vulnerability, tracked as CVE-2025-24813 , is being actively exploited just 30 hours after a public PoC was released. The issue is a path equivalence flaw in Apache Tomcat that allows remote code execution or information disclosure if specific conditions are met.

Collaboration 2.0
MARCH 17, 2025
Unlike Chrome, the Android version of Edge now offers its own dedicated store for extensions.
Security Affairs
MARCH 17, 2025
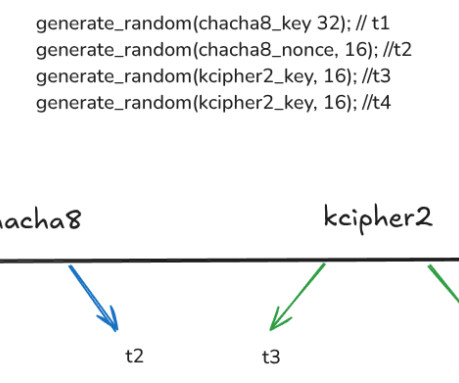
A researcher released a free decryptor for Linux Akira ransomware, using GPU power to recover keys through brute force. Security researcher Yohanes Nugroho created a free decryptor for Linux Akira ransomware , using GPUs to brute force the decryption keys. Initially estimating a week, the project took three weeks and cost $1,200 in GPU resources due to unexpected complexities.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Collaboration 2.0
MARCH 17, 2025
The added security is admirable, but the unexpected drawbacks aren't.

The Last Watchdog
MARCH 17, 2025
Frankfurt, Germany, Mar. 17, 2025, CyberNewswire — Cyberattacks are no longer an abstract threat – they dominate risk planning for companies worldwide. The latest Link11 European Cyber Report shows an alarming trend: the number of DDoS attacks has more than doubled, and they are shorter, more targeted, and more technically sophisticated.

Collaboration 2.0
MARCH 17, 2025
The Acer Aspire 14 AI is the latest addition to the affordable laptop line, with impressive battery life and solid hardware.
Let's personalize your content