Are we losing our critical thinking skills to AI? New Microsoft study raises red flags
Collaboration 2.0
FEBRUARY 13, 2025
As more workplaces embrace emerging technology, research warns that prolonged use of AI can erode our cognitive abilities.

Collaboration 2.0
FEBRUARY 13, 2025
As more workplaces embrace emerging technology, research warns that prolonged use of AI can erode our cognitive abilities.
WIRED Threat Level
FEBRUARY 13, 2025
Romance scams cost victims hundreds of millions of dollars a year. As people grow increasingly isolated, and generative AI helps scammers scale their crimes, the problem could get worse.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Collaboration 2.0
FEBRUARY 13, 2025
The differences between ChatGPT's Advanced Voice, Google's Gemini Live, and Microsoft's Copilot Voice are narrowing.

Data Breach Today
FEBRUARY 13, 2025
Astaroth Kit Offered for $2,000 on Telegram, Intercepts Authentication in Real Time A new phishing kit called Astaroth bypasses two-factor authentication through session hijacking and real-time credential interception from services like Gmail, Yahoo, AOL and Microsoft 365. Acting as a man-in-the-middle, it captures login credentials, tokens and session cookies in real time.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Collaboration 2.0
FEBRUARY 13, 2025
If your PC is operating perfectly right now, great! But getting ahead of any future PC fiascos with a recovery drive may save you from a major tech-induced headache later.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Collaboration 2.0
FEBRUARY 13, 2025
Samsung's Galaxy Watch FE is a great entry point into smartwatches, and the base model is available for $40 off.

Data Breach Today
FEBRUARY 13, 2025
Also: Google Fixes YouTube Vulnerabilities That Could Have Exposed User Emails This week: Microsoft, Ivanti and Google release fixes for critical vulnerabilities and urge priority patching; Lee Enterprises confirms a cyberattack disrupted newspaper operations; and thousands of KerioControl Firewalls exposed to critical remote code execution flaws.

Collaboration 2.0
FEBRUARY 13, 2025
If your PC can't upgrade to Windows 11, switching to Linux can extend its life past 2025. WattOS is one of the best options I've tested.

Data Breach Today
FEBRUARY 13, 2025
Social Platforms Also Could Face Stiff Fines for Failing to Protect Users The Australian government passed the Scams Prevention Framework law in Parliament to make social media companies, banks and telecommunication companies accountable for scammers using their networks, subjecting them to a maximum of AU$50 million in fines for violations.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Collaboration 2.0
FEBRUARY 13, 2025
SAP's new AI-driven data platform integrates SAP and non-SAP data, breaks silos, and enables next-gen automation with Joule AI agents. Is your business ready?

Data Breach Today
FEBRUARY 13, 2025
Acquisition of Startup Adds Modern Identity Governance to CyberArks Identity Suite CyberArk has acquired Zilla Security for up to $175 million, adding modern identity governance and administration capabilities with AI-driven automation for faster deployments, streamlined access reviews, and efficient provisioning to secure human and machine identities.
Collaboration 2.0
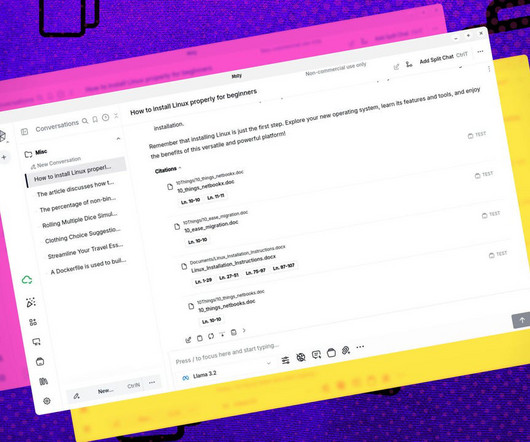
FEBRUARY 13, 2025
Msty is one of the best apps for interacting with the Ollama local AI tool and it contains a feature you'll want to use to help provide contextuality to its responses.

Data Breach Today
FEBRUARY 13, 2025
Could CISA's Uncertain Future Embolden Nation-State Attackers? As the future of the Cybersecurity and Infrastructure Security Agency becomes increasingly uncertain in the wake of a massive federal overhaul, experts warn that key U.S. infrastructure sectors, including energy, financial services and election infrastructure, are at a heightened risk of cyberattacks and cyberespionage.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

Collaboration 2.0
FEBRUARY 13, 2025
iPhones, iPads, MacBooks, and robots?

Data Breach Today
FEBRUARY 13, 2025
Russian, Iranian and Chinese APTs Among Most Active Ransomware Collaborators Security researchers are increasingly finding it challenging to attribute cyberattacks due to surging cooperation between nation-state hackers and ransomware groups, especially for espionage purposes. They say it reflects the blurring of the lines between state-directed and criminal activities.

Collaboration 2.0
FEBRUARY 13, 2025
Google's AI assistant now understands more languages and accents, making it easier to have a conversation.

Data Breach Today
FEBRUARY 13, 2025
Telecoms Still Falling to Chinese Nation-State Hacking Group, Researchers Warn A Chinese cyber espionage group tracked as Salt Typhoon and tied to the mass hacking of telecommunications networks in the U.S. and dozens of other countries has been continuing to seek and hack unpatched equipment, including exploiting two long-patched vulnerabilities in Cisco gear.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

Collaboration 2.0
FEBRUARY 13, 2025
Some detectors are better at spotting AI-written text than others. Here's why these mixed results matter.

AIIM
FEBRUARY 13, 2025
The evolution of information management demands a new approach to talent development. As someone who transitioned from traditional librarianship to leading digital transformation initiatives, I understand the importance of continuous learning and adaptation.

Collaboration 2.0
FEBRUARY 13, 2025
Ahead of the Oppo Find N5 launch early next week, OnePlus took to its community forums to announce that it will not launch a foldable this year.

KnowBe4
FEBRUARY 13, 2025
SentinelOne warns that a phishing campaign is targeting high-profile X accounts, including those belonging to US political figures, leading journalists, major technology companies, cryptocurrency organizations, and owners of coveted usernames.

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.

Collaboration 2.0
FEBRUARY 13, 2025
When a shopper clicks on a product available only on a brand's site, they'll be notified that they're about to leave Amazon. It looks like Google Shopping has some competition.

Jamf
FEBRUARY 13, 2025
Ensure compliance with regulatory frameworks using Jamfs Mac Endpoint Telemetry.

Collaboration 2.0
FEBRUARY 13, 2025
I noticed that my iPhone's battery was being hit hard after installing iOS 18. I tracked this down to a new feature.

Security Affairs
FEBRUARY 13, 2025
A November 2024 RA World ransomware attack on an Asian software firm used a tool linked to China-linked threat actors. Broadcom researchers reported that threat actors behind an RA World ransomware attack against an Asian software and services firm employed a tool that was explosively associated in the past with China-linked APT groups. “Tools that are usually associated with China-based espionage actors were recently deployed in an attack involving the RA World ransomware against an Asian

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Collaboration 2.0
FEBRUARY 13, 2025
Just a heads up: The migration process can be a bit of a headache, with a long checklist -- but the option is finally here for those who've been waiting forever.
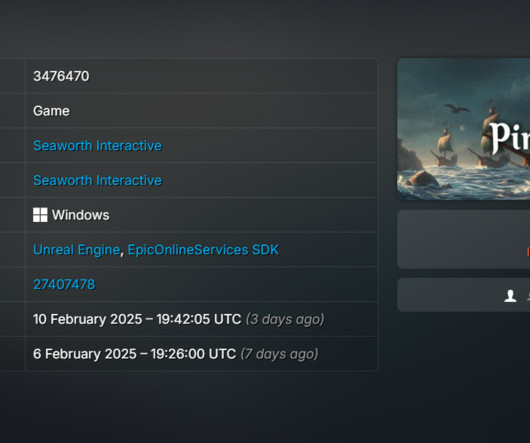
Security Affairs
FEBRUARY 13, 2025
Valve removed a game from Steam because it contained malware, the company also warned affected users to reformat their operating systems. Valve removed the game PirateFi from the Steam video game platform because it contained a Windows malicious code to steal browser cookies and hijack accounts. The company also warned affected users to fully reformatting the operating systems to remove the threat.

Collaboration 2.0
FEBRUARY 13, 2025
If you are running out of room on your internal drive, why not expand it with a few 2.5" SSD drives and this handy docking station by Sabrent.
Let's personalize your content