Fraudsters Deepfake Entire Meeting, Swindle $25.5M
Data Breach Today
FEBRUARY 5, 2024
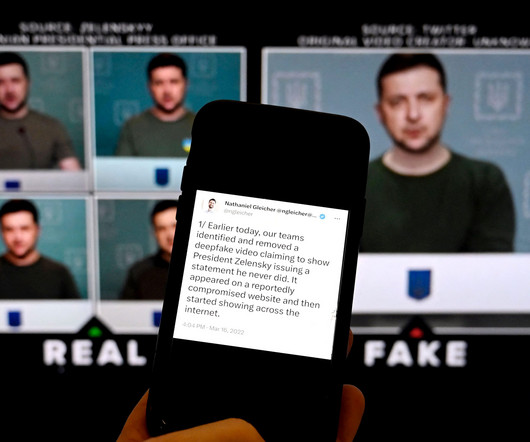
Hong Kong Company Scammed After Criminals Used Deepfake Technology to Imitate CFO Fraudsters used deepfake technology to trick an employee at a Hong Kong-based multinational company to transfer $25.57 million to their bank accounts. Hong Kong Police said Sunday that the fraudsters had created deepfake likenesses of top company executives in a video conference to fool the worker.







































Let's personalize your content