OpenAI rolls out Canvas to all ChatGPT users - and it's a powerful productivity tool
Collaboration 2.0
DECEMBER 10, 2024
For 12 days, the OpenAI daily live stream is unveiling 'new things, big and small.' Here's what's new today.

Collaboration 2.0
DECEMBER 10, 2024
For 12 days, the OpenAI daily live stream is unveiling 'new things, big and small.' Here's what's new today.

WIRED Threat Level
DECEMBER 10, 2024
The design of the gun police say they found on the alleged United Healthcare CEO's killerthe FMDA or Free Men Dont Askwas released by a libertarian group.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

AIIM
DECEMBER 10, 2024
At Shell, we recently held an IM business strategy workshop that brought together IM business leads from different lines of business. The goal? To connect the dots between information and data management and chart our approach for the coming years.

WIRED Threat Level
DECEMBER 10, 2024
Several recent schemes were uncovered involving poker players at casinos allegedly using miniature cameras, concealed in personal electronics, to spot cards. Should players everywhere be concerned?

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Data Matters
DECEMBER 10, 2024
Recent enforcement actions by both state and federal law enforcement signal that companies that make or use artificial intelligence products are facing increased scrutiny under existing unfair and deceptive acts and practices laws. Several late-2024 examples present important insights for companies navigating how to effectively and legally implement artificial intelligence technologies in their businesses.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

KnowBe4
DECEMBER 10, 2024
New analysis of ransomware attacks shows that phishing is the primary delivery method and organizations need to offer more effective security awareness training to mitigate the threat.

Security Affairs
DECEMBER 10, 2024
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Microsoft Windows Common Log File System (CLFS) driver flaw to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the Microsoft Windows Common Log File System (CLFS) driver flaw CVE-2024-49138 (CVSS score: 7.8) to its Known Exploited Vulnerabilities (KEV) catalog.

KnowBe4
DECEMBER 10, 2024
Researchers at Silent Push warn that a phishing campaign is using malicious Google Ads to conduct payroll redirect scams.

Security Affairs
DECEMBER 10, 2024
SAP has issued patches for 16 vulnerabilities, including a critical SSRF flaw in NetWeaver’s Adobe Document Services. SAP addressed 16 vulnerabilities as part of its December 2024 Security Patch Day. The company released nine new and four updated security notes. The most severe of these vulnerabilities is a critical issue, tracked as CVE-2024-47578 (CVSS score of 9.1), in the Adobe Document Service component of NetWeaver.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Schneier on Security
DECEMBER 10, 2024
This is going to be interesting. It’s a video of someone trying on a variety of printed full-face masks. They won’t fool anyone for long, but will survive casual scrutiny. And they’re cheap and easy to swap.

KnowBe4
DECEMBER 10, 2024
CyberheistNews Vol 14 #50 Cruel Year-End Twist: When Fake Firing Is A Real Phishing Attack

IG Guru
DECEMBER 10, 2024
Understanding Glucophage SR: A Comprehensive Guide for Patients In today’s fast-paced world, managing health conditions such as type 2 diabetes has become increasingly important. Glucophage SR, a widely recognized medication, plays a crucial role in controlling blood sugar levels. It’s designed to release metformin slowly, providing a steady effect throughout the day.

OpenText Information Management
DECEMBER 10, 2024
We are excited to announce our strategic partnership with Secure Code Warrior (SCW), a leader in developer-focused security training. This integration will equip developers in real time with the skills needed to efficiently identify and fix vulnerabilities, empowering your organization to transform its security posture. By combining OpenText Fortifys industry-leading static application security testing (SAST) with SCW's agile learning platform, we are set to create a powerful solution that enhan

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

Andrew Hay
DECEMBER 10, 2024
As we approach 2025, the ever-evolving landscape of cybersecurity continues to challenge professionals and organizations alike. Based on observed trends and emerging technologies, here are my predictions for the coming year. AI-Powered Threats and Defenses The ubiquity of artificial intelligence in cybersecurity is inevitable. In 2025, adversaries will use AI more effectively to bypass traditional defences.
Gimmal
DECEMBER 10, 2024
How to Avoid Writing RFP’s and Simplify the Procurement Process Written by Navigating the complexities of procurement can be overwhelming. If you’ v e e v e r been part of the purchasing process , y ou’re l ikely familiar with the labyrinth of regulations, paperwork, and time-consuming processes involved in a cquiring new products or services.

OpenText Information Management
DECEMBER 10, 2024
The lead-up to the holidays are a busy time for everyone. Is your brand designing communications for the digital-first paradigm? An omnichannel communications strategy can help win hearts and open wallets during a crucial time for your business or non-profit organization. Deloitte forecasts that holiday retail sales will grow with shoppers planning to increase their spending by 8 per cent in 2024 compared with the same period last year.
Gimmal
DECEMBER 10, 2024
How to Get Around Writing RFPs: Simplify Your Procurement with Gimmal Written by Navigating the complexities of procurement can be overwhelming. If you’ v e e v e r been part of the purchasing process , y ou’re l ikely familiar with the labyrinth of regulations, paperwork, and time-consuming processes involved in a cquiring new products or services.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

OpenText Information Management
DECEMBER 10, 2024
A leader in content services We are pleased to announce that OpenText Documentum Content Management(CM) has once again been named a Leader in Omdia Universe: Content Services Platform Solutions, 2024-25 Vendor Assessment. The report provides business and IT executives with a comprehensive evaluation of the content services market, offering valuable insights into how organizations can leverage content services solutions to accelerate digital transformation.

Unwritten Record
DECEMBER 10, 2024
Original Caption: Meeting in Paris after a two-year separation, Lt. Col. Barney Oldfield and his wife, Cpl. Vada M. Oldfield, initiate their reunion by signing each others short snorters in the shadow of the Eiffel Tower. The Oldfields come from Lincoln, Nebraska. France, 7/20/45. Local Identifier: 111-SC-210020. Going to war is never easy. Going to war in dangerous circumstances is even harder.

Security Affairs
DECEMBER 10, 2024
Resecurity uncovered a large-scale fraud campaign in the UAE where scammers impersonate law enforcement to target consumers. Resecurity has identified a wide-scale fraudulent campaign targeting consumers in the UAE by impersonating law enforcement. Victims are asked to pay non-existent fines online (traffic tickets, parking violations, driving license renewals) following multiple phone calls made on behalf of Dubai Police officers.
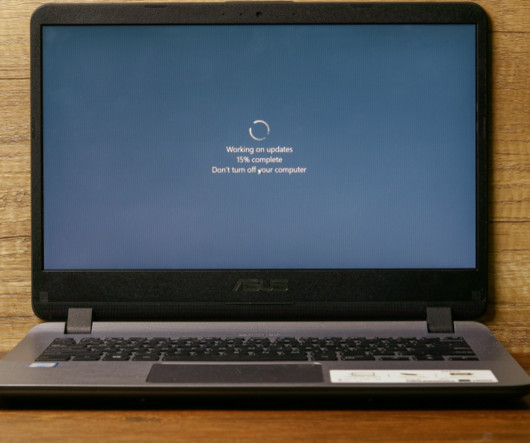
Krebs on Security
DECEMBER 10, 2024
Microsoft today released updates to plug at least 70 security holes in Windows and Windows software, including one vulnerability that is already being exploited in active attacks. The zero-day seeing exploitation involves CVE-2024-49138 , a security weakness in the Windows Common Log File System (CLFS) driver — used by applications to write transaction logs — that could let an authenticated attacker gain “system” level privileges on a vulnerable Windows device.

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.
Let's personalize your content