You have 4 days to update Firefox before everything breaks
Collaboration 2.0
MARCH 18, 2025
This upgrade isn't optional.
Collaboration 2.0
MARCH 18, 2025
This upgrade isn't optional.

Data Breach Today
MARCH 18, 2025
Malicious Code Injected in reviewdog Just Hours Before tj-actions Backdoored Just days after researchers discovered an attack that subverted a widely used tool for software development platform GitHub, they discovered a second, prior attack, as part of what one expert said may be "a chain of supply chain attacks eventually leading to a specific high-value target.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Collaboration 2.0
MARCH 18, 2025
Anyone can become a zero-knowledge threat actor now, thanks to AI.

Data Breach Today
MARCH 18, 2025
Researchers Detail AI's Fabricated Facts in Healthcare, Discuss Solutions Hallucinations in artificial intelligence foundation models are pushing healthcare professionals and technologists to rethink how practitioners can safely use AI. Hallucinated lab result or an erroneous diagnostic recommendation could lead to harmful interventions or missed treatments.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Collaboration 2.0
MARCH 18, 2025
NixOS is a well-designed OS with a fantastic array of layouts and features, but I recommend it to Linux users who aren't afraid of a little learning curve.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Collaboration 2.0
MARCH 18, 2025
As software becomes the worker, Software as a Service is being turned on its head by artificial intelligence. Meet 'Services as Software.

Data Breach Today
MARCH 18, 2025
Largest Cybersecurity Deal of All-Time Aims to Boost AI-Driven Multicloud Solutions Google Cloud plans to acquire cloud security leader Wiz for $32 billion, integrating its AI-powered security capabilities to better protect companies across multiple cloud environments. The deal reinforces protections across multicloud environments, including AWS, Microsoft Azure, and Google Cloud.

Collaboration 2.0
MARCH 18, 2025
Cybercrooks are using automated AI bots to generate multiple login attempts across a range of services. And it's about to get much worse.

Data Breach Today
MARCH 18, 2025
MirrorFace Expands Operations, Revives Anel Backdoor for Espionage A threat actor associated with Chinese cyberespionage campaigns against Japan stepped outside its East Asian comfort zone to target a European organization with a refreshed set of hacking tools. A hacking group tracked as MirrorFace and Earth Kasha deployed a backdoor once exclusively used by APT10.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Collaboration 2.0
MARCH 18, 2025
Researchers with no hacking experience jailbroke AI models to create 'infostealing malware' that can steal saved logins from Chrome.

KnowBe4
MARCH 18, 2025
Our recent research reveals a concerning discrepancy between employees' confidence in their ability to identify social engineering attempts and their actual vulnerability to these attacks.

Collaboration 2.0
MARCH 18, 2025
Google has rolled out an update to resolve the issue, but if you factory reset your device, you need to take an additional step.

Data Protection Report
MARCH 18, 2025
By David Kessler and Sue Ross Although there is scant case law on the question, it is generally accepted that it is not a violation of ones duty not to disclose information if it is stolen from you. Put another way, disclosure is an affirmative act, and, absent an affirmative duty to protect information from unauthorized access, theft of information is not a violation of a duty not to disclose.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

Collaboration 2.0
MARCH 18, 2025
The Lenovo Tab Plus boasts a surprisingly powerful speaker system and a crisp 2K display, offering an audio-visual experience that outshines some iPads.

KnowBe4
MARCH 18, 2025
A phishing campaign is impersonating travel agency Booking.com to target employees in the hospitality industry, according to researchers at Microsoft.

Collaboration 2.0
MARCH 18, 2025
New Dynamo software splits AI inference across 1,000 GPUs to boost query throughput - Nvidia's answer to investor concerns that DeepSeek cuts the processing needed.
KnowBe4
MARCH 18, 2025
My two previous recent postings on AI covered Agentic AI and how that impacts cybersecurity and the eventual emergence of malicious agentic AI malware.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

Collaboration 2.0
MARCH 18, 2025
Also known as the 'soap opera effect,' motion smoothing is ideal for gaming and live sports but less so for everything else. Here's how to turn off the feature.

Jamf
MARCH 18, 2025
Discover Jamf Pro's new blueprints configured to streamline device management workflows, or create one of your own to your specifications.

Collaboration 2.0
MARCH 18, 2025
The Kospet Tank Ultra series is a budget-friendly smartwatch packed with features typically found in higher-end models.

Security Affairs
MARCH 18, 2025
Threat actors exploit a server-side request forgery (SSRF) flaw, tracked as CVE-2024-27564, in ChatGPT, to target US financial and government organizations. Cybersecurity firm Veriti reports that threat actors are exploiting a server-side request forgery (SSRF) vulnerability, tracked as CVE-2024-27564 (CVSS score of 6.5), in ChatGPT to target financial and government organizations in the US.

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.

Collaboration 2.0
MARCH 18, 2025
The best tax filing software options like TurboTax and H&R Block can help you file your taxes more easily -- maybe even for free.

Security Affairs
MARCH 18, 2025
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Fortinet FortiOS/FortiProxyand GitHub Actionflaws to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the following vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog : CVE-2025-24472 Fortinet FortiOS and FortiProxy Authentication Bypass Vulnerability CVE-2025-30066 tj-actions/changed-files GitHub Action Embedded Malicious Code Vulnerability In Fe

Collaboration 2.0
MARCH 18, 2025
By following these seven tips from federal authorities, you can prevent Medusa from wreaking havoc on your life and business.
Security Affairs
MARCH 18, 2025
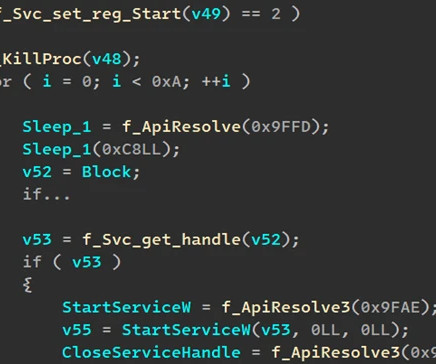
Microsoft discovered a new remote access trojan (RAT), dubbed StilachiRAT, that uses sophisticated techniques to avoid detection. In November 2024, Microsoft researchers discovered StilachiRAT, a sophisticated remote access trojan (RAT) designed for stealth, persistence, and data theft. Analysis of its WWStartupCtrl64.dll module revealed that the malware supports sophisticated functionalities to steal credentials from browsers, digital wallet data, clipboard content, and system information.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Collaboration 2.0
MARCH 18, 2025
Want to keep your personal info safe? Use this tool from ExpressVPN to see how much of it is out there.
Security Affairs
MARCH 18, 2025
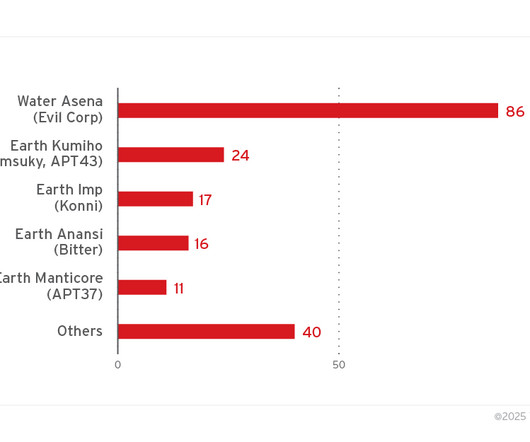
11 state-sponsored APTs exploit malicious.lnk files for espionage and data theft, with ZDI uncovering 1,000 such files used in attacks. At least 11 state-sponsored threat groups have been abusing Windows shortcut files for espionage and data theft, according to an analysis by Trend Micros Zero Day Initiative (ZDI). Trend ZDI researchers discovered 1,000 malicious.lnk files used by nation-state actors and cybercrime groups to execute hidden malicious commands on a victims machine by exploiting th

Collaboration 2.0
MARCH 18, 2025
Soundcore's Sleep A20 earbuds offer a comfortable design perfect for side sleepers. Over at Amazon, the devices are freshly discounted.
Let's personalize your content