Perplexity is the AI tool Gemini wishes it could be
Collaboration 2.0
FEBRUARY 12, 2025
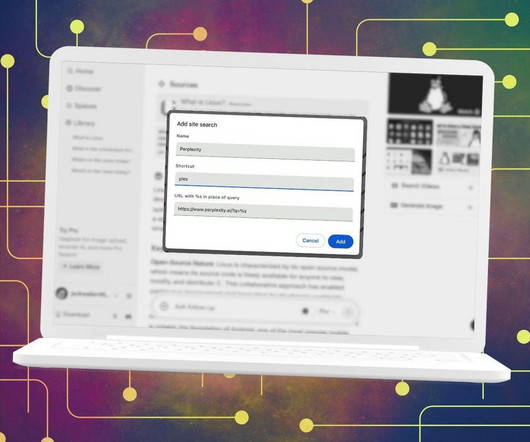
Here's why I stick with Perplexity over Google's Gemini for AI assistance, even on my Android phone.
Collaboration 2.0
FEBRUARY 12, 2025
Here's why I stick with Perplexity over Google's Gemini for AI assistance, even on my Android phone.

Schneier on Security
FEBRUARY 12, 2025
Here’s a supply-chain attack just waiting to happen. A group of researchers searched for, and then registered, abandoned Amazon S3 buckets for about $400. These buckets contained software libraries that are still used. Presumably the projects don’t realize that they have been abandoned, and still ping them for patches, updates, and etc. The TL;DR is that this time, we ended up discovering ~150 Amazon S3 buckets that had previously been used across commercial and open source software
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Collaboration 2.0
FEBRUARY 12, 2025
If you've become interested in AI, you might have automatically been drawn to Google's Gemini but there's a better way to get your answers, thanks to Perplexity.

Data Breach Today
FEBRUARY 12, 2025
Breach of GoAnywhere File Transfer App at Brightline Affected 1 Million Patients Virtual mental health provider Brightline has agreed to pay $7 million to settle a proposed class action lawsuit involving a data breach affecting about 1 million individuals stemming from the 2023 hack by ransomware gang Clop on software vendor Fortra's GoAnywhere managed file transfer application.

Advertiser: ZoomInfo
AI adoption is reshaping sales and marketing. But is it delivering real results? We surveyed 1,000+ GTM professionals to find out. The data is clear: AI users report 47% higher productivity and an average of 12 hours saved per week. But leaders say mainstream AI tools still fall short on accuracy and business impact. Download the full report today to see how AI is being used — and where go-to-market professionals think there are gaps and opportunities.

Collaboration 2.0
FEBRUARY 12, 2025
ChatGPT, Copilot, Gemini, and Perplexity were asked to summarize 100 news stories. Here's how they did.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Collaboration 2.0
FEBRUARY 12, 2025
Once upon a time, using Linux without the terminal was unthinkable. Now? For average users, the terminal is totally optional.

WIRED Threat Level
FEBRUARY 12, 2025
A team Microsoft calls BadPilot is acting as Sandworm's initial access operation, the company says. And over the last year it's trained its sights on the US, the UK, Canada, and Australia.
Collaboration 2.0
FEBRUARY 12, 2025
After nearly a decade of using the same web browser, I've finally returned to the land of Firefox, thanks to Zen Browser, and here's why.

Thales Cloud Protection & Licensing
FEBRUARY 12, 2025
The Rise of Non-Ransomware Attacks on AWS S3 Data madhav Thu, 02/13/2025 - 04:39 A sophisticated ransomware gang, Codefinger, has a cunning new technique for encrypting data stored in AWS S3 buckets without traditional ransomware tools. Instead, they exploit the AWS server-side encryption with customer-provided keys (SSE-C), extorting payment in exchange for the encryption key.

Speaker: Ben Epstein, Stealth Founder & CTO | Tony Karrer, Founder & CTO, Aggregage
When tasked with building a fundamentally new product line with deeper insights than previously achievable for a high-value client, Ben Epstein and his team faced a significant challenge: how to harness LLMs to produce consistent, high-accuracy outputs at scale. In this new session, Ben will share how he and his team engineered a system (based on proven software engineering approaches) that employs reproducible test variations (via temperature 0 and fixed seeds), and enables non-LLM evaluation m

Collaboration 2.0
FEBRUARY 12, 2025
As the video platform turns 20, creating content and expanding reach is about to get easier with more than a little help from AI. Here's what's coming.

Data Breach Today
FEBRUARY 12, 2025
Russia, China, Iran and North Korea Tapping Cybercrime Services, Google Says The cybercrime-as-a-service economy continues to power ransomware and other criminal enterprises, as well as serve as "an accelerant for state-sponsored hacking," collectively posing an increasing risk to Western national security, cybersecurity researchers warn.

Collaboration 2.0
FEBRUARY 12, 2025
A new Bloomberg report suggests that Apple will soon expand its popular streaming service to non-iOS devices.

Data Breach Today
FEBRUARY 12, 2025
Chinese State-Sponsored Cyber Group Deploying Fileless Malware to Persist Chinese state-sponsored cyber group APT40 intensified its attacks on government and critical infrastructure networks in the Pacific region by deploying fileless malware and modified commodity malware, prompting Samoa's cybersecurity agency to issue an urgent advisory.

Advertiser: ZoomInfo
ZoomInfo customers aren’t just selling — they’re winning. Revenue teams using our Go-To-Market Intelligence platform grew pipeline by 32%, increased deal sizes by 40%, and booked 55% more meetings. Download this report to see what 11,000+ customers say about our Go-To-Market Intelligence platform and how it impacts their bottom line. The data speaks for itself!

Collaboration 2.0
FEBRUARY 12, 2025
If you're facing the end of support for your operating system, I recommend giving Siduction a try - especially if you're a Pink Floyd fan.

Data Breach Today
FEBRUARY 12, 2025
Chapter 11 Looms as Eric Gan Seeks Custodian and Liberty, SoftBank Block Financing Cybereason faces a crisis as a boardroom deadlock halts financing efforts. CEO Eric Gan and his family firm seek a custodian to halt the impasse, alleging SoftBank and Liberty Strategic Capital are prioritizing control over the companys financial stability. Without urgent funding, bankruptcy looms.

Collaboration 2.0
FEBRUARY 12, 2025
While AI giants burn cash, one company quietly makes billions without the hype. Here's why every business should take note.

Data Breach Today
FEBRUARY 12, 2025
Cybersecurity Officials Launch Major Push for Zero Trust, Secure-By-Design Approach The Australian Signals Directorate's Australian Cyber Security Center released guidance on proactive cyber defense strategies to help organizations build a modern, defensible network architecture that's resilient to cyberattacks and designed to help minimize impact on critical systems and assets.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

Collaboration 2.0
FEBRUARY 12, 2025
The latest updates resolve more glitches and security flaws - some critical - in Windows 11 23H2 and 24H2, so you'll want to install them sooner rather than later.
Data Breach Today
FEBRUARY 12, 2025
US, UK and Australia Target Zservers for Supporting LockBit, Other Cybercrime Groups A Russian bulletproof hosting service used by cybercriminals including the LockBit ransomware group has been sanctioned by Australian, British and American agencies. Zservers has been advertised in criminal forums as an aid to avoid law enforcement investigations and takedowns.

Collaboration 2.0
FEBRUARY 12, 2025
Chipolo's One and Card trackers are ideal for those who frequently misplace their keys or wallets. Available individually or in multipacks, they offer a convenient solution for keeping track of your essentials.

Data Breach Today
FEBRUARY 12, 2025
New CEO Emphasizes Cryptographic Agility, Aims to Simplify Post-Quantum Migration Rebecca Krauthamer steps into the CEO role at QuSecure, leading the companys efforts in post-quantum cryptography. With fresh funding from Two Bear Capital and Accenture, she focuses on cryptographic agility to help organizations transition to quantum-safe encryption and thwart AI-driven threats.

Advertiser: ZoomInfo
Incorporating generative AI (gen AI) into your sales process can speed up your wins through improved efficiency, personalized customer interactions, and better informed decision- making. Gen AI is a game changer for busy salespeople and can reduce time-consuming tasks, such as customer research, note-taking, and writing emails, and provide insightful data analysis and recommendations.

Collaboration 2.0
FEBRUARY 12, 2025
Generating only IP-friendly content, Adobe's Firefly Video model could be a boon to professionals such as filmmakers and marketers.

Adam Shostack
FEBRUARY 12, 2025
An exciting new sample TM from MITRE For Threat Model Thursday, I want to provide some comments on NIST CSWP 35 ipd, Cybersecurity Threat Modeling the Genomic Data Sequencing Workflow (Initial Public Draft). As always, my goal is to offer helpful feedback. This is a big, complex document. Its 50 pages of real content with 13 listed authors, and is a subset of a larger project.

Collaboration 2.0
FEBRUARY 12, 2025
Looking to harvest free power for your off-grid adventures? Check out the EcoFlow River 2 Max, a portable, highly durable power station with plenty of juice.

Data Breach Today
FEBRUARY 12, 2025
Apply These Proven Methodologies to Assess, Prioritize and Act Quickly in a Crisis Cybersecurity professionals frequently deal with multiple issues - all demanding immediate attention. How can you demonstrate the ability to make sound decisions to advance your career? Decision-making in high-stakes environments demands clear methodologies that promote both efficiency and accuracy.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.
Collaboration 2.0
FEBRUARY 12, 2025
If you're a budding writer, an advanced author, or somewhere in between, you know that the right tools can help you stay organized and on track to complete that article, memoir, or manuscript.

Data Breach Today
FEBRUARY 12, 2025
WEF's Akshay Joshi on How Global Instability Is Affecting Cyber Resilience Nearly 60% of all organizations reported prevailing geopolitical instability has had an impact on their cybersecurity strategies, said Akshay Joshi, head of the Center for Cybersecurity at the World Economic Forum.

Collaboration 2.0
FEBRUARY 12, 2025
Now rolling out to the Gemini iPhone app, Deep Research finds and pulls a vast amount of data from the web and presents it to you in a comprehensive report.
Let's personalize your content