RSAC Fireside Chat: Jscrambler levels-up JavaScript security, slows GenAI-fueled privacy loss
The Last Watchdog
JUNE 10, 2024
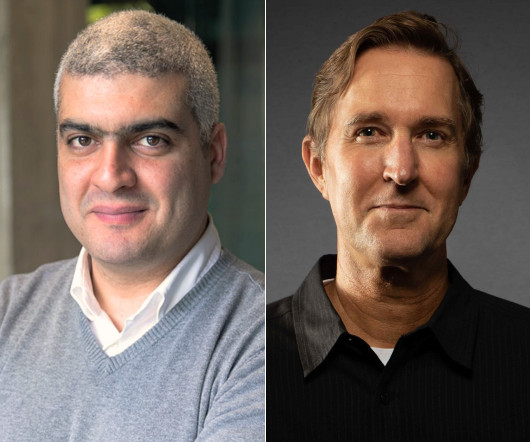
Related: Next-level browser security That’s a question that spilled out of a thought-provoking conversation I had with Pedro Fortuna , co-founder and CTO of Jscrambler , at RSAC 2024. Jscrambler provides granular visibility and monitoring of JavaScript coding thus enabling companies to set and enforce security rules and privacy policies.








































Let's personalize your content