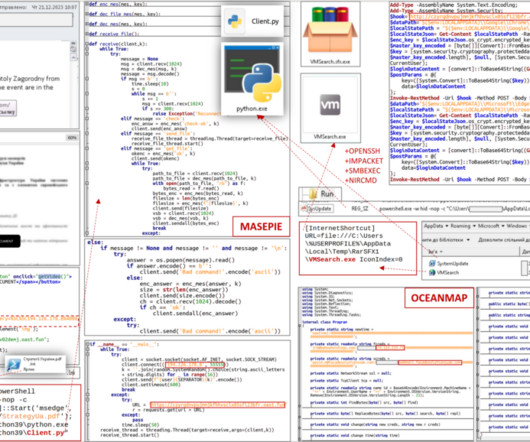
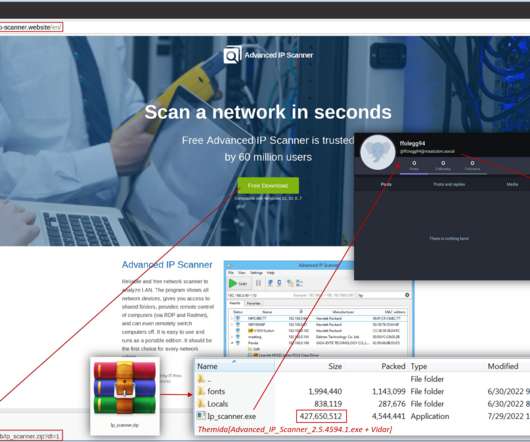
Estonian National charged with helping Russia acquire U.S. hacking tools and electronics
Security Affairs
APRIL 9, 2023
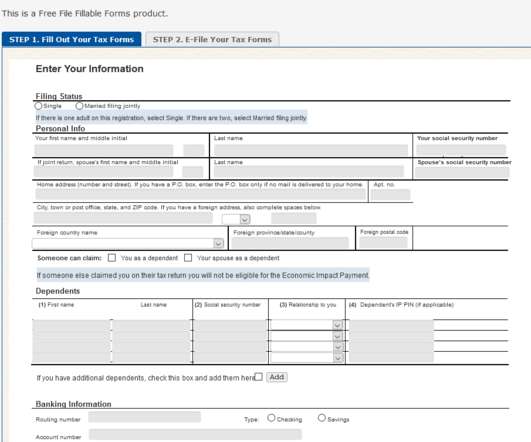
made electronics on behalf of the Russian government and military. The Estonian man is accused of having helped the Russian government and military to purchase US-made electronics and hacking tools. “Shevlyakov also attempted to acquire computer hacking tools.”









































Let's personalize your content