2024 Cybersecurity Laws & Regulations
eSecurity Planet
SEPTEMBER 21, 2024
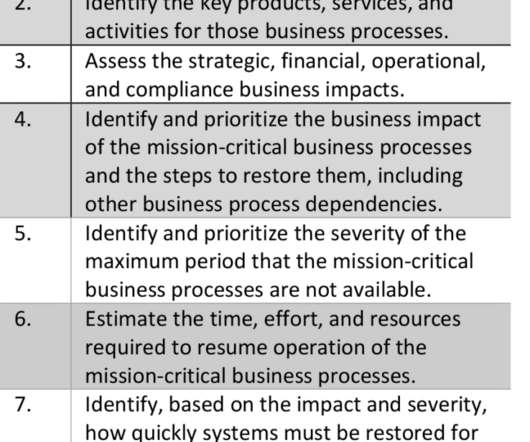
These laws aim to establish standards for securing data, ensuring privacy, and mitigating risks associated with digital information. Various federal agencies enforce them and may include guidelines for implementing security measures, conducting risk assessments, and ensuring compliance with national security objectives.













































Let's personalize your content