Good Governance is About the “Why”
Weissman's World
JANUARY 30, 2025
I get inquiries all the time from people seeking support as they ready to tackle what sound like fairly specific records and information governance issues.
Weissman's World
JANUARY 30, 2025
I get inquiries all the time from people seeking support as they ready to tackle what sound like fairly specific records and information governance issues.

Security Affairs
OCTOBER 22, 2024
vCenter Server is a critical component in VMware virtualization and cloud computing software suite. ” Chinese law requires researchers to disclose zero-day vulnerabilities to the government. Experts speculate that the Chinese government was aware of the flaw and may have exploited it as a zero-day.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Weissman's World
NOVEMBER 11, 2024
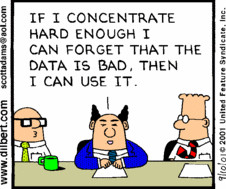
The adage “garbage in, garbage out” (GIGO) has been around for nearly 70 years, and it’s never been more relevant thanks to the intensifying need for information governance and the emergence of generative and agentic AI as potential disruptors. Regardless of your mandate (e.g.,

Security Affairs
DECEMBER 19, 2020
The US National Security Agency (NSA) warns of two techniques abused by threat actors for escalating attacks from local networks to cloud infrastructure. The US National Security Agency has published a security advisory that describes two techniques abused in recent attacks against cloud infrastructure. ” continues the alert.
Advertisement
To address this, a next-gen cloud data lake architecture has emerged that brings together the best attributes of the data warehouse and the data lake. Read this whitepaper to learn: How this “no data copy” approach dramatically streamlines data workflows while reducing security and governance overhead.

Security Affairs
JANUARY 14, 2021
The US CISA revealed that several recent successful cyberattacks against various organizations’ cloud services. . The Cybersecurity and Infrastructure Security Agency (CISA) announced that several recent successful cyberattacks hit various organizations’ cloud services. ” reads the report published by CISA. Pierluigi Paganini.
Security Affairs
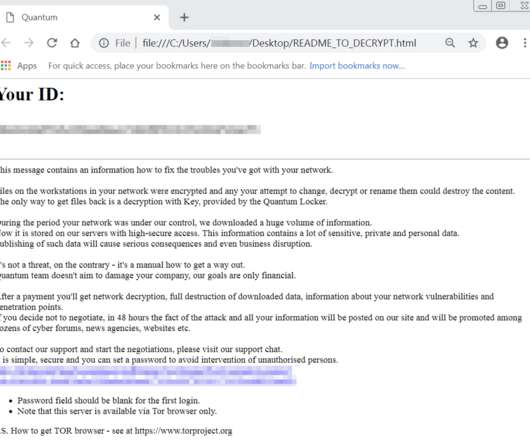
NOVEMBER 23, 2022
The gang behind Quantum Locker used a particular modus operandi to target large enterprises relying on cloud services in the NACE region. Quantum Locker gang demonstrated capabilities to operate ransomware extortion even on cloud environments such as Microsoft Azure. Executive Summary. Source Cybereason. Incident Insights.

Speaker: Jeremiah Morrow, Nicolò Bidotti, and Achille Barbieri
Yet they are continually challenged with providing access to all of their data across business units, regions, and cloud environments. In this session, you will learn: How the silos development led to challenges with data growth, data quality, data sharing, and data governance (an example of datamesh paradigm adoption).
Advertisement
Leverage the Cloud Development Environment Maturity Model to elevate your software development practices with scalable, secure cloud-based workspaces. By implementing Cloud Development Environments (CDEs), teams can boost efficiency, improve security, and streamline operations through centralized governance.
Speaker: Crystal Cao, Lindsey Simon & Lisa Ripley
Cloud applications are driving the future of work with the ability to operate anytime, anywhere. Join Onna and experts from Quip, Airbnb, and Oracle for this live webinar as they dive into proactive data deletion policies, retention strategies, and legal hold practices that are essential to a modern enterprise information governance strategy.
Advertisement
Increasingly, enterprises are leveraging cloud data lakes as the platform used to store data for analytics, combined with various compute engines for processing that data. Read this paper to learn about: The value of cloud data lakes as the new system of record.
Let's personalize your content