Crypto Mining Service Coinhive to Call it Quits
Krebs on Security
FEBRUARY 27, 2019
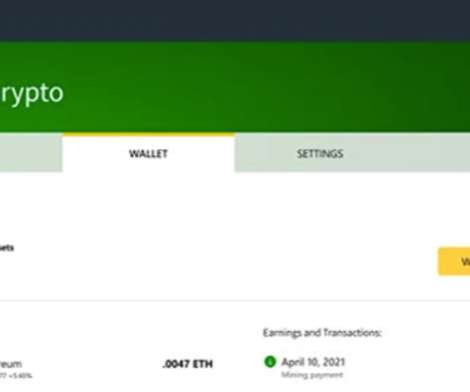
com , a cryptocurrency mining service that has been heavily abused to force hacked Web sites to mine virtual currency. Coinhive took a whopping 30 percent of the cut of all Monero currency mined by its code, and this presented something of a conflict of interest when it came to stopping the rampant abuse of its platform.








































Let's personalize your content