Risk Management under the DORA Regulation
IT Governance
NOVEMBER 23, 2023
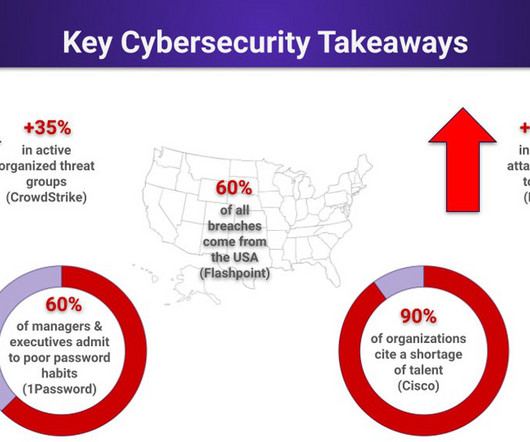
In fact, in 2020–2022, the financial sector was the second-most attacked sector, topped only by the retail and manufacturing sector. That said, remember to consider risks to the confidentiality, integrity, availability and authenticity of each ICT asset: Confidentiality : The asset is accessible to authorised people only.



















Let's personalize your content