CISA Urges Exchange Online Authentication Update
eSecurity Planet
JUNE 30, 2022
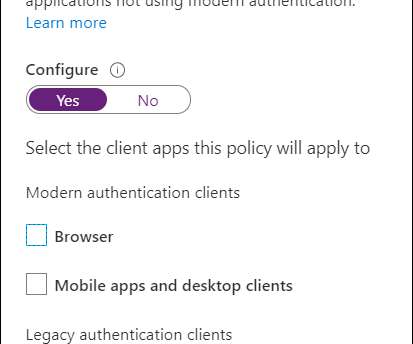
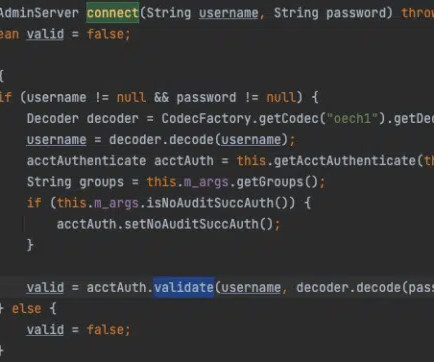
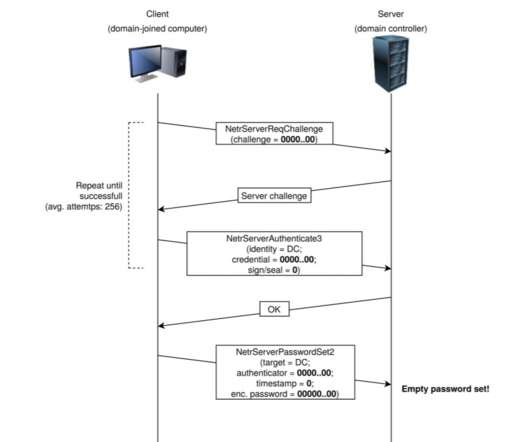
CISA noted that Basic authentication is simple and pretty convenient but unsecured by design. And it’s incompatible with multi-factor authentication (MFA) systems , so admins might be discouraged from enabling it. or Microsoft Active Directory Authentication Library uses tokens that expire quickly and cannot be reused elsewhere.



































Let's personalize your content