Long Article on GM Spying on Its Cars’ Drivers
Schneier on Security
APRIL 26, 2024
Kashmir Hill has a really good article on how GM tricked its drivers into letting it spy on them—and then sold that data to insurance companies.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Schneier on Security
APRIL 26, 2024
Kashmir Hill has a really good article on how GM tricked its drivers into letting it spy on them—and then sold that data to insurance companies.

The Last Watchdog
AUGUST 24, 2020
Purchasing life insurance once meant going to an insurer’s office or booking an appointment with an insurance agent. Today’s generation is used to getting everything done fast and easy, so life insurance providers had to get with the times and cover all customers’ needs and requirements.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Launching LLM-Based Products: From Concept to Cash in 90 Days
Driving Responsible Innovation: How to Navigate AI Governance & Data Privacy

Data Protection Report
MARCH 21, 2023
2] In this context, the Directorate General of the French Treasury has put forward a plan of action with a view to clarifying the cyber-insurance legal framework, better gauging cyber-risks, and enhancing companies’ awareness as regards cyber-risks. 12-10-1 into the French Insurance code. However, in the end, Article L.12-10-1

Schneier on Security
JULY 1, 2021
Here’s one more contribution to that issue: a research paper that the insurance industry is hurting more than it’s helping. Although it is a societal problem, cyber insurers have received considerable criticism for facilitating ransom payments to cybercriminals. News article. Often, that’s paying the ransom.

DLA Piper Privacy Matters
MARCH 27, 2023
LOPMI introduces amendments to the insurability of losses and damages paid in response to cyber-attacks, including in relation to ransom payments – requiring that the payment of insurance compensation be conditional on the filing of a complaint, within a 72 hour time frame, to competent authorities.
Hunton Privacy
JANUARY 5, 2024
Background The case related to the processing of an incapacitated employee’s personal data, including health data, by the medical service provider (“MDK”) of a health insurance fund in Germany. Under applicable law, the MDK draws up reports on the capacity of individuals insured by the health insurance fund to work.

IBM Big Data Hub
DECEMBER 4, 2023
IBM can help insurance companies insert generative AI into their business processes IBM is one of a few companies globally that can bring together the range of capabilities needed to completely transform the way insurance is marketed, sold, underwritten, serviced and paid for.

Krebs on Security
APRIL 15, 2019
Indian information technology (IT) outsourcing and consulting giant Wipro Ltd. [ NYSE:WIT ] is investigating reports that its own IT systems have been hacked and are being used to launch attacks against some of the company’s customers, multiple sources tell KrebsOnSecurity. Wipro has refused to respond to questions about the alleged incident.

IBM Big Data Hub
JUNE 23, 2023
Although interest rates have increased at an unprecedented rate over the past year due to efforts by central banks to curb inflation, insurers are locked into low-yielding investments, and it will take several years for their investment yields to improve. Core modernization (processes and technology) is a top priority for every insurer.

Schneier on Security
APRIL 12, 2018
Good article about how difficult it is to insure an organization against Internet attacks, and how expensive the insurance is. In my new book -- out in September -- I write: There are challenges to creating these new insurance products. There are two basic models for insurance. BoingBoing article.

Security Affairs
SEPTEMBER 8, 2024
Security Affairs Malware newsletter includes a collection of the best articles and research on malware in the international landscape.
Lenny Zeltser
JULY 1, 2020
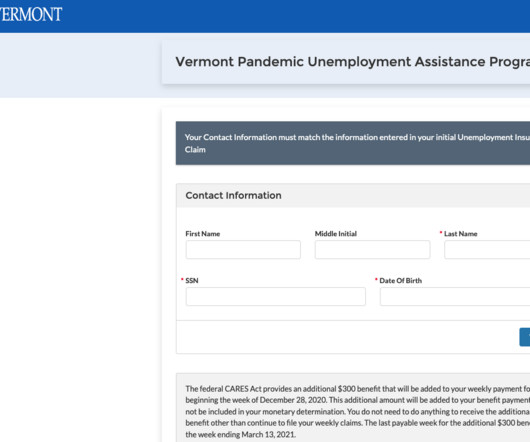
According to the New York Times article from May 2020 , the US Secret Service “had information suggesting that the scheme was coming from a well-organized Nigerian fraud ring.” The criminals behind this scheme are probably counting on this. ” An Unsolicited Debit Card: One Sign You May Be a Victim.

Hunton Privacy
NOVEMBER 27, 2017
On November 3, 2017, Securityroundtable.org published an article highlighting the vulnerabilities businesses face in a world of e-commerce and interconnectivity, and spotlighted a crisis-planning panel hosted by Hunton & Williams held on November 1. For a recap of the event, read the full Securityroundtable.org article.

KnowBe4
AUGUST 24, 2022
Reporter Aaron Holmes just published an article that is an eye opener for sure. Here is s short extract and I recommend you reading the whole article, link is below. One of these is called '" The Information " which covers in-depth tech stories usually earlier than anywhere else.

Schneier on Security
JANUARY 19, 2022
Doctors Clinical Lab, the lab Center for COVID Control uses to process tests, makes money by billing patients’ insurance companies or seeking reimbursement from the federal government for testing. Read the article for the messy details. The companies will keep making money for the rapid tests they collect, he said.

DLA Piper Privacy Matters
OCTOBER 23, 2018
The Financial Supervisory Authority in Finland (FIN-FSA) has on 16 October 2018 published an interpretation that provision of insurance against administrative fines and penalty payments is contrary to good insurance practice and is therefore not permitted. Interpretation of ‘Good Insurance Practice‘. Possible implications.

Thales Cloud Protection & Licensing
JANUARY 16, 2024
As set out in its Article 2, DORA applies to the entire financial services sector. That includes banks, insurances, payment institutions, stock market, and many financial management firms (trading, crypt-assets, etc). What is the scope of DORA? Regulated entities mentioned above must comply to DORA.

Data Protection Report
SEPTEMBER 23, 2021
The matter involved one of France’s largest insurers, SGAM AG2R LA MONDIALE, which was subject to an inspection by the French data protection authority (the CNIL), in 2019. The CNIL’s inspection included the insurer’s compliance with Section 5-1(e) of GDPR , which reads: Personal data shall be. (e) Perhaps the CNIL’s €1.75
Security Affairs
SEPTEMBER 8, 2024
Every week the best security articles from Security Affairs are free in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.

AIIM
MARCH 12, 2018
Over 100 eBooks, Guest articles, and Tip Sheets from the past year or so -- 107 of them to be exact. Getting Ahead of the Disruption Curve is Critical for Insurance Companies. A winning recipe: SaaS + Cloud Content Management + IaaS. Modern problems require modern solutions: Meeting the challenge of Big Content. And the What? -
Security Affairs
JULY 21, 2021
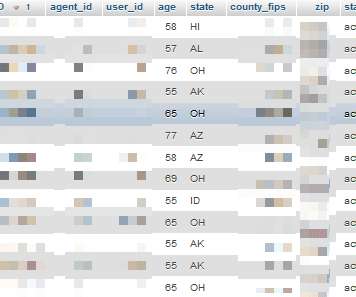
Experts found a DB containing sensitive health insurance data belonging to customers of US insurance giant Humana. An SQL database containing what appears to be highly sensitive health insurance data of more than 6,000 patients has been leaked on a popular hacker forum. Drug prescription listings). Who had access to the data?

Data Protection Report
JULY 28, 2021
The FCJ held that Article 15 of the EU General Data Protection Regulation (GDPR) has a broader scope than previously understood in Germany. The defendant was a life insurance company and the claimant their insured. The claimant appealed this decision to the FCJ.

Hunton Privacy
AUGUST 10, 2017
Circuit reversed the dismissal of a putative data breach class action against health insurer CareFirst, Attias v. 1, 2017), finding the risk of future injury was not too speculative to establish injury in fact under Article III. . CareFirst, Inc. , 16-7108, slip op.

CGI
FEBRUARY 28, 2017
Insurers’ digital focus is looking through the wrong ‘lens’. Read any article on digital insurance and it seems to me that it is all about the insurers! harini.kottees…. Tue, 02/28/2017 - 03:52.

Security Affairs
OCTOBER 1, 2023
Immediately after detecting the intrusion, the company launched an investigation with the help of leading third-party cybersecurity experts and is also coordinating with its insurers. ” reads the article published by CNN. “We The security breach forced the company to shut down its systems to prevent the threat from spreading.

Hunton Privacy
JUNE 16, 2014
As companies seek out ways to prevent these events and recoup losses associated with a data breach, cyber insurance is increasingly discussed as an effective method of recovery. In a recent article published in the Daily Journal , Hunton & Williams’ Insurance Coverage Counseling and Litigation attorney William T.

HL Chronicle of Data Protection
MAY 13, 2019
In the past two years, multiple state bills that have been introduced in the US to provide for cybersecurity requirements and standards to the insurance sector, with recent legislative activity taking place in particular within the States of Ohio, South Carolina, and Michigan. NYDFS: Setting a new bar for state cybersecurity regulation.
Security Affairs
JANUARY 7, 2024
Every week the best security articles from Security Affairs are free for you in your email box. Experts spotted a new macOS Backdoor named SpectralBlur linked to North Korea Merck settles with insurers regarding a $1.4 A new round of the weekly SecurityAffairs newsletter arrived!

eSecurity Planet
MARCH 18, 2022
In this article, we’ll briefly touch on what policies are; tips for writing them; and the advantages policies provide for compliance, transitions, and IT team liability. Even though drafting IT security policies can be a pain, formal policies provide a valuable resource to protect both the IT team and their organization.

CGI
AUGUST 31, 2016
Insurers’ role will be critical in improving cybersecurity standards. Cyber insurance can be obtained to cover such costs as crisis management, media management, incident management, technical remediation, legal fees, call management, data subject notification, breach investigation and many other losses resulting from a cyber-attack.

Hunton Privacy
APRIL 15, 2016
As reported on the Hunton Insurance Recovery Blog , data breach claims involving customer data can present an ever-increasing risk for companies across all industries. Syed Ahmad , a partner in the Hunton & Williams LLP insurance practice, was quoted in a Law360 article concerning the importance of this decision.

Hunton Privacy
OCTOBER 25, 2022
million fine to Interserve Group Limited for failing to keep employee personal data secure, which violates Article 5(1)(f) and Article 32 of the EU General Data Protection Regulation (“GDPR”), during the period of March 2019 to December 2020. On October 24, 2022, the UK Information Commissioner’s Office (“ICO”) issued a £4.4
Krebs on Security
APRIL 27, 2023
health administrators are still smarting from a data breach earlier this year at the health insurance exchange DC Health Link , which exposed personal information for more than 56,000 users, including many members of Congress. A researcher found DC Health had five Salesforce Community sites exposing data. Washington, D.C. ”

IT Governance
OCTOBER 11, 2022
Why Cyber Insurance is Essential in 2022. Many of their requirements overlap, particularly in relation to Article 32 of the Regulation. One of the most common mistakes that organisations make when addressing cyber security is that they consider it a one-off event. How we can help.

Security Affairs
FEBRUARY 25, 2024
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.

Schneier on Security
NOVEMBER 13, 2020
If you want your insurance company to have access to your fitness data, you grant it through your pod. A few news articles. Your data is no longer in a bazillion places on the Internet, controlled by you-have-no-idea-who. It’s yours. If you want your friends to have access to your vacation photos, you grant it through your pod.
Security Affairs
MARCH 17, 2024
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.

Adam Levin
JUNE 4, 2021
Upon publication of this article, the Exagrid website still touted seven industry awards for work in the area of ransomware recovery solution, but this attack will harm its reputation, proving once again that no one is immune from the scourge of a well-targeted attack. million after it was hit with Conti ransomware. .
Security Affairs
FEBRUARY 26, 2023
Every week the best security articles from Security Affairs are free for you in your email box. A new round of the weekly SecurityAffairs newsletter arrived! If you want to also receive for free the newsletter with the international press subscribe here.

eSecurity Planet
AUGUST 9, 2022
The GDPR provision that may keep IT security teams busiest is Article 32, which requires “a process for regularly testing, assessing and evaluating the effectiveness of technical and organizational measures for ensuring the security of the processing” of personal data. See the Top Governance, Risk and Compliance (GRC) Tools. Location Matters.

Hunton Privacy
APRIL 4, 2017
In March 2017, Syed Ahmad, a partner with Hunton & Williams LLP’s insurance practice, and Eileen Garczynski, partner at insurance brokerage Ames & Gough, co-authored an article, Protecting Company Assets with Cyber Liability Insurance , in Mealey’s Data Privacy Law Report. Read the full article.

Security Affairs
JULY 24, 2022
Every week the best security articles from Security Affairs for free in your email box. A new round of the weekly Security Affairs newsletter arrived! If you want to also receive for free the newsletter with the international press subscribe here. released in Dark Web – malicious shortcut-based attacks are on the rise Tor Browser 11.5

Hunton Privacy
JANUARY 18, 2019
Article 28 of the EU General Data Protection Regulation (the “GDPR”) requires data controllers enter into data processing agreements with data processors. The Dutch DPA indicated that the targeted organizations are mainly in energy, media and trade sectors.

Adam Levin
SEPTEMBER 4, 2019
According to a representative of Euler Hermes Group SA, the firm’s insurance company, the CEO was targeted by a new kind of scam that used AI-enhanced technology to create an audio deepfake of his employer’s voice. Read the Wall Street Journal article here (subscription required).
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content