GDPR and The Data Governance Imperative
AIIM
SEPTEMBER 12, 2018
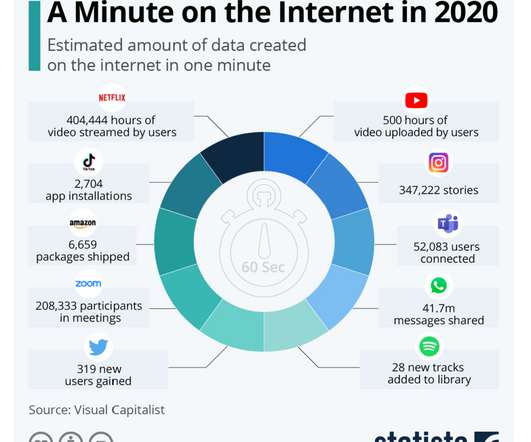
GDPR and the Data Governance Imperative. The confluence of big data, cloud computing, social media, mobile devices collect and aggregate diverse data sets, which taken together, such as internet search habits and GPS tracking information may expose personally identifiable information. The Information Governance Imperative.









































Let's personalize your content