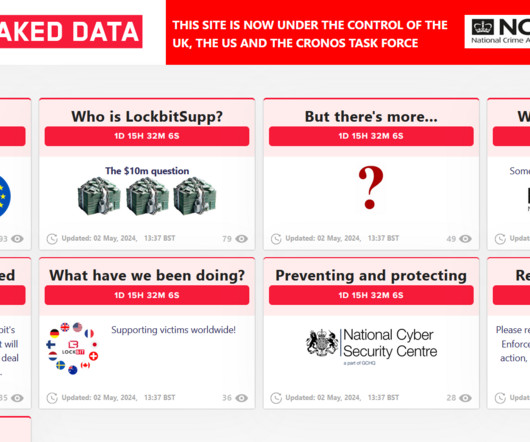
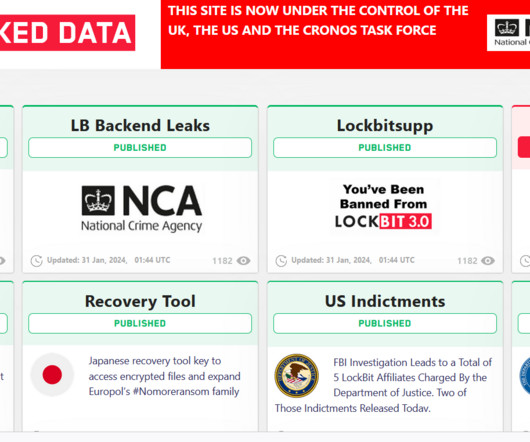
Operation Cronos: law enforcement disrupted the LockBit operation
Security Affairs
FEBRUARY 19, 2024
An international law enforcement operation codenamed ‘Operation Cronos’ led to the disruption of the LockBit ransomware operation. A joint law enforcement action, code-named Operation Cronos, conducted by law enforcement agencies from 11 countries has disrupted the LockBit ransomware operation. on January 5, 2020.
















Let's personalize your content