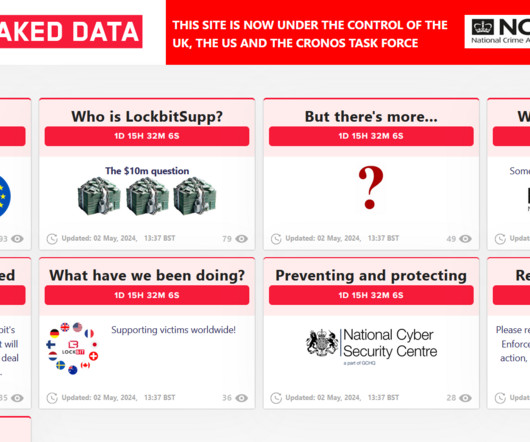
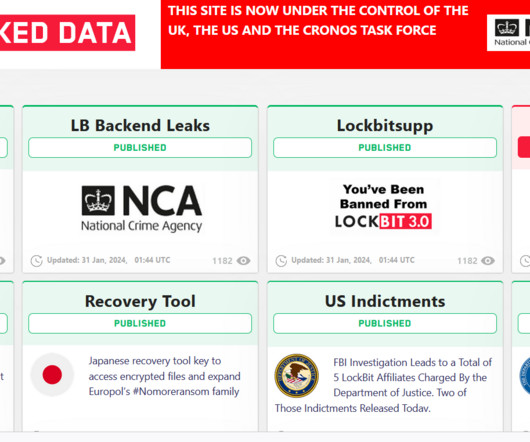
FBI obtained 7,000 LockBit decryption keys, victims should contact the feds to get support
Security Affairs
JUNE 6, 2024
Law enforcement also had access to data stolen from the victims of the ransomware operation, a circumstance that highlights the fact that even when a ransom is paid, the ransomware gang often fails to delete the stolen information. In 2022, LockBit was one of the most active ransomware groups, and its prevalence continued into 2023.















Let's personalize your content