InfoGovCon 2016 Promo Video
JKevinParker
JULY 20, 2016
Check out the new promo video for InfoGovCon 2016 ! I'm excited to be one of the speakers for this exciting event. You should come! Learn more at: www.InfoGovCon.com.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

JKevinParker
JULY 20, 2016
Check out the new promo video for InfoGovCon 2016 ! I'm excited to be one of the speakers for this exciting event. You should come! Learn more at: www.InfoGovCon.com.

Hunton Privacy
JULY 26, 2019
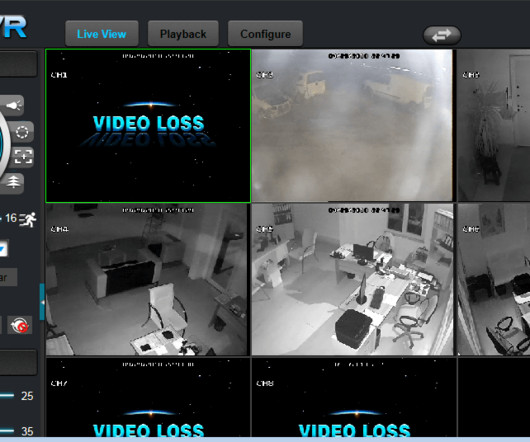
The European Data Protection Board (the “EDPB”) recently adopted its Guidelines 3/2019 on processing of personal data through video devices (the “Guidelines”). Although the Guidelines provide examples of data processing for video surveillance, these examples are not exhaustive.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Launching LLM-Based Products: From Concept to Cash in 90 Days
Driving Responsible Innovation: How to Navigate AI Governance & Data Privacy

Krebs on Security
JULY 17, 2019
The name of this particular card shop won’t be mentioned here, and its various domain names featured in the video have been pixelated so as not to further promote the online store in question. WARNING: Some viewers may find this video disturbing. He now works as a private cybersecurity consultant).
Krebs on Security
JULY 18, 2022
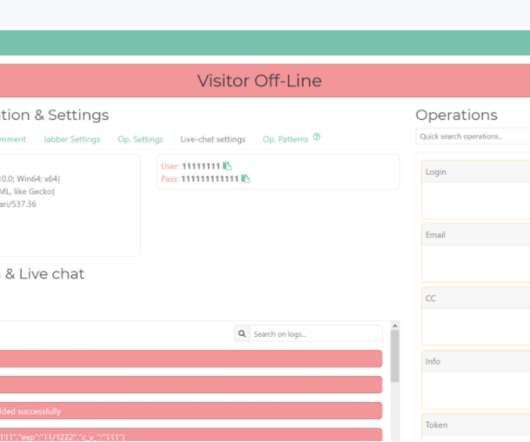
The 911 user interface, as it existed when the service first launched in 2016. net available at the Wayback Machine shows that in 2016 this domain was used for the “ ExE Bucks ” affiliate program, a pay-per-install business which catered to people already running large collections of hacked computers or compromised websites. .

Hunton Privacy
MARCH 29, 2017
On March 28, 2017, the French Data Protection Authority (“CNIL”) published its Annual Activity Report for 2016 (the “Report”) and released its annual inspection program for 2017. The CNIL estimates that the GDPR will lead to the appointment of a data protection officer in at least 80,000 to 100,000 organizations in France. smart TVs.
Krebs on Security
MARCH 10, 2020
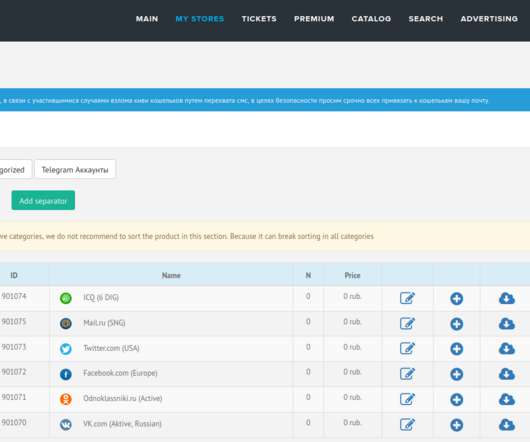
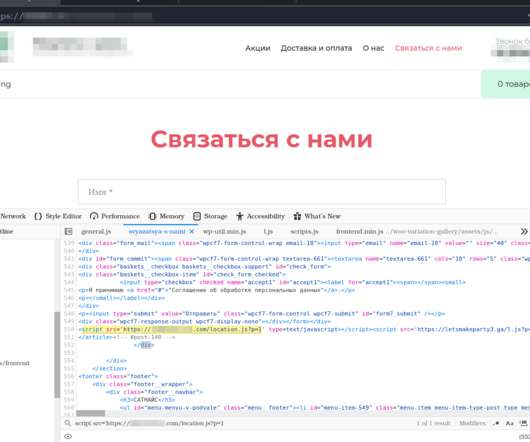
In addition to facilitating the sale of hacked accounts at video streaming services like Netflix and Hulu and social media platforms like Facebook , Twitter and Vkontakte (the Russian equivalent of Facebook), deer.io The user asks why Isis’s site — a video and music search site called vpleer[.]ru
Security Affairs
MAY 2, 2023
A remote attacker can trigger the flaw to obtain administrative privileges and eventually gain access to camera video feeds. TBK Vision is a video surveillance company that provides network CCTV devices and other related equipment, including DVRs for the protection of critical infrastructure facilities. in MVPower CCTV DVR models.

Hunton Privacy
JULY 11, 2016
On July 6, 2016, the Bavarian Data Protection Authority (“DPA”) issued a short paper on video surveillance under the EU General Data Protection Regulation (“GDPR”). According to the DPA, video surveillance under the GDPR can be legitimized based on the general legal ground of legitimate interest following a balancing test.

Schneier on Security
MAY 3, 2024
TEDxPSU 2010: “ Reconceptualizing Security ” TEDxCambridge 2013: “ The Battle for Power on the Internet ” TEDMed 2016: “ Who Controls Your Medical Data ?” I have spoken at several TED conferences over the years. ” I’m putting this here because I want all three links in one place.

Schneier on Security
JUNE 13, 2024
In January, Muthuvel Karunanidhi, former chief minister of the southern state of Tamil Nadu for two decades, appeared via video at his party’s youth wing conference. ” Jayalalithaa died in 2016. He wore his signature yellow scarf, white shirt, dark glasses and had his familiar stance—head slightly bent sideways.

eDiscovery Daily
FEBRUARY 18, 2019
O’Hara denied the plaintiff’s motion for sanctions based on the defendant’s alleged spoliation of a surveillance video that shows an altercation between the plaintiff and her supervisor, stating that “plaintiff has failed to meet the requirements of Fed. Case Background. The plaintiff subsequently filed the suit in July 2017.
Security Affairs
FEBRUARY 2, 2024
According to his LinkedIn profile , Schulte worked for the NSA for five months in 2010 as a systems engineer, after this experience, he joined the CIA as a software engineer and he left the CIA in November 2016. Schulte was identified a few days after WikiLeaks started leaking the precious dumps.

Security Affairs
JUNE 8, 2023
Researchers from Singapore-based cybersecurity firm Numen Cyber have published a detailed analysis of the vulnerability along with a proof-of-concept (PoC) exploit that works against Windows Server 2016. Below is a video demonstrating how the exploit works on Windows Server 2016.

Hunton Privacy
JULY 8, 2019
The updates aim to answer questions about data breaches received by the Dutch DPA from organizations since 2016. In the Netherlands, a data breach notification regime has been in place since 2016. The Dutch DPA also developed practical tools to help organizations understand what to do in the event of a data breach.

Krebs on Security
SEPTEMBER 19, 2018
Mirai enslaves poorly secured “Internet of Things” (IoT) devices like security cameras, digital video recorders (DVRs) and routers for use in large-scale online attacks. Not long after Mirai first surfaced online in August 2016, White and Jha were questioned by the FBI about their suspected role in developing the malware.
Security Affairs
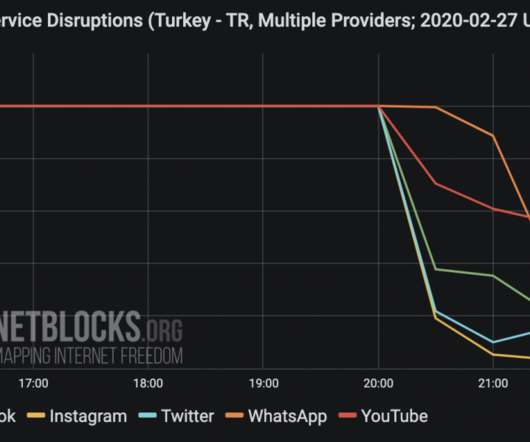
FEBRUARY 28, 2020
This isn’t the first time that the government adopted similar restrictions, when the Operation Euphrates Shield begun on Thursday, 25 August 2016, the government blocked major social media platforms, including Facebook, Twitter, YouTube, Vimeo, and Instagram. ”added Netblocks. It's 5:30 a.m.

The Last Watchdog
SEPTEMBER 5, 2023
The Mirai botnet, initially discovered in October 2016 , infected Internet-connected routers, cameras and digital video recorders at scale. Here are a few takeaways: Minimum requirements A few years back, a spate of seminal IoT hacks grabbed the full attention of governments worldwide.

Krebs on Security
JANUARY 24, 2023
Many of the infected systems were Internet of Things (IoT) devices , including industrial control systems, time clocks, routers, audio/video streaming devices, and smart garage door openers. RSOCKS, circa 2016. Later in its existence, the RSOCKS botnet expanded into compromising Android devices and conventional computers.
Hunton Privacy
NOVEMBER 10, 2020
On November 9, 2020, the Federal Trade Commission announced it had entered into an consent agreement (the “Proposed Settlement”) with Zoom Video Communications, Inc.

Preservica
SEPTEMBER 20, 2016
The event was opened by Hwang Kyo-ahn, the Prime Minister of South Korea, followed by a video message from the President of South Korea, Park Geun-hye. The event attracts a high number of senior practitioners including head archivists with extensive experience.
Krebs on Security
FEBRUARY 8, 2021
“Universal Admin,” is crimeware platform that first surfaced in 2016. The video below, produced by the U-Admin developer, shows a few examples (click to enlarge). A demonstration video showing the real-time web injection capabilities of the U-Admin phishing kit. ” U-Admin, a.k.a. Credit: blog.bushidotoken.net.

The Guardian Data Protection
MAY 2, 2018
The CBA’s acting group executive for retail banking services, Angus Sullivan, issued a video statement on YouTube after BuzzFeed Australia published an article about the incident on Wednesday. Related: Banking royal commission: CBA admits it failed to find system error for four years Continue reading.
ARMA International
APRIL 18, 2022
resumes, personnel files, video/call recordings). 2016/679 (EU, April 27). 2016/679, Art. 2016/679 (EU, April 27). 2016/679, Art. A data subject request is an action by an individual to exercise that right, and the organization has an obligation to respond to that request 10 11. Conclusion. 2 DLA Piper. 2000. . §

Troy Hunt
FEBRUARY 6, 2020
I hope the audio (and video) improvements this week do the job, I'll do it all again from Sydney next week with (hopefully) a much improved audio setup. References I'm speaking at the Azure user group in Sydney on Tuesday night (only 15 spots left at the time of writing so get in quick if you're going to be around!)
Security Affairs
SEPTEMBER 30, 2020
Security experts Simon Zuckerbraun from Zero Day Initiative published technical details on how to exploit the Microsoft Exchange CVE-2020-0688 along with a video PoC. Researchers from Rapid7 reported that 61 percent of Exchange 2010, 2013, 2016 and 2019 servers are still vulnerable to the vulnerability.
Security Affairs
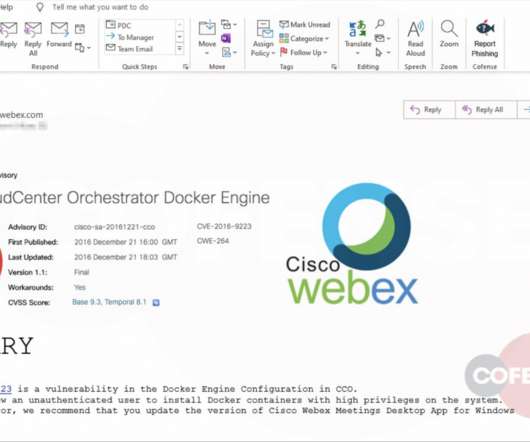
APRIL 11, 2020
The number of users for video conferencing applications like Zoom and Webex is spiked in recent weeks. The messages link the legitimate advisory for the CVE-2016-9223 vulnerability: hxxps://cve[.]mitre[.]org/cgi-bin/cvename.cgi?name=CVE-2016-9223. name=CVE-2016-9223. org/cgi-bin/cvename.cgi?name=CVE-2016-9223.

National Archives Records Express
OCTOBER 9, 2020
We would like to remind agencies of the products we’ve created regarding transition: Memorandum from Archivist of the United States to the Senior Agency Officials for Records Management 2016 Web Edition of Documenting Your Public Service featuring social media account guidance Video Briefing on Records Management Guidance for Political Appointees featuring (..)
Security Affairs
DECEMBER 27, 2023
The 2016 US presidential elections and Brexit have demonstrated how, through the manipulation of information, it is possible to influence the perception of entire populations on issues of interest to the community.

Krebs on Security
OCTOBER 26, 2018
2016 attack that sidelined this Web site for nearly four days. 2016 attack on KrebsOnSecurity and several other targets, Jha and his cohorts released the source code for Mirai in a bid to throw investigators off their trail. “He won’t be going to back to school right now or to his job.” After the Sept.

Security Affairs
JULY 23, 2021
The attack can potentially impact most of the supported Windows versions, it was successfully tested against Windows 10, Windows Server 2016, and Windows Server 2019 systems. Mimikatz author Benjamin Delpy also successfully tested the PetitPotam attack and published a video PoC of the attack.

Krebs on Security
OCTOBER 22, 2018
“It logs keys and clipboards data, captures screen and video, and performs form-grabbing (Instagram, Twitter, Gmail, Facebook, etc.) Sometime in mid-2016 the site’s registration records were hidden behind WHOIS privacy services [full disclosure: Domaintools is a previous advertiser on KrebsOnSecurity].

Security Affairs
MARCH 16, 2020
Security experts Simon Zuckerbraun from Zero Day Initiative published technical details on how to exploit the Microsoft Exchange CVE-2020-0688 along with a video PoC. The vulnerability impacts Microsoft Exchange 2010, 2013, 2016, and 2019. “How many of these are vulnerable? ” continues the report.
Security Affairs
DECEMBER 30, 2022
Newspaper Theme on WordPress Access Control (vulnerability CVE-2016-10972). FV Flowplayer Video Player. WordPress – Yuzo Related Posts. Yellow Pencil Visual Theme Customizer Plugin. WP GDPR Compliance Plugin. Google Code Inserter. Total Donations Plugin. Post Custom Templates Lite. WP Quick Booking Manager. WooCommerce.

Outpost24
JUNE 7, 2017
First, the Mirai botnet, in late 2016, affected internet access for some hundreds of thousands of systems. Home routers and IP-connected video cameras were exploited, but the public suffered. The attack vector focused on home consumer devices, items that typically aren’t really configured securely, or administrated professionally.

Security Affairs
SEPTEMBER 10, 2021
rc2, it was released in 2016, and was affected by at least two container escape issues. ” Palo Alto Networks researchers published a video PoC to show how an attacker could escape the container to get administrator privileges for the entire cluster. The version used by the ACI is v1.0.0-rc2, ” reported PaloAlto Networks.

Adam Levin
OCTOBER 2, 2020
Existing campaigns created prior to October 27 will still be allowed to run, but they will face content and placement restrictions, including a ban on editing or uploading videos, images, making adjustments to image captions, and the removal of the “Paid for by” disclaimer.

Krebs on Security
JANUARY 22, 2019
In July 2018, email users around the world began complaining of receiving spam which began with a password the recipient used at some point in the past and threatened to release embarrassing videos of the recipient unless a bitcoin ransom was paid. EARLY WARNING SIGNS.

Security Affairs
JANUARY 12, 2019
Gottesfeld published a video on YouTube calling Anonymous members for action and asking them support to launch a cyber attack against the Boston Children’s Hospital asking for the return of Justina Pelletier to her parents. The state of Massachusetts obtained the custody of the teen after a diagnosis of the Boston Children’s Hospital.

Security Affairs
DECEMBER 2, 2018
A video on the Rossiiskaya Gazeta government daily’s website showed a police officer explaining people waiting in line that the cable car would not reopen “for technical reasons.”. . . “However, a cyberattack forced all passengers to disembark the cable car only two hours after it opened, its operator said on Wednesday.”

Schneier on Security
MAY 15, 2018
A group of students from University of California, Berkeley, and Georgetown University showed in 2016 that they could hide commands in white noise played over loudspeakers and through YouTube videos to get smart devices to turn on airplane mode or open a website.

Security Affairs
APRIL 29, 2020
Matthew Keys is a former Reuters journalist who was convicted in October 2015 of supporting the Anonymous collective and that was sentenced to 24 months in prison for computer hacking charges in April 2016. Due to the COVID-19 pandemic, the probation officer recommended Keys remain out of custody pending during violation proceedings.

The Texas Record
SEPTEMBER 26, 2018
TSLAC’s state records management assistance has archived over 20 webinars (45 minutes each) including a 30-minute online introductory video and webinars on electronic records management, digital imaging, shared drive cleanup, emergency planning and more. Association of Intelligent Information Management (AIIM) has a webinar Oct.

The Guardian Data Protection
MARCH 20, 2018
In December 2016, while researching the US presidential election, Carole Cadwalladr came across data analytics company Cambridge Analytica, whose secretive manner and chequered track record belied its bland, academic-sounding name.

The Guardian Data Protection
JULY 10, 2018
Related: Revealed: 50 million Facebook profiles harvested for Cambridge Analytica in major data breach In December 2016, while researching the US presidential election, Carole Cadwalladr came across data analytics company Cambridge Analytica, whose secretive manner and chequered track record belied its bland, academic-sounding name.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content