Meet Ika & Sal: The Bulletproof Hosting Duo from Hell
Krebs on Security
JANUARY 8, 2024
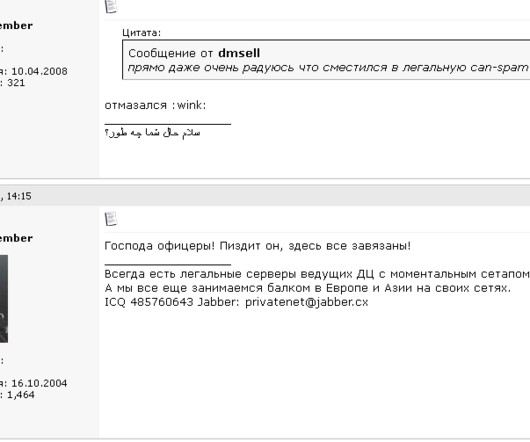
In 2020, the United States brought charges against four men accused of building a bulletproof hosting empire that once dominated the Russian cybercrime industry and supported multiple organized cybercrime groups. All four pleaded guilty to conspiracy and racketeering charges. The Spamdot admins went by the nicknames Icamis (a.k.a.














Let's personalize your content