Using Microsoft Powerpoint as Malware Dropper
Security Affairs
NOVEMBER 16, 2018
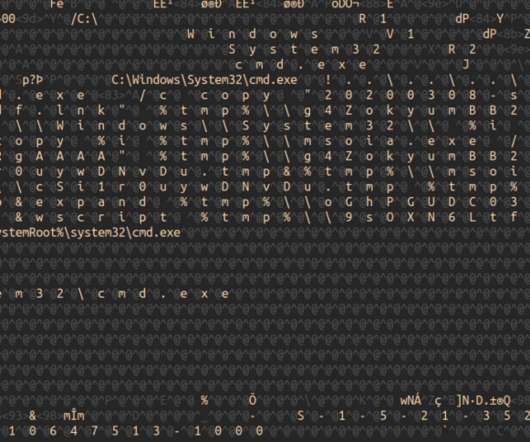
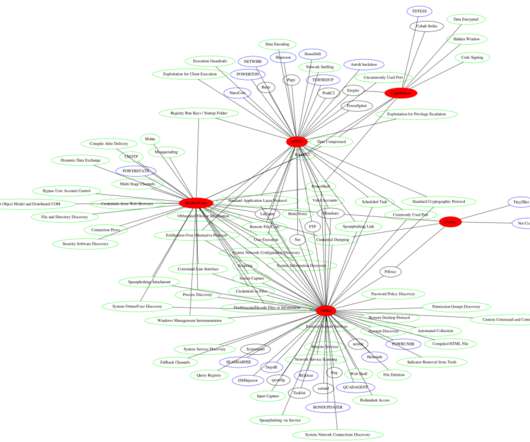
Marco Ramilli, founder and CEO at cyber security firm Yoroi has explained how to use Microsoft Powerpoint as Malware Dropper. The evidence comes from traffic analysis where the identified pattern sends (HTTP POST) data on browser history and specifically crafted files under User – AppData to specific PHP pages.


























Let's personalize your content