Spotlight Podcast: At 15 Cybersecurity Awareness Month Grows with Cyber Risk
The Security Ledger
OCTOBER 18, 2018
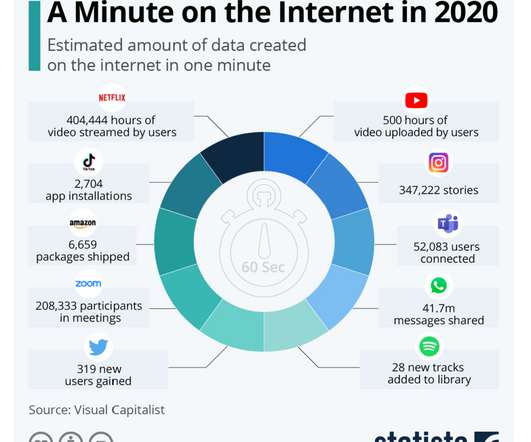
And this year is a special occasion: a Quinceañera of sorts recognizing 15 years since the first Cybersecurity Awareness Month in 2004. The Computers in our Pockets. Problems like cyber crime were predictable outgrowths of growing connectivity and convenience – from electronic banking to online retail, Angel Grant of RSA told me.













Let's personalize your content