SolarWinds Orion: Fixes Aim to Block Sunburst and Supernova
Data Breach Today
DECEMBER 29, 2020
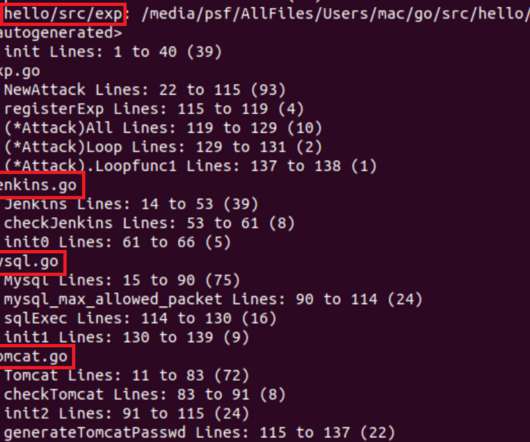
Both Strains of Malware Among Multiple Tactics Being Used by Supply Chain Attackers Software vendor SolarWinds has updated multiple versions of its Orion network-monitoring software to address the Sunburst backdoor that was added to its code, and to block Supernova malware that exploited a vulnerability in Orion. But incident response experts have warned that full cleanup may take years.


































Let's personalize your content