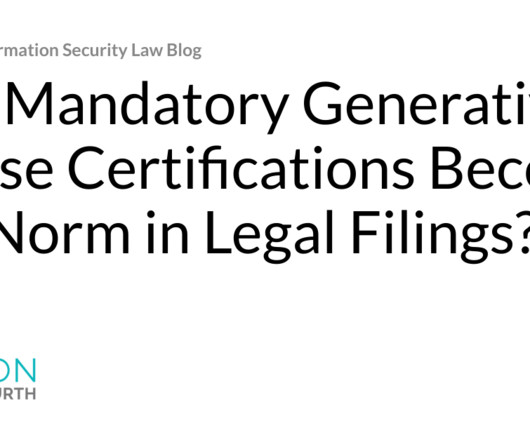
Microsoft Sets Aside $425M For Anticipated GDPR Fine
Data Breach Today
JUNE 3, 2023
Targeted Advertising on LinkedIn May Violate Europeans' Privacy Microsoft is warning investors it may receive a fine from European privacy regulators adding up to at least hundreds of millions of dollars over targeted advertising on its LinkedIn social network. European authorities have shown increased willingness to use the GDPR to limit targeted advertising.






































Let's personalize your content