Medical Transcriber's Hack Breach Affects at Least 9 Million
Data Breach Today
NOVEMBER 15, 2023
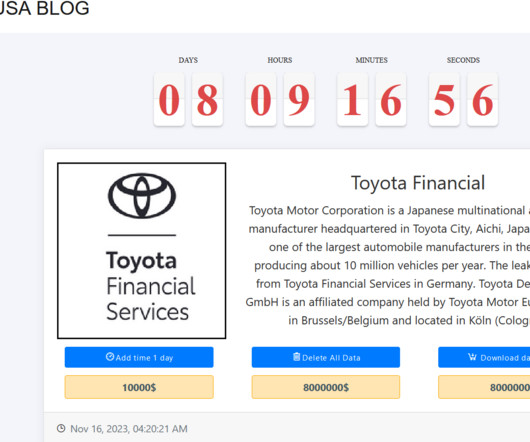
Northwell Health Among Perry Johnson & Associates' Healthcare Clients Affected The number of healthcare organizations and patients affected by a recent data theft at medical transcription firm Perry Johnson & Associates is expanding: The company now says the breach affected the sensitive information of about 9 million people.
































Let's personalize your content